Intel is dealing with a major chip bug, but full impact unclear
Add Axios as your preferred source to
see more of our stories on Google.
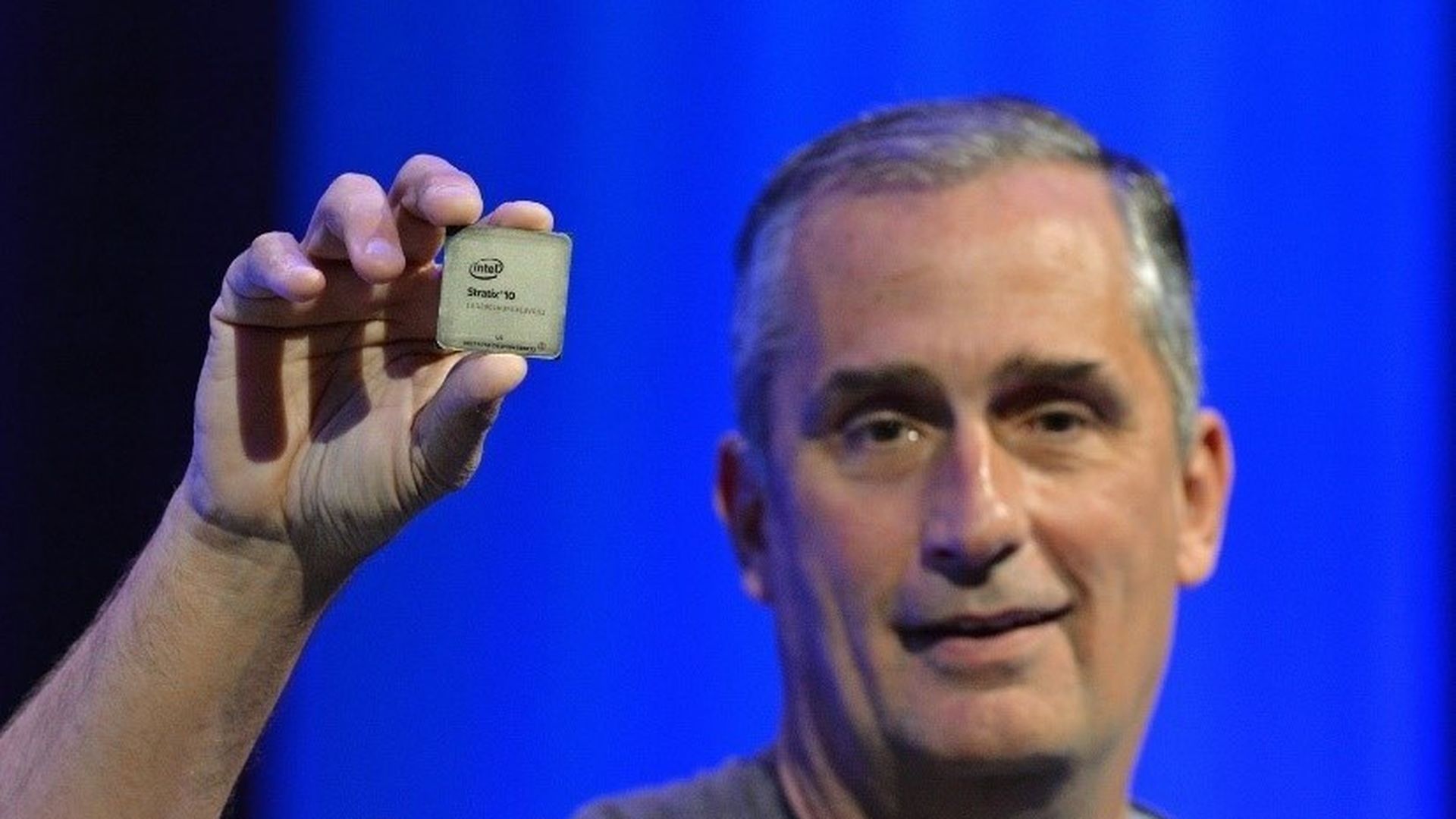
Intel CEO Brian Krzanich holding up one of the company's chips. Photo: Intel
It's clear that a soon-to-be-disclosed bug in Intel chips is going to be a big deal, but it's tough to say just how big until Intel shares more details publicly and the other key players — Intel, Microsoft, Apple, Google and Amazon share the steps they are taking to secure machines in the wake of the flaw.
What we know: There is a major bug out there that leaves lots of different types of computers running Intel chips vulnerable to an attack. That includes PCs, but also appears to include cloud services that run on Intel chips, such as those from Amazon. Reports suggest that, for now, Windows, Linux and MacOS (as well as impacted cloud operating systems) are being rewritten to close the security hole created by the flaw.
Update: It's not just Intel affected.
That said, there is a lot we still don't know. Here are three big questions:
- How much will it cost to fix?It's clear that the major operating system vendors, including Microsoft and the Linux community as well as cloud providers like Amazon, have spent significant money to rearchitect their operations. PC makers, cloud service providers and others will also have to educate their consumers on the impact. Plus, Intel could be looking at lawsuits from those who say their machines performance has been degraded.
- How will it affect computer performance?This has been the subject of much speculation in recent days, with some seeing a performance hit of as much as 30%, while others saying the performance impact will be much smaller in nearly all cases.
- When will the companies break their silence?There is clearly a benefit to a coordinated response, but at this point there are lots of questions swirling, so hopefully answers are coming sooner rather than later. (Update: Sources tell Axios the research behind this flaw will come out this afternoon, with comments from the companies affected expected to follow.)
Intel, Microsoft and Apple have declined to comment. Google and Amazon representatives did not immediately respond to requests for comment.
