Axios Codebook

August 23, 2024
😎 TGIF, everyone. Welcome back to Codebook.
- 🥰 It feels good to be back! What did we miss?
- 📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,365 words, a 5-minute read.
1 big thing: The hacker blame game isn't working anymore
Publicly pointing the finger at foreign adversaries' hackers doesn't hold the same power that it used to.
Why it matters: Attributing nation-state hacks has long been one of the few tools the U.S. government had to deter adversaries in China, Russia, Iran and North Korea from coming after American officials and companies.
The big picture: That no longer seems to be the case — as Iran continues to ramp up attacks on the U.S. elections, China burrows into U.S. critical infrastructure networks, and Russian ransomware gangs rake in more cash from U.S. companies.
- "You know it's them, and they know you're not going to do anything, so it really doesn't have any effect," James Lewis, director of the strategic technologies program at the Center for Strategic and International Studies, told Axios.
Driving the news: The intelligence community formally pinned the blame on Iran on Monday for a set of cyberattacks targeting the Trump and Biden-Harris campaigns.
- The joint statement from the FBI, the Office of the Director of National Intelligence, and the Cybersecurity and Infrastructure Security Agency marked one of the quickest attributions that the U.S. government has made in cyberspace, coming in just a little over a week.
Flashback: Historically, the U.S. government has taken several months to publicly blame a nation-state for spying and hacking officials, political parties or similar organizations.
- In 2016, it took the Obama administration about three months to formally blame Russia for hacking the Democratic National Committee and Hillary Clinton's presidential campaign.
- In 2021, the Biden administration didn't formally attribute a massive hack of Microsoft Exchange servers to Chinese government spies for four months.
Yes, but: The U.S. government and private sector have since developed better analysis tools and partnerships for these investigations — speeding up the process for them to pin the blame on an adversary.
Between the lines: Attribution of nation-state attacks is now more important for getting allied nations on board for retaliatory sanctions and joint law enforcement investigations, Lewis said.
- Smaller nations typically want to be certain that a specific adversary was behind an attack before they take action against them for fear of facing a major attack on their own networks, he added.
- The U.S. government also needs to attribute an attack to pursue sanctions or indictments.
- And attributing an attack tied to election infrastructure, especially in the 2024 cycle, is important for assuaging any potential disinformation about the security of the voting process, David Kennedy, the CEO at TrustedSec and a former NSA hacker, told Axios.
The intrigue: Attribution, sanctions and even indictments are no longer enough, experts said, but the U.S. government and its allied nations have yet to come up with an alternative.
- "At the end of the day, Iran is largely going to go unpunished for this," Kennedy said. "It makes no sense for Iran to stop."
What we're watching: Experts said the ongoing war in the Middle East — and Iranian threats to attack Israel — might deter the U.S. from pursuing stricter sanctions.
2. Government recruits a team to stress-test AI
A new government-supported program is actively recruiting people who want to help evaluate AI-enabled office productivity software.
Why it matters: Stress-testing generative AI tools is still one of the best ways to root out biases or false information in responses, as well as privacy concerns like responses that leak sensitive information.
Zoom in: Humane Intelligence, an AI ethics nonprofit, is teaming up with the National Institute of Standards and Technology to launch a new competition to find flaws in AI office productivity tools.
- The first round of the competition is virtual, and anyone in the U.S. who is interested in red-teaming AI models is welcome to participate.
- In this round, participants will run through a set of test scenarios and try to identify as many "violative outcomes" as possible.
- Those who pass this round will be invited to participate in an in-person red-teaming exercise in late October at the Conference on Applied Machine Learning in Information Security in Arlington, Virginia.
The intrigue: Humane Intelligence is also inviting genAI model operators to donate access to their models for testing.
- Qualifying products must be used for workplace productivity — such as coding, process automation and similar activities — and the operators must be willing to have their models tested for a variety of issues.
Between the lines: This new competition is just one of the challenges that Humane Intelligence is launching with government partners and NGOs in the coming weeks, the nonprofit told Wired.
- Humane Intelligence sees these competitions as a way of engaging people with a variety of backgrounds, not just coders, in AI red-teaming.
What's next: Those interested in participating in the first round have until Sept. 9 to sign up.
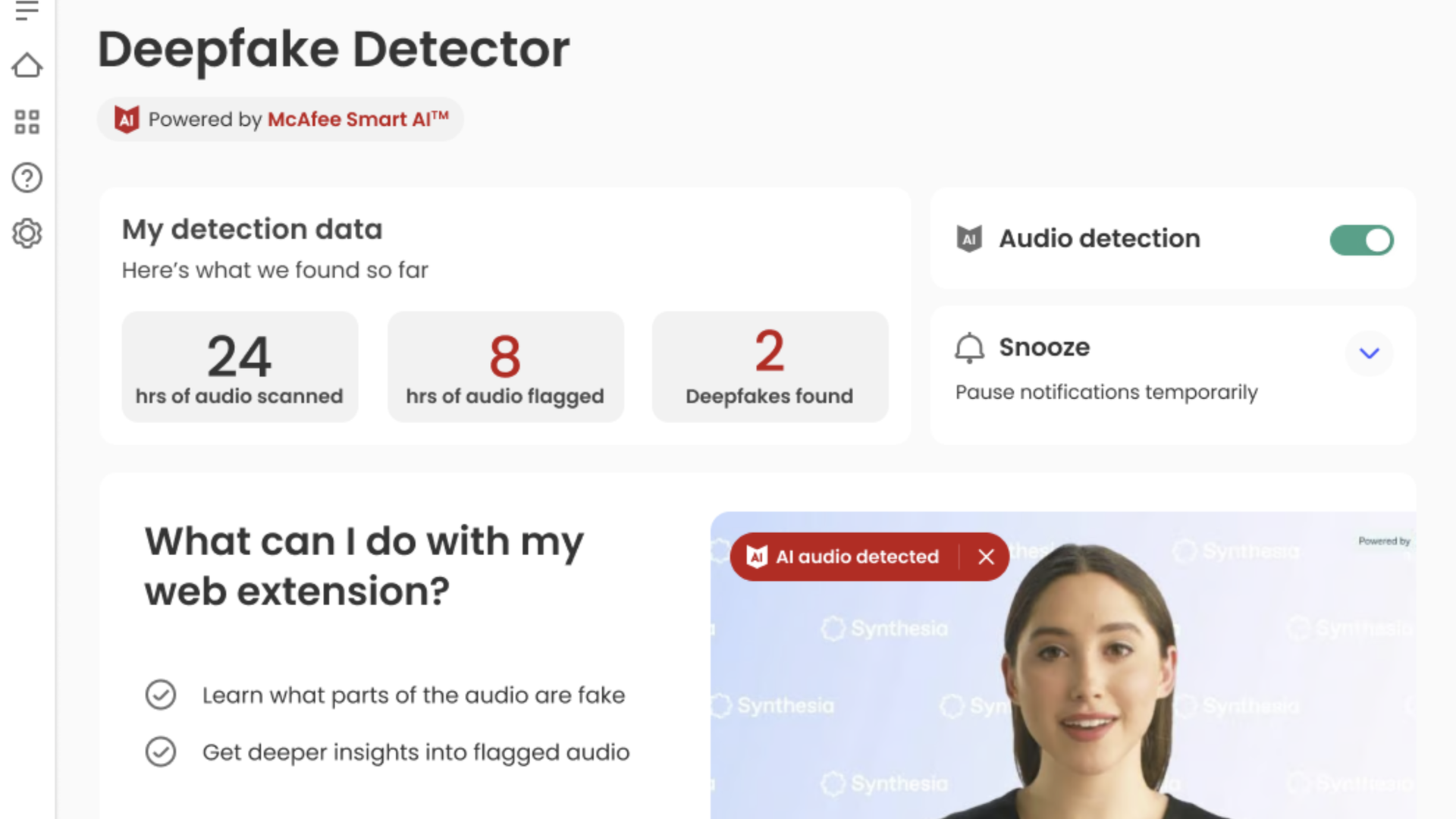
3. New McAfee tool can detect AI-generated audio
McAfee launched a new tool that helps users figure out whether the audio they are listening to in a video on YouTube, X or any other service is real or a deepfake.
Why it matters: AI companies have released a growing array of tools to generate content, but products that can tell you with any reliability whether content was made with AI remain rare.
How it works: The McAfee Deepfake Detector, as the new software is known, focuses on detecting AI-generated audio within almost any audio or video stream available on a PC.
- When AI-generated audio is detected, McAfee's software throws up a red icon. If a user clicks on it, the program offers additional details about the audio in question.
- Deepfake Detector doesn't work on content protected with digital rights management, but that content usually comes from big studios or other large companies.
What they're saying: "The barrier to create AI-generated content has come way down, and consumers don't really have great tools to know whether what they're looking at is potentially generated with AI," McAfee chief technology officer Steve Grobman told Axios.
Yes, but: Deepfake Detector does its work not in the cloud but on a user's computer.
- In today's AI software, that approach is typically reserved for tasks in which protecting the privacy of user data is a priority.
Between the lines: Grobman said McAfee is also looking ahead toward other kinds of AI scans that might be more sensitive.
- He noted that malware detection could benefit from scanning a wider array of the content someone sees and interacts with. But uploading all that data to the cloud for processing could violate user privacy and demand an impractically high level of bandwidth.
- "We can do a better job by having our analysis look at all the content, but we'd want to do that on device," Grobman said. "Doing everything in the cloud is just not practical; if you can do things locally, you can do it much more efficiently."
What's next: The McAfee tool will be available exclusively on Lenovo Copilot+ PCs through mid-September. McAfee said it expects to make the tool available on other PCs after September.
4. Catch up quick
@ D.C.
🤖 AI images created during the presidential election cycle have mostly just become another meme style, rather than a believable-looking source of information that experts feared. (Axios)
🏛️ A group of software and tech advocacy organizations are calling on Congress to pass legislation that could improve the way federal agencies make software purchases. (FedScoop)
@ Industry
👀 A CrowdStrike executive says the company was never in real talks to acquire patch management firm Action1 — despite reports from Action1 itself that it was considering a deal from the major industry player. (SecurityWeek)
📆 Cisco says it's planning to cut 7% of its workforce, but employees won't know if they're affected until next month. (TechCrunch)
@ Hackers and hacks
⚠️ U.S. chipmaker Microchip Technology said a cybersecurity incident involving an "unauthorized party" has disrupted some of its servers and business operations. (Reuters)
🛢️ Oil giant Halliburton confirmed this week that it's responding to a cyberattack on its systems. (CNN)
🚔 The Department of Justice has indicted an alleged member of the Karakurt ransomware gang for money laundering, wire fraud and extortion. (BleepingComputer)
5. 1 fun thing
If you live in D.C. (like me), most of the people you know were either in Chicago for the Democratic National Convention or in London for Taylor Swift this week.
- I think we all can guess where I was 😎.
☀️ See y'all Tuesday!
Thanks to Megan Morrone for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook