Axios Future of Cybersecurity

March 11, 2025
🔮 Happy Tuesday! Welcome back to Future of Cybersecurity.
- 👋🏻 Hello from Las Vegas, where I'm attending the inaugural HumanX AI conference. Stay tuned later this week for my dispatch from the ground.
- 📬 Have thoughts, feedback or scoops to share? [email protected].
🚨 Situational awareness: President Trump has nominated Sean Plankey to be the next director of the Cybersecurity and Infrastructure Security Agency.
Today's newsletter is 1,537 words, a 6-minute read.
1 big thing: A new way to take down scammers
Visa has created an unprecedented scam detection initiative, built to both protect customers and dismantle the scammer ecosystem, the company shared exclusively with Axios.
Why it matters: Consumers lost more than $1 trillion to scams around the world last year, according to a report from Feedzai, but few resources exist to adequately fight back against the vast online scam ecosystem.
- Visa's approach could serve as a blueprint for other companies looking for ways to fight scammers.
The big picture: Like ransomware gangs, online scammers run vast, international operations — but instead of extorting corporations, they exploit individuals on a massive scale.
- Romance scams, phishing emails, and payment fraud are all part of the scammer ecosystem.
- Fraudsters are increasingly using generative AI to write convincing phishing emails, improve deepfakes, and draft new forms of malicious code — making scams harder to detect.
Between the lines: Law enforcement can't handle the volume of online scams, so private companies need to step up.
How it works: Visa's new scam detection practice is modeled after threat intelligence units inside cybersecurity companies, which proactively study and research threat actors to prevent new attacks.
- Visa has invested $12 billion over the last five years to improve its cyber, fraud, and risk tools. The scam disruption practice is part of that broader effort.
- The new practice includes an intelligence team that goes beyond Visa's own payment network and studies the dark web and social media to uncover scammers' actions, Michael Jabbara, senior vice president of payment ecosystem risk and control at Visa, told Axios.
- Visa also has a dedicated disruption team that partners with industry peers and law enforcement to shut down scam networks, including fraudulent merchant sites and scammers' financial accounts found on Visa's networks.
- Employees on the team come from a mix of backgrounds, including cybersecurity, fraud detection, data science, and law enforcement, Jabbara added.
What they're saying: "Consumers can only do so much, we need to also be there to protect them and help level the playing field a little bit," Jabbara said. "They're not going to stand a chance if you don't have folks who are standing behind their back."
The intrigue: Visa estimates its team, which it has been building over the last year, disrupted more than $350 million worth of attempted fraud in 2024.
Zoom in: Last year, the new Visa team took down roughly 12,000 merchant websites linked to a fake background-check scam on dating apps.
- Scammers posed as real people, built rapport, and then asked victims to run a background check before meeting.
- The fraudulent website signed victims up for recurring payments that often went unnoticed, Jabbara said.
- Visa found that the 12,000 fraudulent merchants were spread across more than 10 financial institutions and two continents. The company estimates this takedown prevented more than $27 million in victim losses.
- "We can actually find that needle in the haystack — but then we can connect that needle to all the other needles and all the other haystacks that are set up all around the world," Jabbara said.
Reality check: Visa has a vested interest in ensuring that fraud doesn't continue to target its customers or its own platforms.
- Every time customers' payments are returned, Visa incurs operational costs for the transactions and spends its own resources investigating the customers' claims.
- A high volume of fraud-related chargebacks can also make Visa's network look riskier, potentially leading to more regulatory scrutiny or pressure from financial institutions.
- By establishing itself as a leader in this space, Visa could benefit from stronger relationships with banks, merchants and regulators.
What's next: Over the next year, Visa is focused on expanding its intelligence gathering and speeding up scam takedowns. And the practice is investing more in generative AI and automation to scale its scam detection, too.
2. Just don't call it a hack — yet
X's string of outages yesterday look more like a classic DDoS attack than the hack some claim it to be.
Why it matters: Calling the attack a hack implies a wider impact — like stolen data or unauthorized access to sensitive systems.
- DDoS attacks are still serious, but they require a different response and typically have a more contained impact.
Catch up quick: Elon Musk said yesterday that X was facing a "massive cyberattack."
- Tens of thousands of users reported outages throughout the day, starting at 6am ET.
- Pro-Palestinian hacktivist group Dark Storm Team claimed responsibility on Telegram, according to Check Point Research.
- Musk also told Fox Business Network that the IP addresses tied to the attack originate "in the Ukraine area."
- Verifying that claim is impossible without access to X's systems.
What they're saying: Gen. Mike Flynn, a national security adviser during President Trump's first term, wrote on X: "Check to see if the CIA was acting behind the scenes first before going off on China or Russia please."
- Shawn Ryan, a former Navy SEAL and podcast host, said, "They hacked the wrong person," referring to Musk as a "tech genius who knows his stuff."
Yes, but: Other than Musk's confirmation that X is under attack, no technical details have been shared.
- And so far, the disruption resembles the DDoS attacks politically motivated hackers have been launching for decades.
The big picture: DDoS attacks flood websites with bot traffic, making them unreachable.
- They're effective for causing chaos and sowing distrust, but not for operations requiring stealth, like data theft or espionage.
What we're watching: Keep an eye out for new details from Musk and third-party cybersecurity researchers tracking Dark Storm Team and other hacktivist groups, who are able to study the networks those groups rely on.
3. Threat spotlight: Scammy domains
A new report, shared in advance exclusively with Axios, from BrandShield reveals a little of how scammy operators work.
Between the lines: The thinking seems to work like this: Identify a person or brand that lots of people are talking about, come up with something that you think people might buy associated with that brand, and throw up a quick website offering that thing.
- Oh, and two more parts. First, give them a way to pay for it. Second, don't send it. Don't even make it.
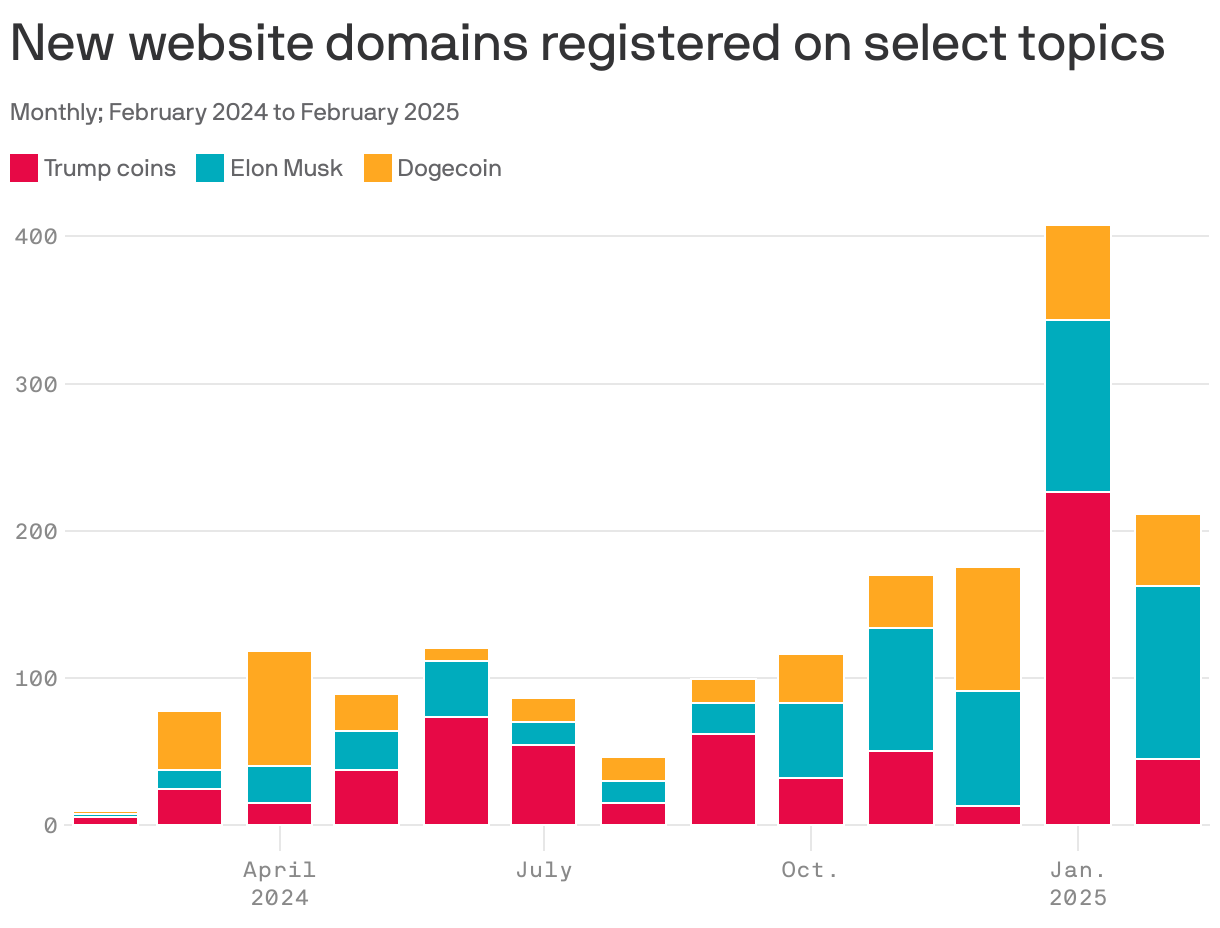
How it works: Folks come up with all kinds of ridiculous websites that touch on key brands. In the chart above, BrandShield found sites associated with the brand Dogecoin (which was first a jokey cryptocurrency, but now the brand is reshaping the federal government), Elon Musk and "Trump Coin."
- The last one is probably more limited because the Trump brand is just too big, but also Trump coins were a pretty big thing before President Trump offered a coin.
- Musk's brand seemed to drive the freshest inspiration for swindlers over the period studied.
Zoom in: Some of the scams seem so bad it's hard to believe anyone would fall for them, including:
- A CEO of Dogecoin and TSLA investment Facebook page, featuring an image of Musk as a clown.
- A Dogecoin faucet site offering free DOGE (bitcoin oldheads will tell you that there was once a bitcoin faucet, but that was long ago).
- Trump Coin Shop, which for some reason doesn't have a picture of Trump. It has images of aliens and flying saucers.
- The Ultimate Meme, that is $MUSK, which features Musk as a cartoon dog walking various Muppets.
- Super Trump Coin.
Reality check: All we know from the report is that these sites went up, not that anyone purchased anything from them.
4. Security tip of the week
Conference season is around the corner, so set up a personal VPN to enhance your privacy and security on the go, especially when using that free and often insecure Wi-Fi service offered at hotels, in airplanes, or at conference centers.— Kemba Walden, president of Paladin Global Institute
5. Catch up quick
@ D.C.
🇨🇳 The U.S. indicted 10 individuals and two Chinese government officials tied to several high-profile cyberattacks. (Axios)
🪙 International law enforcement seized Russian crypto exchange Garantex, which has long been popular with cybercriminals to launder funds. (Axios)
💼 President Trump says the U.S. is in talks with four groups about a potential TikTok deal. (TechCrunch)
@ Industry
🤖 Alibaba launched its own AI reasoning model that the company says rivals DeepSeek's capabilities. (CNN)
👀 In 2015, Meta was willing to create a new censorship system and hire a "chief editor" who would decide what content to remove from the platform in a failed attempt to bring Facebook to China, according to a new whistleblower complaint. (Washington Post)
💰 Chainguard, a security startup focused on open-source software development, is in talks to raise another $350 million, led by Kleiner Perkins, in a deal that would raise the startup's valuation to $3.5 billion. (Bloomberg)
@ Hackers and hacks
🔍 A look inside the Chinese government's nationwide operation — involving law enforcement, telecom companies, banks and other organizations — to keep scammers from targeting citizens. (Bloomberg)
🇷🇺 Several major chatbots have been seen recycling arguments made by a Russian disinformation network. (Axios)
🤷🏻♀️ The Federal Trade Commission has ended its case against MGM Resorts over its 2023 ransomware attack. (The Record)
6. 1 fun thing
If you ever find yourself outside Death Valley National Park, consider a pit stop at the abandoned mining town of Rhyolite.
- I saw a house built in 1906 using just glass bottles and mortar (seen above) and some funky art pieces! So fun.
☀️ See y'all next week!
Thanks to Megan Morrone for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity





