Axios Codebook

May 17, 2024
😎 TGIF, everyone. Welcome back to Codebook.
- 🎶 Happy Billie Eilish release day to all my fellow pop girlies!
- 📬 Have thoughts, feedback or scoops to share? [email protected]
Today's newsletter is 1,564 words, a 6-minute read.
1 big thing: Defense contractors have a long way to go on cybersecurity
Most defense contractors believe they're too small and inconsequential for nation-state hackers to target them, a National Security Agency official told Axios.
Why it matters: China, in particular, has been laser-focused on targeting key American critical infrastructure, officials have warned.
- That includes defense contractors — even the small ones that are responsible for making just one component of a military weapon.
The big picture: 70% of the defense industrial base are small businesses, and they're facing many of the same cyber threats as the typical small business, Bailey Bickley, chief of DIB defense at the NSA Cybersecurity Collaboration Center, said in an interview at the RSA Conference last week.
- But many small defense contractors believe their work isn't consequential enough to catch the eyes of adversarial hackers, she adds.
- That's even despite very public warnings over the last year from top U.S. cyber officials about increasing Chinese government cyber threats.
What they're saying: "These companies are truly a target of nation-state activity, and we need them to understand that and know how to defend against it," Bickley told Axios.
- "The fact is, our adversaries, particularly the People's Republic of China, [have] an incredible amount of resources to do mass scanning of the internet, mass exploitation and mass data exfil."
Threat level: Defense contractors are rich targets for nation-state hackers looking to steal military secrets and ransomware hackers targeting small businesses, Bickley said.
Between the lines: One of the biggest hurdles for defense contractors is a lack of technical expertise and money needed to invest in cybersecurity.
- "When you engage with these companies, they are so good at what they do, and it's not cybersecurity," Bickley said. "They're really just grappling with.... 'What do I do? Where do I start?'"
The intrigue: The NSA is well-known for its own espionage, surveillance and hacking operations, but the agency is also key in overseeing defense contractors' cybersecurity needs.
- The agency provides several free cybersecurity tools to defense contractors, including DNS filters, threat intelligence information-sharing programs and vulnerability scans.
- Most nation-states and ransomware actors are just conducting basic scans of internet-facing systems to see which ones are vulnerable to attacks, and the free tools are aimed at closing those flaws before hackers find them, Bickley said.
- The NSA will also go directly to a contractor to help it best approach the vulnerabilities it's grappling with.
Yes, but: These tools don't completely eradicate the threats posed by Volt Typhoon — the Chinese hacking group targeting American infrastructure — since they can't remove hackers who are already lurking inside a system.
- "It's just challenging to find, so there might be maybe a false sense of security," Bickley said. "Companies look and they don't see anything."
- Part of the challenge with Volt Typhoon is the group's persistence: Its hackers are known to stealthily linger on a system, and not all companies have access to activity logs that date back far enough to spot the initial intrusion.
- Bickley and her team haven't seen products on the market yet that could boot Volt Typhoon from a system once it's inside.
What we're watching: Bickley's office is always looking for new, low-cost, scalable and easy to maintain cybersecurity tools it could pilot and make available to defense contractors.
2. Artificial intelligence experts under attack
A Chinese-speaking hacking group is targeting individuals tied to a U.S. artificial intelligence company in an ongoing phishing attack, researchers at Proofpoint said yesterday.
Why it matters: AI operators have become prime targets for hackers looking to steal trade secrets as the U.S. and China continue to battle for AI dominance.
Zoom in: Fewer than 10 individuals tied to the same "leading U.S.-based artificial intelligence organization" received a phishing email this month aimed at deploying trojan malware onto their devices, according to Proofpoint's report.
- The hacking group used a free email account to send an AI-themed lure that tried to get recipients to download a malware-laced zip file.
- Attackers pretended to be a user reporting problems with an AI tool they were using for work, and claimed they had more details about the issue in the attached file.
- The malware in the zip file is nearly identical to the malicious files seen in another scheme that Cisco discovered in November that targeted people in Central and East Asia.
Yes, but: Proofpoint did not name the U.S. company where the targeted experts work.
The big picture: It's rare to see a phishing campaign be as precise and limited as the one Proofpoint uncovered — underscoring the heightened insider threats facing U.S. AI companies.
- Not only are AI operators dealing with run-of-the-mill cyber threats like phishing, but they're also contending with a range of insider threats, including nation-state spies and employees who may be duped into sharing secrets.
- AI firms are paying attention: Last week, OpenAI listed a role for an insider risk investigator.
3. Pentagon weighs Microsoft licensing upgrades
The Pentagon is looking at expanding its use of Microsoft software across all components starting next month, according to a draft memo obtained by Axios.
Why it matters: The tech upgrade is spurring concerns among competitor cybersecurity and software vendors interested in coveted defense contracts.
Zoom in: The Pentagon is pushing all department components to start upgrading to Microsoft's E5 licenses by June 3 to support its ongoing zero trust transition, according to the memo.
- The E5 license gives organizations access to Microsoft 365 Defender and other tools that help with insider risk management, identity protection and more.
- If the memo is published as-is, Department of Defense offices would have until June 2025 to complete the transition and install these new tools.
Catch up quick: The Pentagon has been working since 2022 to implement a new zero trust security strategy — which overhauls which employees have access to certain files and requires tougher identity verification tools — by the 2027 fiscal year.
- Pentagon CIO John Sherman told DefenseScoop last week that the department has held "very candid discussions" with Microsoft about its cybersecurity strategies after a data breach last year.
What they're saying: Timothy Gorman, a Pentagon spokesperson, told Axios that the Microsoft E5 upgrades are just "one solution in addition to many other integrated solutions" that DOD is implementing as part of the strategy.
- "There is a draft internal memo in coordination to clearly communicate our leadership's intent," he added.
- David McKeown, DOD's deputy CIO for cybersecurity, mentioned the planned upgrades during remarks at the RSA Conference's public-sector day last week, Gorman said.
- A Microsoft spokesperson said in a statement that its zero-trust platform "emphasizes proactive, integrated, and automated security measures," and it has capabilities for DOD's zero-trust plans.
The big picture: Ever since Microsoft uncovered a Chinese hack of some government officials' email inboxes last summer, tensions between parts of Washington and the tech giant have been high.
- A government advisory board released a report last month saying the attack was "preventable and should never have occurred."
- An aide for the House Homeland Security Committee told Axios on Wednesday that they're working with Microsoft to find a date for a potential hearing on the company's cybersecurity approach.
- Microsoft has also overhauled its internal cybersecurity strategies in response to the incident.
Yes, but: Industry groups are concerned that the Pentagon will open itself up to increased security flaws if it deepens its relationship with Microsoft.
- "It is concerning for any department to further entrench itself into Microsoft's ecosystem before the company has demonstrated that it has satisfied the recommendations of the [Cyber Safety Review Board] report," Ryan Triplette, executive director of the Coalition for Fair Software Licensing, told Axios.
- Triplette added that the E5 licenses come at a "significantly increased cost" and could limit other vendors' ability to compete for contracts or assist in any government security incidents.
The bottom line: Microsoft was already working with the department to help with the zero-trust transition, and typically draft guidance like this wouldn't receive as much scrutiny.
- But the proposed guidance comes as competitors and officials are hawkishly watching Microsoft's every move due to the high-profile attacks.
4. Catch up quick
@ D.C.
👋 Senior CISA official Eric Goldstein is leaving the agency next month. (CyberScoop)
🤖 Nation-state adversaries are likely to tap artificial intelligence tools in their disinformation campaigns targeting the U.S. elections, top officials warn. (Associated Press)
🗳️ Three bipartisan AI and election bills advanced out of the Senate Rules committee on Wednesday, marking the first major pieces of AI-related legislation to leave committee this year. (Axios Pro)
@ Industry
🏷️ Google has devised a way to watermark AI-created text without altering the quality or meaning of the writing. (Axios)
🇨🇳 Microsoft has asked hundreds of employees who work on cloud computing and artificial intelligence operations in China-based offices to consider moving to another country. (Wall Street Journal)
🔎 Investment companies are now required to have a cyber incident response program to assist during a data breach, under SEC rules adopted yesterday. (Reuters)
@ Hackers and hacks
🚔 Federal law enforcement seized the website and Telegram page tied to dark web marketplace BreachForums — again. (The Record)
🇰🇵 Federal prosecutors charged an Arizona woman with assisting an elaborate North Korea-linked scheme that helped foreign IT workers pose as Americans to land jobs at U.S. companies. (CNN)
🚗 Nissan North America says that a recent ransomware attack exposed personal information belonging to roughly 53,000 employees and consumers. (SC Media)
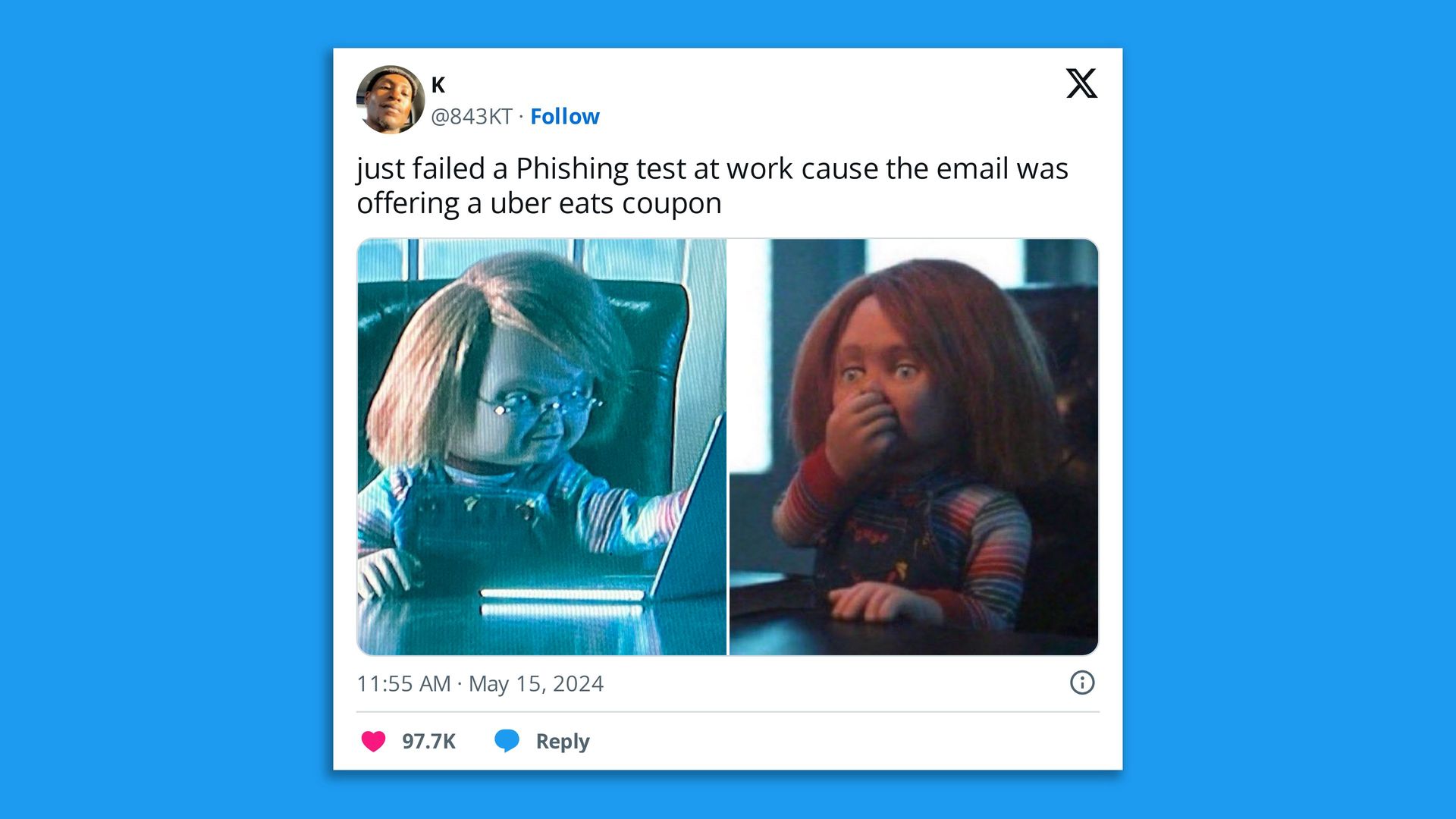
5. 1 fun thing
Watch out: Phishing email tests are getting savvier!
- 👀 I, too, would be enticed by a food delivery-themed lure.
☀️ See y'all Tuesday!
Thanks to Megan Morrone for editing and Caitlin Wolper for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook