Axios Codebook

August 16, 2024
😎 TGIF, everyone. Welcome back to Codebook.
- 👋🏻 Codebook is off Tuesday while I'm on vacation. See y'all next Friday.
- 📬 Have thoughts, feedback or scoops to share while I'm off? [email protected].
Today's newsletter is 1,023 words, a 4-minute read.
1 big thing: Iran is now the biggest foreign threat to the 2024 elections
Iran, not Russia, is proving to be the biggest nation-state threat to the U.S. presidential election in November.
Why it matters: Russia and Iran have grown more brazen and hungrier in their attacks on the U.S. elections, officials say, and the final stretch of the presidential election could see even more chaos.
Driving the news: Google researchers released a report Wednesday confirming that Iran-backed hackers targeted both the Trump and Biden campaigns in a phishing attack.
- The FBI is actively investigating the Trump campaign's claims that Iran hacked its systems and is leaking stolen materials to U.S. news outlets.
The big picture: Foreign adversaries have a growing appetite for targeting the U.S. elections amid a tense geopolitical environment, Sean Minor, team lead for Recorded Future's influence operations research, said during a webinar this week.
- U.S. involvement in several high-profile global conflicts — including the war in Ukraine, tensions between China and Taiwan, and the Israel-Hamas war — has put a major target on the presidential race.
- Iran has started using influence operations to undermine the Trump campaign, the U.S. intelligence community warned last month.
Flashback: Iran has shown a growing interest in targeting former President Donald Trump and the U.S. government since January 2020, when a U.S. airstrike killed Iranian Gen. Qasem Soleimani.
- During the 2020 presidential election, two Iranian hackers stole confidential U.S. voter information from at least one election website and posed as members of the Proud Boys to send threats to Democrats, according to indictment documents.
- And in 2022, Iranian hackers were seen using similar tactics to target voters in the month before the November elections, according to an FBI alert.
The intrigue: Iran now appears to be following the playbook Russia crafted in 2016 for targeting a U.S. presidential campaign, James Turgal, a former FBI assistant director, tells Axios.
- "It is almost an exact blueprint of what the Russians were doing in 2016," says Turgal, who is now the vice president of cyber risk at Optiv.
- And Iran has been working more closely with the Russian government since the invasion of Ukraine more than two years ago — suggesting they could have traded notes.
- "That's not a coincidence that we're now seeing really active cyber actions and cyber threats that mirror Russian [tactics]," Turgal says.
Threat level: Iran is known for a loud, chaotic style of foreign interference that typically doesn't emerge until the last month of the U.S. election cycle.
- But both the killing of Soleimani and Trump's years-long-run as the presumptive GOP presidential nominee gave Iran more time to prepare and pursue a more sophisticated hack-and-leak approach, similar to Russia's.
What we're watching: None of the publications that received apparently leaked Trump campaign materials have published them. Officials also haven't confirmed that Iran was behind those leaks.
- But if Iran was behind the leaks, their hackers will likely be motivated to find other means to publish the documents, Turgal says.
- "Strap in tight because it's going to get weird."
2. Ransomware on track for highest-grossing year


Ransomware costs have ballooned for victims in 2024 as malicious hackers have targeted higher-value companies more likely to pay a large sum to unlock their systems.
Why it matters: As long as ransomware keeps paying, hackers will keep using this technique.
By the numbers: Chainalysis said in a report yesterday that it's detected what it believes is the largest ransomware payment ever — $75 million that went to the Dark Angels gang this year.
- That number is roughly double the highest payment of 2023, which was $37.8 million.
- The median ransom payment has also skyrocketed: In early 2023, it was $200,000. As of mid-June 2024, it was $1.5 million.
Driving the news: Late last month, cybersecurity company Zscaler indicated that a Fortune 50 company had made the $75 million payment.
- Earlier this year, UnitedHealth's Change Healthcare paid $22 million to unlock its systems after a debilitating ransomware attack — and also to keep hackers from publishing stolen information online.
The big picture: Ransomware gangs have been demanding larger payouts, while also targeting fewer high-profile victims, Chainalysis noted.
- The tactic — known in the industry as "big game hunting" — primarily leans on hackers targeting critical life services like a hospital or larger businesses that may be more likely to pay up to bring their services back online.
Between the lines: Ransomware has proven to be a difficult problem for law enforcement and government officials to squash.
- Despite law enforcement takedowns, new hacker groups keep cropping up.
- And breaking into companies is still relatively easy, with more hackers gaining access simply by stealing an employee's password.
3. Catch up quick
@ D.C.
🗳️ Hackers at the DEF CON Voting Village found security flaws in widely used voting machines — and while a disruptive hack is unlikely, experts worry the bugs will be used as fodder among those who wrongly think the election is not safe. (Politico)
🇨🇳 Two House lawmakers are requesting that the Commerce Department open a probe of national security risks tied to routers from Chinese manufacturer TP-Link Technology Co. and its affiliates. (Reuters)
@ Industry
👨🏻⚖️ Google opens up about its new legal strategy to stop hackers and scammers: Sue them. (Wired)
💰 Tech investors Insight Partners and Sixth Street Partners are providing cybersecurity company Kiteworks with $456 million in funding. (Wall Street Journal)
👀 Meta has officially shut down CrowdTangle, a tool that gave researchers and journalists the ability to monitor how information was shared on its social media sites. (NPR)
@ Hackers and hacks
⚠️ Columbus, Ohio, residents' data is now at risk after a ransomware attack on the city's servers last month. (Axios Columbus)
💪🏻 DEF CON has launched a program to match volunteer hackers with under- resourced critical infrastructure organizers to help bolster their security. (NBC News)
🚔 Kim Dotcom, who is facing criminal charges tied to file-sharing website Megaupload, will be extradited to the U.S. (Reuters)
4. 1 fun thing
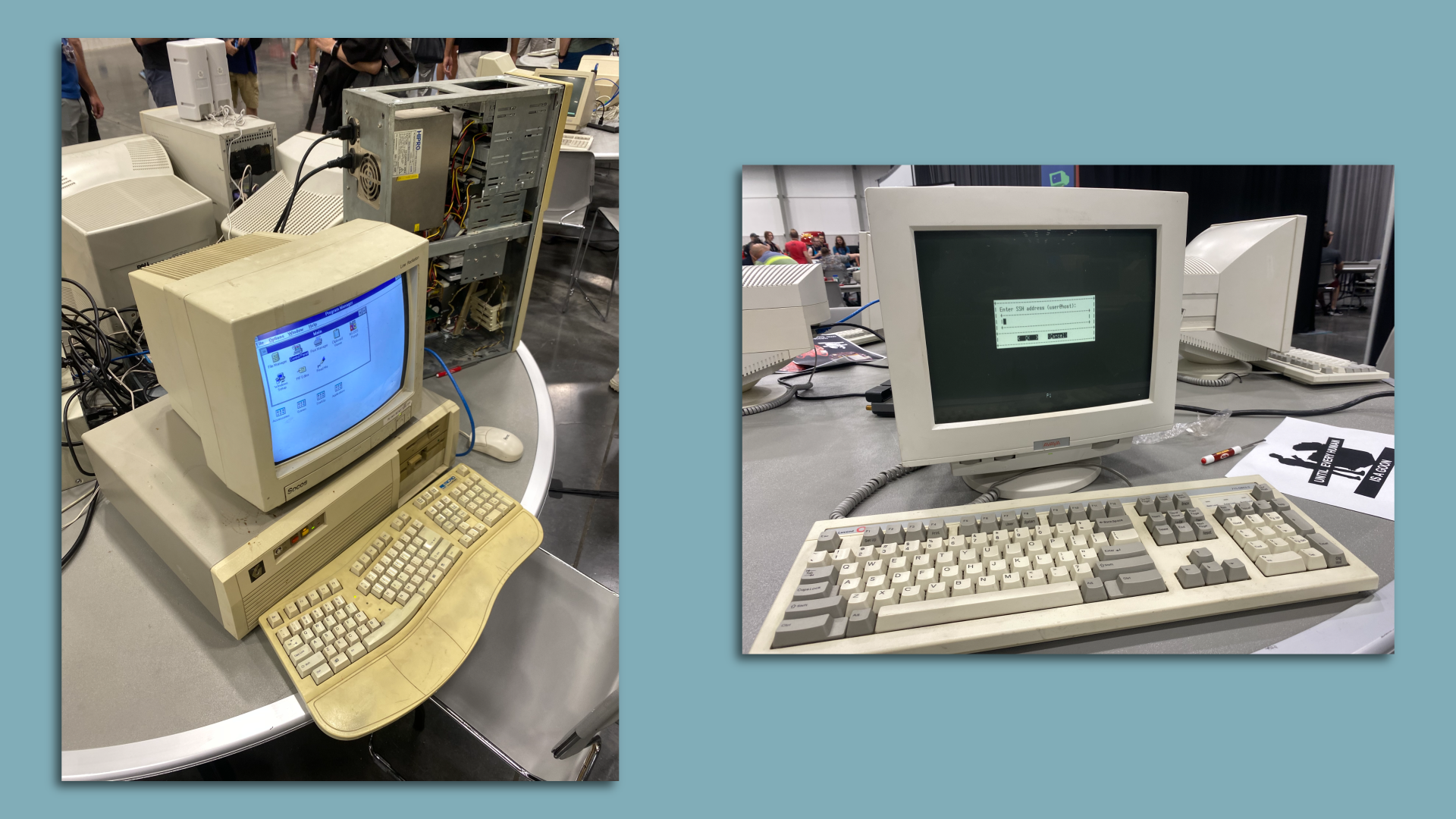
DEF CON hosted a Retro Technology Village last weekend that forced me to feel my age — rude!
- The village was exactly what it sounds like: Tables filled with old Macintoshes and Avaya computers, a row of Dell laptops running Windows 98, and a working, old-school projector. Time flies!
☀️ See y'all next week!
Thanks to Megan Morrone for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook