Axios Codebook

May 14, 2024
Happy Tuesday! Welcome back to Codebook.
- ☕️ Hope all you sleepyheads still recovering from the RSA Conference are awake and ready to dive back into reality.
- 📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,514 words, a 5.5-minute read.
1 big thing: Slow road out of the ransomware ward
It can take weeks, if not months, for organizations to recover from ransomware attacks.
Why it matters: Even if a ransom is paid, it takes time to detangle the mess that file-encrypting malware makes of servers.
Driving the news: Ascension, a medical provider that includes 140 hospitals across 19 states, has been experiencing a ransomware attack for nearly a week now.
- Hospitals started diverting ambulances to nearby facilities on Thursday and rescheduling nonemergency procedures.
- So far, Ascension has not said when services will return to normal.
The big picture: This story is a familiar one. A lot of organizations believe they can restore their systems using a backup and return to normal operations within a couple days.
- But untangling the encryption on key servers can take weeks even after securing a decryption key. Sometimes the decryption key that hackers send doesn't work as well as advertised.
- Incident responders also need to conduct a thorough forensic analysis to understand the extent of the attack, how it started, and what data may have been stolen before restoring the systems.
- Even switching over to backup servers can take time as specialists test to make sure the servers don't have the same vulnerabilities that led to the ransomware attack to begin with.
Between the lines: Victim organizations have two options when faced with ransomware: pay a high-dollar fee to the hackers to receive a decryption key or restore operations using a backup data server.
- Neither option guarantees a speedy recovery.
By the numbers: 34% of organizations that faced ransomware in 2023 took more than a month to recover, according to Sophos' latest State of Ransomware report.
- That's up from 24% who said the same in last year's survey.
Zoom in: Ascension confirmed Monday it's in the early days of a ransomware attack, and CNN reports it's battling the Black Basta ransomware gang.
- Patients have reported long delay times in care during the first days of the cyberattack.
- One doctor told Michigan Public radio that it took 90 minutes to get test results back for a woman who was in cardiac arrest. The test normally takes just 15 to 20 minutes.
- A patient told 7 News Detroit that he checked himself out of the emergency room after two days because doctors, who were relying on paper records, forgot to check on him.
Ascension isn't alone. Chicago's Lurie Children's Hospital faced service disruptions for a little over a month after fighting a ransomware attack earlier this year.
- Change Healthcare, a unit of UnitedHealth Group, took weeks to get payments processing back up after its attack despite paying a ransomware gang a $22 million ransom.
The bottom line: The best response to a ransomware attack is proactive defenses.
- A U.S. government advisory released Friday advised cyber defenders to install security updates as soon as they're available, require multifactor authentication, and provide phishing training to employees.
2. Wiz leans into cyber M&A strategy
Wiz, a New York cybersecurity company that's seemingly become a large player overnight, is not shy about acquiring its way to success.
Why it matters: Few venture-backed companies openly raise merger-and-acquisition war chests.
Driving the news: Last week, Wiz announced $1 billion in new venture funding at a $12 billion valuation, which included a small secondary transaction for early employees and investors.
Catch up quick: The company was founded in 2020 by Assaf Rappaport, Yinon Costica, Ami Luttwak and Roy Reznik after they left Microsoft. The four had landed at the tech giant in 2015 after it acquired their prior startup, Adallom, for $320 million.
- Wiz quickly set about winning over large enterprises as customers, achieving $100 million in annual recurring revenue in 18 months (it hit $350 million this year).
- It previously raised $900 million in funding from blue chip investors like Index Ventures, Sequoia Capital, and Insight Partners.
The big picture: Although Rappaport says he doesn't feel pressure from his investors to make any further acquisitions, M&A is a big reason for the large pile of cash his company just raised.
- It has already acquired two companies — Rafft and Gem Security — spending about $400 million, per reports.
Inside the room: Wiz is very intentional about its post-acquisition approach.
- "What we're doing is we're almost sunsetting the existing product in order to rebuild it into the Wiz technology stack to make sure that everything is coherent," Rappaport tells Axios.
Yes, but: Inevitably, some prospective deals have not come to fruition, notably Sutter Hill Ventures-backed Lacework and publicly traded SentinelOne.
- Lacework has raised $1.8 billion in funding and was last valued at $8.3 billion. Wiz made an initial offer of about $160 million before revising it down to less than $100 million, following a few weeks of diligence, according to a source familiar with the discussions.
As for SentinelOne, Wiz considered a bid but walked away after details leaked to the press, according to the source. SentinelOne told Axios there was never a deal, or any discussions of a deal, between the parties.
What's next: Wiz wants to build out an actual corporate development team to focus on M&A and investments, and it wants to start checking things off the list for an eventual IPO, like hiring a CFO — and hitting $1 billion in annual recurring revenue.
- "We're a 4-year-old toddler as an organization," Rappaport says.
3. Commerce moves to secure internet traffic
The Commerce Department has started implementing new internet routing security measures to fend off nation-state hackers and other malicious cyberattacks.
Why it matters: Improving the department's internet security can keep hackers from spoofing government domain names, stealing data flowing over these networks, or hijacking traffic going to legitimate government websites.
Zoom in: A handful of Commerce Department offices have signed new Route Origin Authorizations (ROAs) — cryptographic certifications that prove a website is legitimate and validate web traffic flowing through it.
- The Bureau of Economic Analysis, the Bureau of Industry and Security, the International Trade Administration, and the National Telecommunications and Information Administration (NTIA) are each implementing the new routing protocol.
- The National Oceanic and Atmospheric Administration — along with each of the researchers, scientists and partners on the office's N-Wave network — had already moved to these procedures.
- The NTIA worked with the American Registry for Internet Numbers and other groups to determine the tools needed and best practices for transitioning to this routing protocol.
Driving the news: The implementation plan for the Biden administration's national cybersecurity strategy urged agencies to increase adoption of secure internet routing technologies.
The big picture: Implementing these routing protocols requires manpower, money and resources that some government offices and businesses don't have, Commerce officials told Axios.
- Both the private and public sectors have historically lagged in implementing strong routing security measures, Alan Davidson, administrator for the NTIA, told Axios in an exclusive interview.
Inside the room: The Commerce Department hosted a small, internal ceremony Monday where the bureaus signed their ROAs, Davidson told Axios.
- Federal CISO Chris DeRusha and officials from the White House's National Security Council attended the event.
What they're saying: "A lot of people think of us as the department of business, which we are, but we're also the department of data and science and people and communities," Don Graves, deputy secretary of commerce, told Axios.
- "In order for us to ensure the safety and security of all of those things ... it's absolutely imperative for us to implement this model contract ourselves."
What's next: The Census Bureau and the National Institute of Standards and Technology are working on signing their own ROAs, Graves said.
- Commerce has also developed a model procurement contract that other agencies can work from to develop the same routing security measures.
4. Catch up quick
@ D.C.
🇺🇸 The U.S. and China are meeting in Geneva today to discuss AI safety and risk issues. (Axios)
🛰️ China, Russia and other foreign adversaries are increasingly looking to disrupt American space assets, a top Department of Defense official warned. (Nextgov/FCW)
🗳️ AI and other advanced technologies are supercharging threats against election workers, Department of Justice officials warned. (Axios)
@ Industry
🦾 OpenAI is rolling out a new flagship model, GPT-4o, that has advanced voice capabilities. (Axios)
👀 Amazon Web Services CEO Adam Selipsky is stepping down from his role, and long-time company executive Matt Garman is set to take his place. (Axios)
🤖 A look at the roughly 40 startups now advertising tools that can detect AI-manipulated media despite a lack of research into their methods. (Washington Post)
@ Hackers and hacks
⚠️ Federal officials warned that the Black Basta ransomware gang has breached more than 500 organizations worldwide. (BleepingComputer)
📲 Cybercriminals are increasingly targeting older people to steal their one-time passcodes and SIM-swap their phones. (TechCrunch)
🖼️ Hackers took down auction house Christie's website days before it was expected to sell as much as $840 million worth of art. (New York Times)
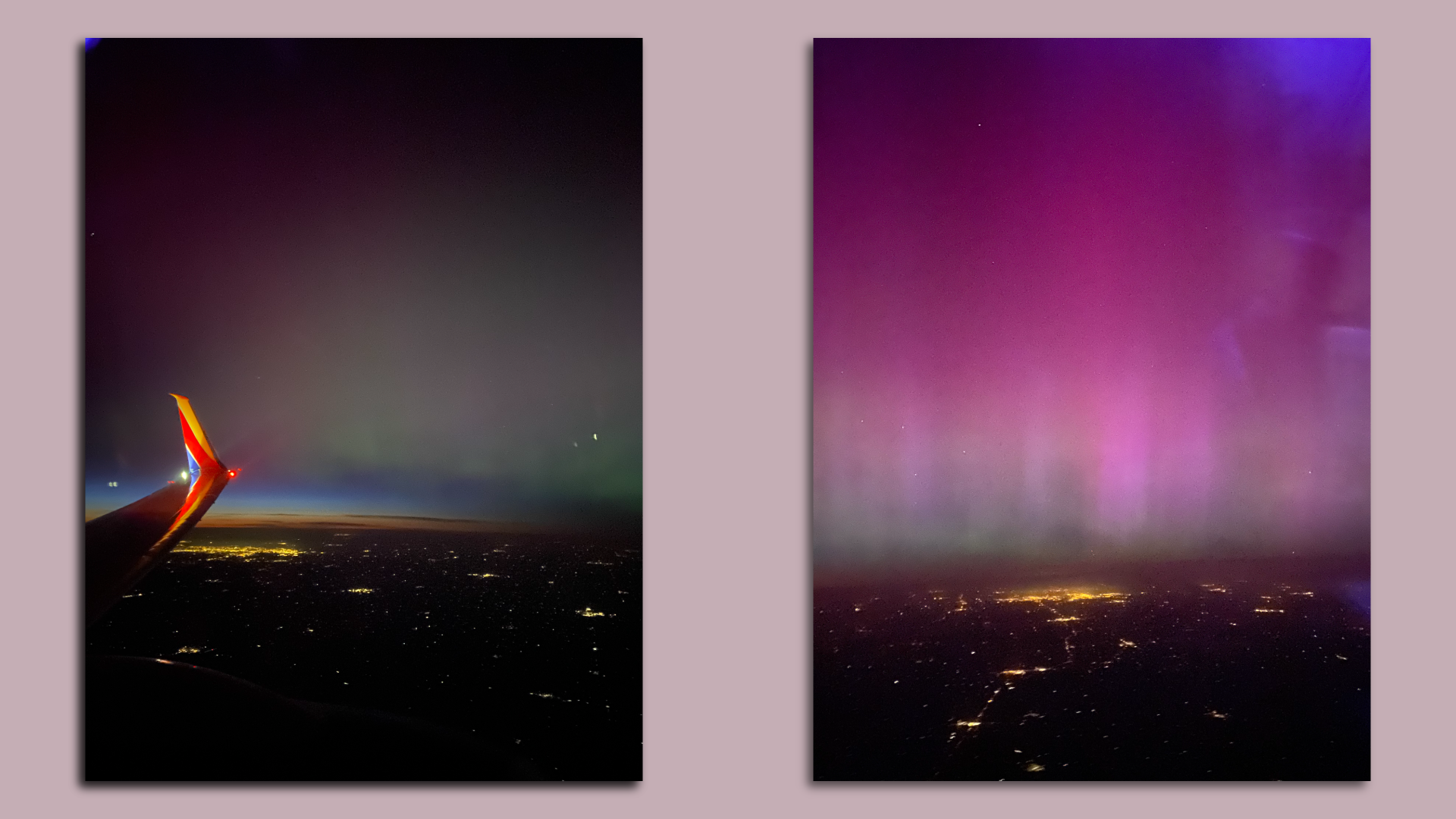
5. 1 fun thing
🌟 I was pretty stressed about taking such a late flight home from the RSA Conference last week — but the universe made the trip worth it!
- 🤖 I should also add: I promise these photos weren't AI-generated.
- 📸 Did you also get to see the northern lights over the weekend? Reply with your pics.
☀️ See y'all Friday!
Thanks to Megan Morrone for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook