Axios Codebook

September 10, 2024
Happy Tuesday! Welcome back to Codebook.
- 🎃 Now that it's firmly September: What pumpkin-flavored beverages are we all trying this fall?
- 📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,062 words, a 4-minute read.
1 big thing: The Russian disinformation networks hiding in plain sight
Russian disinformation warfare is now more calculated and intentional than ever — as it employs more strategies that require hefty financial investments and long-term planning.
Why it matters: These new tactics make it much harder to decipher between a legitimate U.S. influencer posting about the election and a Russian operative posing as an American pundit.
Driving the news: The Department of Justice released several major indictments last week against Russian disinformation operatives and military hackers.
- Feds charged two employees of RT, a Russian state media network, with infiltrating a Tennessee-based online content company as part of a $10 million scheme to push the company to create content aligned with Russian interests.
- The DOJ also seized 32 domains tied to a Russian influence campaign that spread election disinformation and charged a former Trump 2016 campaign adviser with working for a sanctioned Russian television station.
- And the U.S. government identified a new Russian hacker team inside the GRU, an aggressive military branch known for plotting assassinations, bombings and coup attempts.
What they're saying: The schemes "make clear the ends to which the Russian government — including at its highest levels — is willing to go to undermine our democratic process," Attorney General Merrick Garland said last week.
Between the lines: Until now, much of the focus on Russia has centered on social media troll farm operators, phishing-based espionage campaigns and haphazard cybercriminal gangs.
- The new charges show how Russia has grown even more sophisticated in its disinformation operations, building on its advancements in the 2020 election.
Zoom in: Russia is now going as far as funneling millions of dollars into disinformation schemes that involve legitimate U.S.-based media outlets.
- According to the indictment, two RT employees — Kostiantyn Kalashnikov and Elena Afanasyeva — were hired by an unidentified Tennessee media company as editors and successfully published videos promoting Russian interests on TikTok, Instagram, X (formerly Twitter) and YouTube.
- The Tennessee company, which some outlets have identified as Tenet Media, launched in November and has since published nearly 2,000 videos that have garnered more than 16 million views.
- RT funded the operation by funneling money through several foreign shell companies. Tenet has not commented on the allegations.
The intrigue: One of Russia's longest-running disinformation campaigns, known as Doppelganger, has even evolved to start tracking American social media influencers, according to indictment documents.
- Investigators uncovered evidence that the Russian marketing agencies that run Doppelganger have maintained a list of more than 2,800 influencers they track for potential collaborations.
- In one piece of submitted evidence laying out a Doppelganger project, the marketing firms proposed working with social media influencers to fuel "internal tensions" inside U.S.-allied nations.
The big picture: In the last few years, Russian disinformation operatives have struggled to gain traction online.
- In December, Meta researchers said they had failed to find "any significant engagement from authentic social media users" from the Doppelganger network found on Meta's platforms.
- The new tactics — including infiltrating legitimate media sites and tapping unwitting American influencers — are now Russia's preferred way to boost engagement online, officials say.
What we're watching: The Russia-focused indictments could be the tip of the iceberg in an election season that's already been defined by AI-fueled disinformation and Iranian hacks on presidential campaigns.
2. Google Cloud's new plan to thwart ransomware
Google Cloud is offering a new feature to better protect data backups from persistent ransomware hackers.
Why it matters: Ransomware gangs have increasingly targeted companies' data storage backups, both by wiping them and by encrypting them, to entice victims to pay a hefty ransom.
Zoom in: Google Cloud is adding a new "backup vault" feature that will help administrators isolate their backups from company networks that any employee can access.
- The vault can be stored in a location that's inaccessible to most users — meaning attackers would need to find more than just an employee's username and password to access it.
- Administrators can also now lock backups so no one, including themselves, can shorten the lifespan of a backup or delete it before a certain number of days.
- And backup vaults can be stored in a separate location away from the cloud-based project they're supporting, meaning they can still be accessed even if a hacker wipes or encrypts the project.
Between the lines: Data backups are usually companies' only line of defense when faced with file-encrypting ransomware.
- Without them, companies can lose all access to their production information and sensitive data.
The big picture: Ransomware continues to thwart companies that fail to practice basic cyber hygiene, such as implementing multifactor authentication and updating default passwords on key devices.
- Payments to ransomware gangs have gone up in 2024, with the median payment landing at $1.5 million as of July.
What's next: Google Cloud will start previewing the new backup security feature later today, and the company will make it available to everyone in the coming months.
3. Catch up quick
@ D.C.
⚠️ Intelligence agencies in the U.S., the U.K. and other Western countries say Russian military intelligence hackers were behind cyberattacks on NATO and other European Union countries. (BBC)
👀 A top Department of Homeland Security official said yesterday that the Cyber Safety Review Board plans to unveil the subject of its next investigation "soon." (The Record)
🇮🇷 A network of at least 19 pro-Iranian fake news websites is spreading U.S. election disinformation that actively targets minority and veteran voters. (Politico)
@ Industry
🛡️ Microsoft is hosting a cybersecurity summit at its Washington state headquarters for government customers after the global IT outage in July. (Reuters)
📈 The cyber insurance market is likely to see strong growth in the next few years as hackers continue to target businesses, pricing stabilizes, and more insurers offer policies, according to a new Moody's Ratings report. (Cybersecurity Dive)
@ Hackers and hacks
🚗 Car rental giant Avis is notifying hundreds of thousands of customers that their personal data was compromised in an August cyberattack. (TechCrunch)
🏥 Wisconsin Medicare says that nearly 950,000 residents' personal data was compromised during a hacking campaign last year that targeted a vulnerability in the MOVEit file transfer program. (The Record)
4. 1 fun thing
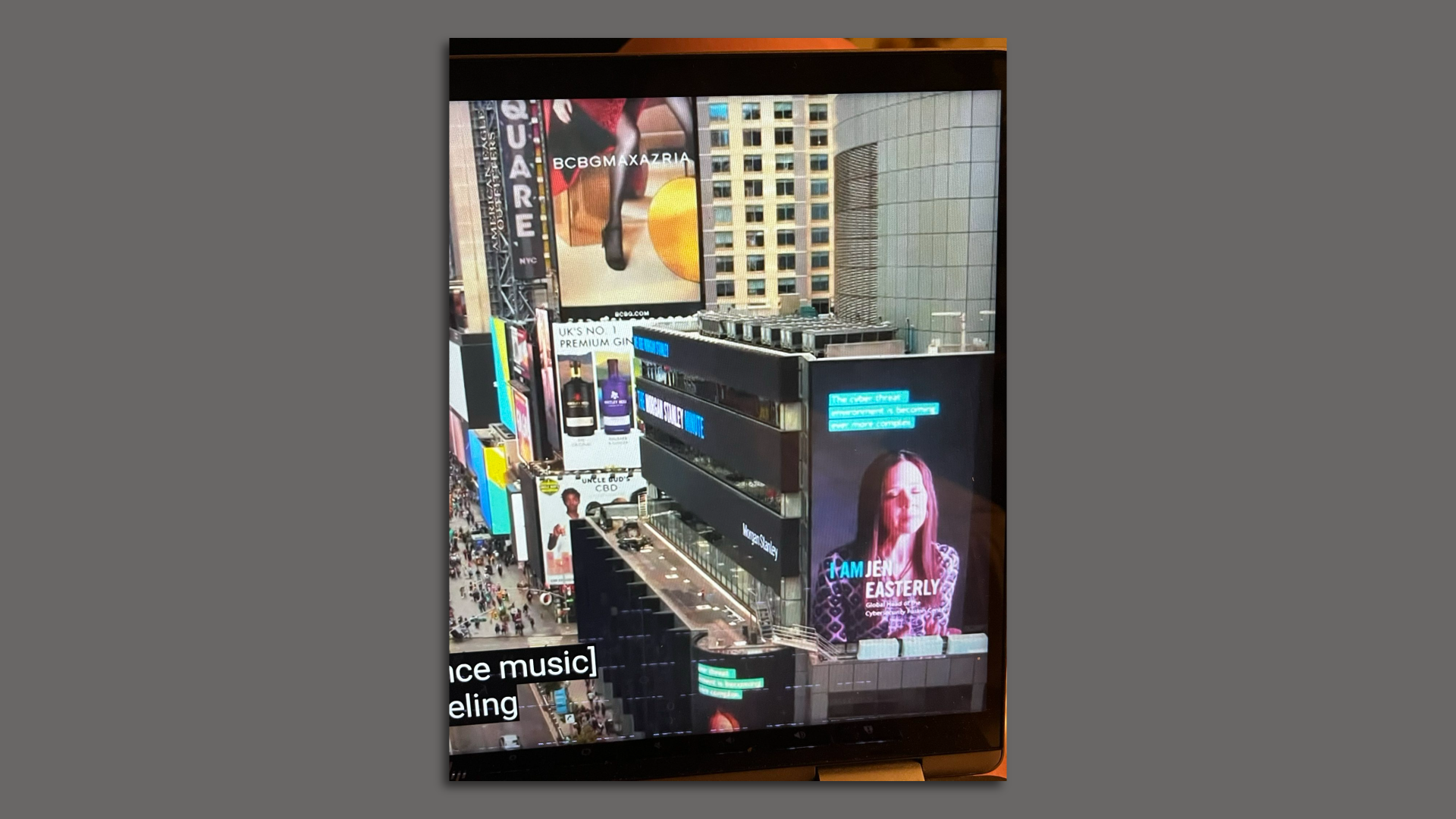
🏝️ This one is for my fellow "Love Island USA" fans: Did you also miss this Jen Easterly cameo in the opening sequence of the reunion episode?
- Seems one of CISA's public service announcements is playing in Times Square during the opening sequence. 👀 📺
- H/t to pal and Nextgov reporter Natalie Alms for finding it.
☀️ See y'all Friday!
Thanks to Megan Morrone for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook