Axios Future of Cybersecurity

July 08, 2025
Happy Tuesday! Welcome back to Future of Cybersecurity.
📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,795 words, a 7-minute read.
1 big thing: The cybercriminal group wreaking havoc on corporate America
A persistent hacking crew of young men and teenagers is back with a vengeance, wielding a two-year-old playbook to knock U.S. corporate systems offline.
Why it matters: Scattered Spider hasn't had to evolve much to remain effective — a sign of how little corporate cybersecurity defenses have improved.
- The group's tactics, including help desk impersonation and SIM swapping, continue to wreak havoc across critical industries.
Driving the news: Over the past month, Scattered Spider has been on a hacking spree that's disrupted operations at retailers, grocery chains, insurance providers, and airlines across the U.S., the U.K. and Canada.
- Their reach may also now extend into Australia, where Qantas is investigating a cyberattack on one of its call centers — a hallmark tactic of Scattered Spider.
The big picture: Unlike most ransomware gangs, Scattered Spider isn't a monolithic, state-sponsored machine. It's a loose collective, largely made up of teenagers and young men who emerged from online gaming communities like Roblox and Minecraft.
- "Scattered Spider includes more people in Western countries than other ransomware groups," Cynthia Kaiser, senior vice president of Halcyon's Ransomware Research Center and a former top FBI cyber official, told Axios.
- But while originally rooted in English-speaking countries, it's evolved into a more global operation, she said.
Breaking it down: The group operates like a business, with a leadership structure, junior associates and temporary roles. Some members' sole job is to call help desks and reset employee passwords.
- Adam Meyers, SVP of counter adversary operations at CrowdStrike, told Axios the group's origin lies in a toxic subset of gaming culture, where online harassment evolved into SIM swapping and eventually ransomware.
- Scattered Spider's core includes about four leaders, but its operations are interwoven with members of the broader online community "The Com," which has ties to cybercrime and real-world violence, experts said.
How it works: The group's primary tactic remains voice-based phishing where they call a company's overseas help desk, impersonate an employee, and reset their single-sign-on passwords.
- They then use SIM swapping to intercept multifactor-authentication codes.
- In recent incidents, the group has escalated attacks by targeting ESXi hypervisors — systems that power a company's servers and digital operations but often fly under the radar of traditional security tools. Once inside, they deploy ransomware and cripple the server environment.
- "They're ninjas with identity," Meyers said. "They know how to avoid modern security tools ... and they're incredibly fast — in some cases, there's less than 24 hours between gaining access to deploying ransomware."
- Meyers added that his team has identified seven unique voices calling help desks in recent months.
Flashback: Scattered Spider first made headlines in 2023 with attacks on Las Vegas casinos, including MGM Resorts and Caesars Entertainment. Two years later, their methods remain largely unchanged.
- "It's largely the same, frankly," Meyers said. "Once they figure out one organization that they can successfully get into, then they go, 'We're here, who are their peers, who are their competitors, who else is there that we can perhaps go after?'"
Threat level: Scattered Spider is now collaborating with Russian ransomware gangs, including those behind Play, Akira and DragonForce, Kaiser said.
Between the lines: Despite the group's Western presence, law enforcement faces obstacles in tracking them down.
- Many members are minors, which gives them different legal protections, Meyers said. And if they have any mental health conditions, officials in some countries where the group operates are limited in how long they can hold them and what charges they can pursue.
- For instance, when authorities arrested members of the Lapsus$ hacking gang — another group involving juvenile offenders — prosecutors struggled to proceed against a 17-year-old despite clear evidence of major corporate breaches.
- Kaiser noted that identifying every member of Scattered Spider is difficult due to the group's sprawling, decentralized nature.
The intrigue: Still, U.S. officials have made more arrests tied to Scattered Spider than to Russian ransomware crews. In November, five men were charged in connection with the group.
The bottom line: Experts urge U.S. companies to implement strict ID verification protocols at IT help desks and to upgrade outdated MFA methods like SMS and voice codes.
- They should also closely monitor how much network access is granted to third-party vendors.
2. Ransomware knocks global IT supplier offline
Ingram Micro, a leading tech supplier for manufacturers and cloud providers, warned over the weekend that it's battling a ransomware attack that has knocked some of its systems offline.
Why it matters: While not a household name, Ingram Micro works with thousands of companies, including major brands like Apple and Microsoft, to distribute hardware, software and other tech services.
- Outages can cause shipping delays, stall cloud services, and lead to further data breaches of customers' sensitive information.
Driving the news: After days of outages, Ingram Micro shared details about the ransomware attack in a statement Saturday night.
- The global IT distributor said hackers had taken some of its internal systems offline, and the company proactively shut down some other systems to contain the attack.
- "Ingram Micro is working diligently to restore the affected systems so that it can process and ship orders, and the Company apologizes for any disruption this issue is causing its customers, vendor partners, and others," the company said in the statement.
- The company also said yesterday that it had "made important progress on restoring our transactional business."
Zoom in: Over the weekend, customers reported they were unable to place orders. The company's website went offline Thursday morning but came back online sometime yesterday.
- Customers have also complained on social media about emails to Ingram Micro account managers bouncing back, according to The Register.
- BleepingComputer reported that the hackers are using the relatively new SafePay ransomware strain, and employees opened their computers to ransom notes last week.
The big picture: Hackers often target third-party, behind-the-scenes companies like Ingram Micro because of the ripple effects just one incident can have.
- Not only will a company like Ingram Micro go dark, but its customers will also face the effects for weeks as the company works to come back online.
- That cascading effect could make companies like Ingram Micro more willing to pay a ransom to decrypt their systems or prevent the publication of any stolen customer data.
What to watch: Ingram Micro has yet to disclose how the hackers broke into its systems or which hacker group is behind the attack.
- The company is likely to share more details about the financial impacts of the incident with investors in the coming weeks.
3. Lawmakers demand update on CISA election work
A pair of Democratic lawmakers warned in a letter sent yesterday that employees at the nation's top cyber agency are "afraid" to work with state and local election officials and vendors "for fear of retribution."
Why it matters: Coordination among federal, state and local election officials is necessary to ensure that each office is up to date on the latest cyber threats.
Driving the news: Rep. Joseph Morelle (D-N.Y.) and Sen. Alex Padilla (D-Calif.), ranking members of the House and Senate administration committees, sent a letter to CISA leadership seeking information about the state of the agency's election security work.
- The lawmakers asked the top CISA officials to weigh in on a series of questions about the ways the agency has restructured, what involvement the Department of Government Efficiency has had in this restructuring, and how the agency is continuing to engage with state and local election officials.
- The two lawmakers also noted that they had heard complaints that CISA staff was too afraid to engage with state and local election officials, but they did not expand further on that claim.
In a statement, Marci McCarthy, CISA's director of public affairs, told Axios that the agency responds to "official correspondence through official channels."
- "We're getting CISA back on mission as America's cyber defense agency," McCarthy said. "We're focused on operationalizing our core authorities: strengthening our nation's cybersecurity, critical infrastructure protection and harnessing the true power of public/private collaboration to secure the homeland."
The big picture: Since January, CISA has lost a third of its workforce and faced major budget cuts as the Trump administration overhauls the agency.
- Some of those workforce cuts have included staffers in the agency's election security team.
- President Trump also directed the Department of Justice to open an investigation into former CISA director Chris Krebs after the agency, under his leadership, publicly said the 2020 election wasn't rigged.
Zoom in: Election officials have already said they're preparing to get less federal help as they prepare for their local elections later this year.
- Earlier this year, CISA pulled its funding for the Election Infrastructure Information Sharing and Analysis Center, which helped member organizations trade details about ongoing cyber threats affecting election vendors.
What's next: Morelle and Padilla have asked CISA leaders to respond to their inquiry within the next two weeks.
4. Catch up quick
@ D.C.
☎️ Someone pretending to be Secretary of State Marco Rubio reached out to foreign ministers, a U.S. governor and a member of Congress via phone and text messages by using AI-powered software to imitate his voice and writing style. (Washington Post)
🇨🇳 A top FBI official says that Salt Typhoon is "largely contained" and "dormant" in U.S. telecom networks but still poses a threat. (CyberScoop)
🤖 Despite the downfall of a possible moratorium on state-level AI regulations, discussions around the idea could spur more federal legislation, experts say. (Axios)
@ Industry
👨🏻⚖️ SolarWinds has reached a preliminary deal with the Securities and Exchange Commission to end litigation tied to the 2020 Russia-linked cyber espionage campaign. (Reuters)
💸 The Justice Department is investigating whether a former employee at a ransomware negotiation firm took a slice of the payments. (Bloomberg)
@ Hackers and hacks
👀 Australian airline Qantas says "a potential cybercriminal" group has contacted the company after a significant data breach. (Australian Broadcasting Corp.)
🛍️ Louis Vuitton's South Korea unit warned that some customer data, including contact information, may have been exposed in a recent breach. (Reuters)
👋🏻 Hunters International, a notorious ransomware gang that targeted more than 300 victims, said it's shutting down and released free decryptors to all affected companies. (The Record)
5. 1 fun thing
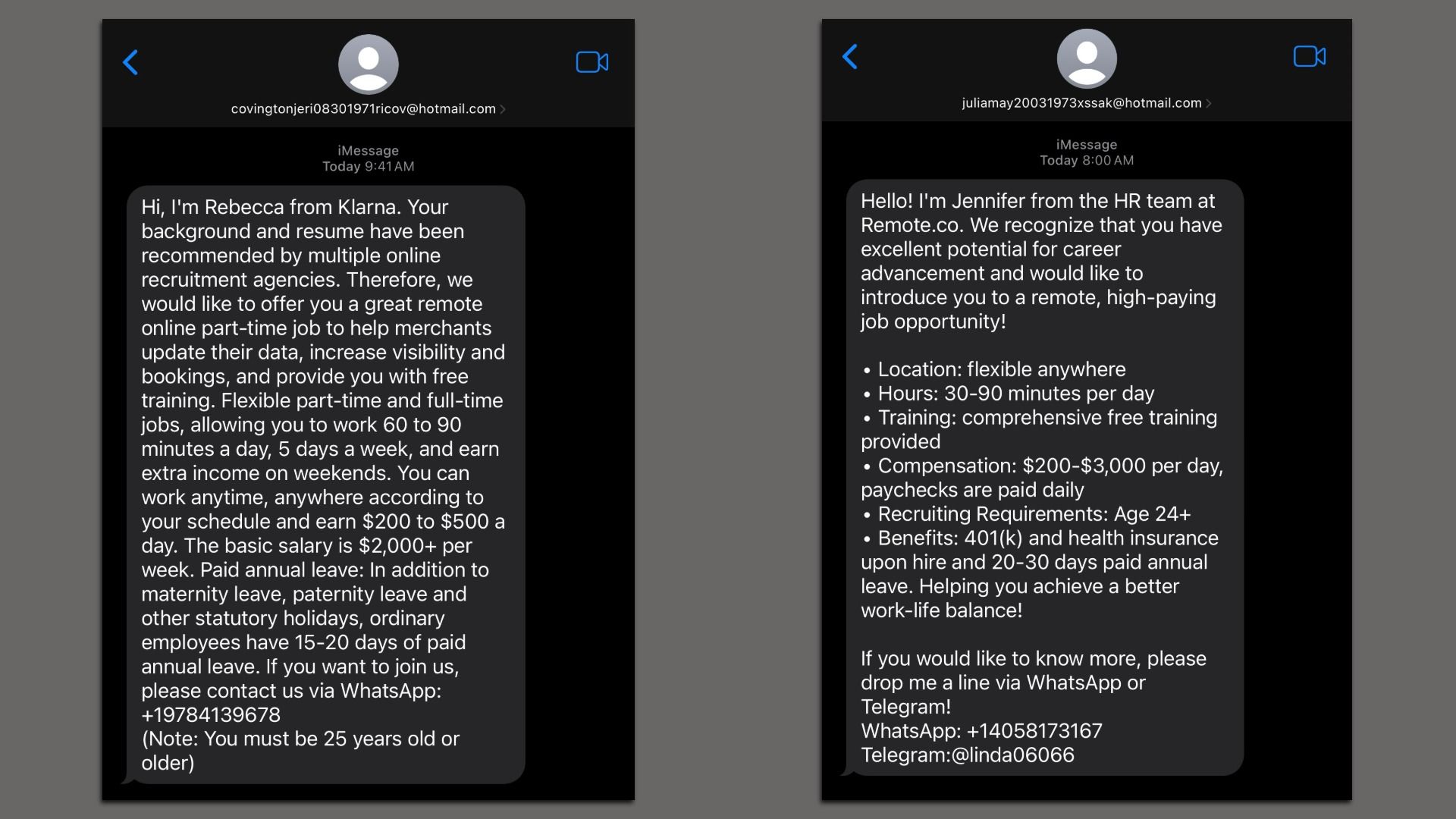
In the two weeks since I covered how one woman fell for a job scam, I've been inundated with texts offering me (fake) jobs, too.
- I'm not the only one: Some readers over on LinkedIn also said they've been receiving waves of job scam texts in recent months.
- In this context, it's easy to see these for what they are: scams. But even the most obvious job scams can catch people off guard when they're moving fast or feeling pressured to find a job.
The bottom line: Be wary of any text-based job recruiters, especially if you haven't talked to anyone at the company or applied to a job yet.
- Legit employers won't be in a rush to hire you without an interview — or reach out from a Hotmail address.
☀️ See y'all next week!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity