Axios Codebook

July 28, 2023
😎 TGIF, everyone. Welcome back to Codebook.
- 🥵 Hope you're all finding a way to stay cool and beat the heat this week!
- 📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,578 words, a 6-minute read.
1 big thing: Public companies get a new cyber cop
Illustration: Allie Carl/Axios
The Securities and Exchange Commission has waved through a new, highly anticipated cybersecurity regime for public companies that requires them to publicly share the news of significant hacks.
Driving the news: The SEC voted Wednesday to approve new rules that require publicly traded companies to report "material" cyber incidents within four business days via a public 8-K filing and to share details about their overall cybersecurity strategies in an annual 10-K filing.
- The SEC spent more than a year deliberating the nuances of the rules and collecting feedback from cybersecurity professionals, companies and other stakeholders.
- The final product took many of the public's concerns into consideration, experts told Axios.
Why it matters: Public companies will soon have a standard for how best to report certain cyber incidents with their investors and shareholders.
- Under the SEC rules, companies will now have to report a cyber incident via an 8-K filing within four business days of determining the incident has had a material impact.
- Before, the obligation to report these incidents was a patchwork. Many companies shared details in 8-K forms already, but the amount of detail in those disclosures varied greatly.
What they're saying: "The commission and maybe the staff, too, noticed that although more cybersecurity disclosures were coming in some cases, it was very uneven," David Martin, senior counsel at law firm Covington & Burling LLP, told Axios.
- "Another principle around these rules was to try to get everybody on the same page," he added.
Details: The final SEC rules vary from the original, highly contested draft rules first proposed in March 2022.
- The final rules don't require companies to appoint someone to the board who has cybersecurity expertise. Instead, companies need to share details in annual reports about who on their management team oversees cybersecurity efforts and must detail any board committees that discuss cybersecurity issues.
- And the SEC added a new exemption for reporting incidents that pose a national security threat. However, only the U.S. attorney general can grant such an exemption.
Between the lines: Many of these changes were made after stakeholders expressed concerns that divulging too much about their cybersecurity systems early in the response process could leave them vulnerable to further attacks.
- However, some of those fears remain.
The big picture: Whether companies are already prepared for these rules largely depends on their size and existing cybersecurity investments, Kaylee Cox Bankston, a partner at law firm Goodwin Procter LLP, told Axios.
- "I don't know that I've spoken to any clients who are excited about the rules and say we really need this," Bankston said. "But some are certainly more prepared than others."
The intrigue: For a lot of companies, adhering to these rules most likely won't require too much additional spending, Matt Gorham, leader of the Cyber & Privacy Innovation Institute at PwC US, told Axios.
- Cybersecurity has long been a top investment for many publicly traded companies, Gorham said, and now they'll just need a plan in place for how to handle a public filing ahead of the next incident.
Yes, but: It's yet to be determined how the SEC rules will work alongside other government cyber reporting requirements.
- While the SEC determined that some requirements from the Federal Communications Commission should take precedence, the agency didn't cover the topic further.
- The Cybersecurity and Infrastructure Security Agency is currently in the rule-making process to determine how new reporting rules for critical infrastructure operators will go into effect.
- "It remains to be seen how much that harmonization will actually be able to occur between these various different regimes," Caleb Skeath, a cybersecurity-focused partner at Covington, told Axios.
What's next: Most companies will need to start complying with the 8-K requirements either within 90 days of publication in the government's Federal Register or by Dec. 18, whichever is later.
- The new 10-K requirements go into effect for fiscal years ending on or after Dec. 15.
2. Senator calls for probe in Microsoft breach
Illustration: Annelise Capossela/Axios
A top cybersecurity-focused senator is calling for the U.S. government to "hold Microsoft responsible for its negligent cybersecurity practices" after a recent cloud breach.
Driving the news: Sen. Ron Wyden (D-Ore.) sent a letter Thursday to the heads of the Justice Department, the Federal Trade Commission and CISA asking them to launch new inquiries into Microsoft's cybersecurity practices.
Why it matters: This marks the first lawmaker request to investigate Microsoft's cybersecurity strategies since the breaches were discovered earlier this month.
- Microsoft has been in the D.C. hot seat since the recent disclosure, given this isn't the first time suspected Chinese hackers have used Microsoft's tech to spy on government officials.
What they're saying: "Even with the limited details that have been made public so far, Microsoft bears significant responsibility for this new incident," Wyden writes in the letter.
Catch up quick: Earlier this month, Microsoft disclosed that a China-based hacking group had gained access to email accounts belonging to several government agencies.
- Reports have now suggested that those accounts included ones belonging to Commerce Secretary Gina Raimondo, the U.S. ambassador to China and a top State Department official.
- But questions still surround how the breach happened. Microsoft has said the hackers acquired an obscure account signing key, which they then used to forge identity authentication on user accounts. It's unclear how the hackers obtained that key.
Details: Wyden alleges that Microsoft likely failed to store "high-value encryption keys" in a recommended hardware storage vault that would have prevented the hackers from stealing it.
- Wyden also argues that Microsoft should not have had an encryption key that would allow people to authenticate other accounts in the first place.
Of note: The senator also placed some blame on the federal government for not detecting these alleged poor storage practices during federal procurement cybersecurity reviews.
Between the lines: Wyden is calling on several regulators to act.
- He's asking CISA director Jen Easterly to direct the Cyber Safety Review Board to investigate the July hacks and Microsoft's security practices around encryption keys.
- He's also calling on Attorney General Merrick Garland to examine whether "Microsoft’s negligent practices violated federal law."
- And he's urging FTC chair Lina Khan to investigate Microsoft's privacy and data security practices related to this incident.
The other side: "This incident demonstrates the evolving challenges of cybersecurity in the face of sophisticated attacks," a Microsoft spokesperson said in a statement.
- "We continue to work directly with government agencies on this issue, and maintain our commitment to continue sharing information at Microsoft Threat Intelligence blog."
3. How hackers are assessing the AI whirlwind
Illustration: Shoshana Gordon/Axios
A group of hackers participated in a level-setting conversation Thursday on how exactly they're seeing artificial intelligence impact cybersecurity — from the perspectives of both the threat side and the defense.
Here are a few of the takeaways I walked away with from HackerOne's online, media-only roundtable:
🔗 Generative AI presents the rare opportunity to build new products with security in mind.
- "We ignored security when we were creating networks, software applications and even in some cases programming languages as a whole, and we're still paying for that today," Gavin Klondike, a cybersecurity consultant and researcher for DEF CON's AI Village, said.
- "With the rise of LLMs and as a brand-new technology, we have the opportunity to start baking in software security and safety from the very beginning," he added.
🔌 GPT apps and browser plugins are where some of the biggest security and data privacy risks will lie.
- "It's a very large risk to plug together different tools or plugins with an LLM feature, even if it's internal only, if it's ever going to be processing untrusted data," said Joseph Thacker, who's known by the alias Rez0.
💼 AI will likely kill off some jobs — but probably not in the understaffed cybersecurity industry.
- "I see AI and being able to integrate AI into some of these systems as another opportunity to scale," Klondike said.
4. Catch up quick
@ D.C.
🏛 Lawmakers advanced the Kids Online Safety Act, a children's online safety bill that's worrying encryption supporters, to the Senate floor. (Axios Pro)
⛽️ The Transportation Security Administration revised its cybersecurity rules for oil and gas pipelines. (Cybersecurity Dive)
🚰 The water sector is showing mixed results in its progress toward becoming more cyber safe, according to newly obtained EPA data. (The Messenger)
@ Industry
💸 The Thales Group is buying U.S. cybersecurity company Imperva in a deal worth $3.6 billion. (Reuters)
👀 A Russian court sentenced Group-IB co-founder Ilya Sachkov to 14 years in prison after convicting him of treason. (Al Jazeera)
📲 Android phones can now alert users if an Apple AirTag is following them. (Ars Technica)
@ Hackers and hacks
🗂 U.S. contractor Maximus, which manages and administers certain government-sponsored programs, says at least 8 million people's data was stolen during a recent MOVEit-related data breach. (BleepingComputer)
🔎 NATO is investigating an apparent cyber incident after hacktivist group SiegedSec posted a link to more than 700 internal documents. (CyberScoop)
💔 CardioComm Solutions, a provider of heart monitoring tech, went offline due to a cyberattack. (TechCrunch)
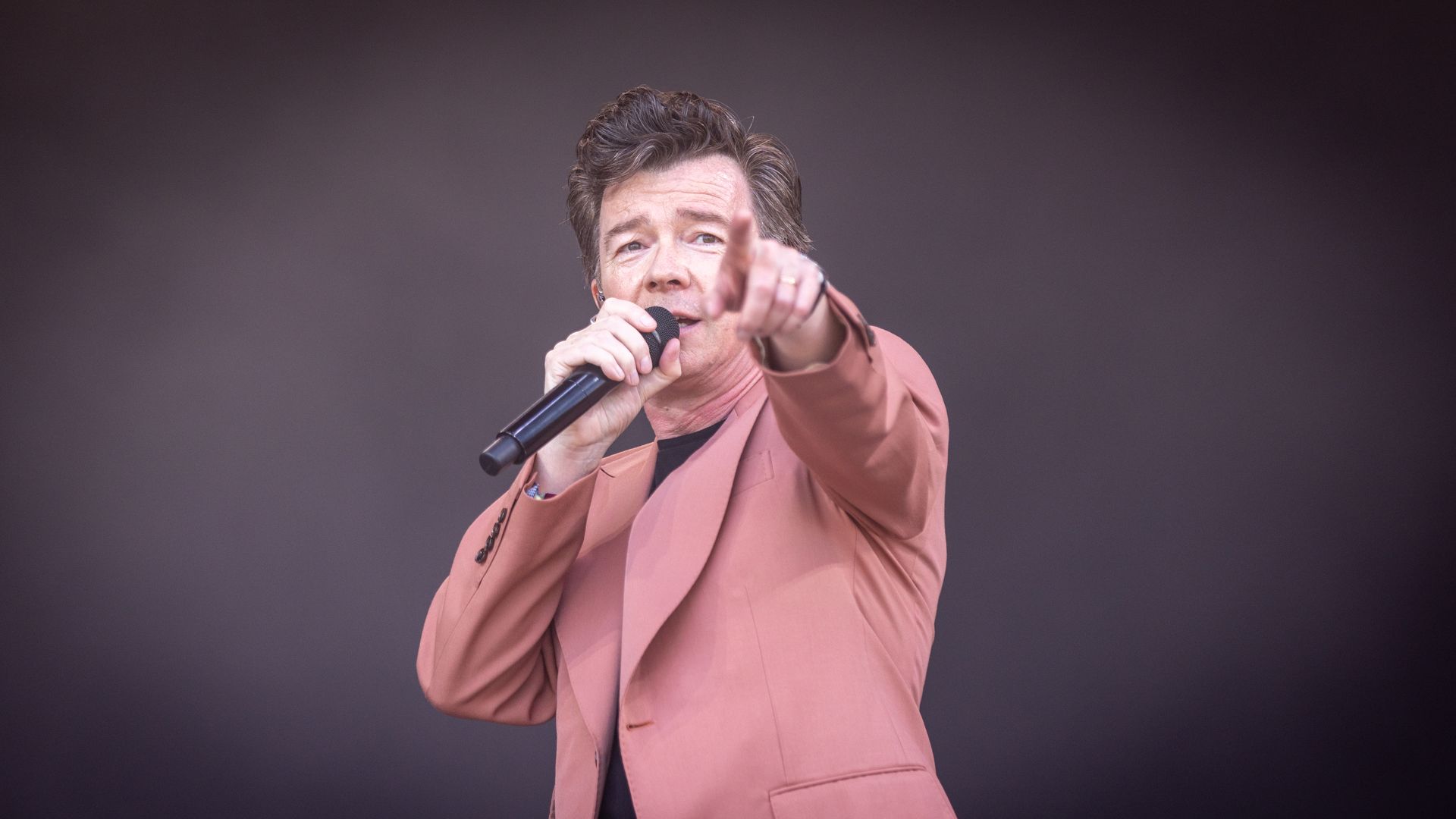
5. 1 fun thing
Rick Astley performs at the Glastonbury Festival in June. Photo: Matt Cardy/Getty Images
Even hackers have learned the art of the "Rickroll."
- Researchers at Sophos recently uncovered a new campaign that embeds malware into Google and Bing ads.
- But in their research, they found the malicious hackers had inserted a fun joke: Any time a user or researcher attempted to study the malware by typing the URL where it was hosted — instead of clicking on the ad — they were redirected to a video of Rick Astley's "Never Gonna Give You Up." 🎤
- In other terms, they get Rickrolled. Classic.
☀️ See y'all on Tuesday!
Thanks to Scott Rosenberg for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.