Axios Future of Cybersecurity

November 12, 2025
Happy Wednesday! Welcome back to Future of Cybersecurity.
📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,698 words, a 6.5-minute read.
1 big thing: Suing the scam factory flooding U.S. phones
Google filed a lawsuit today against alleged China-based operators behind Lighthouse, a phishing platform it says fuels the toll-payment text scam flooding U.S. phones.
Why it matters: Scam networks now operate like global tech firms, forcing companies and investigators to use creative legal and technical tactics to fight them.
- Scammers made off with more than $16 billion from consumers last year, according to the most recent FBI data.
Driving the news: Google filed a civil suit in the U.S. District Court for the Southern District of New York seeking to dismantle the group behind Lighthouse.
- Google says it's the first lawsuit of its kind aimed specifically at a phishing-as-a-service operation.
- For a monthly fee, Lighthouse's software kit lets cybercriminals easily launch text-message scams and set up fake websites that mimic legitimate brands.
Between the lines: The complaint describes Lighthouse as part of a "relentless phishing campaign" that has affected more than a million people and potentially compromised between 12.7 million and 115 million credit cards in the U.S. alone during just one text scam operation.
- In one 20-day period, Lighthouse was used to create 200,000 fraudulent websites and attack more than 1 million potential victims in at least 121 countries, Google says in the filing.
How it works: Lighthouse is marketed as a plug-and-play platform for phishing scams — a "phishing for dummies" kit, as the lawsuit puts it.
- Users subscribe via Telegram, where a self-service bot lets them pay for access to the software on a "weekly, monthly, seasonal, annual, or permanent" basis, per the complaint.
- From there, they choose from more than 600 spoof templates mimicking more than 400 entities, including the U.S. Postal Service, New York City's government, Apple, banks and toll agencies.
- Lighthouse allows users to sort phishing templates by geographic region, so a scammer can easily select fake websites that will resonate with local targets.
Threat level: Lighthouse also has several mechanisms designed to evade detection.
- Victims receive a text prompting them to pay a toll or redeliver a package.
- When they visit the fake website, they're asked to enter payment info. They don't even need to click "Submit" for the data to be stolen because the software is tracking their keystrokes in real time.
- If multifactor authentication is enabled, Lighthouse triggers the victim's bank to send a legitimate verification code to their phone and then tricks them into entering it on a fake screen, allowing scammers to evade any suspicion and add the card to their digital wallet.
Zoom in: Google's complaint paints Lighthouse as a full-fledged criminal enterprise with separate teams dedicated to development, data brokering, spam delivery, financial theft and marketing.
- Data brokers gather personal info from breaches, social media and public records.
- Spammers use phones, modems and SIM cards to send mass messages.
- A so-called "theft group" uses the stolen info to drain bank accounts, launder money, and resell credit card information on the dark web.
- And admins run tutorials, answer questions, and post screenshots of brokerage accounts with balances in the millions to entice new scammers to "start fishing."
The intrigue: Some Lighthouse users have purchased online ads, including through Google Ads, to funnel victims to fake retail sites selling everything from phone cases to groceries.
- Google says that scammers used fake identities to bypass verification and that it has since suspended those accounts.
What to watch: Google is also endorsing three anti-scam bills today that have already been introduced in Congress: the GUARD Act, the Foreign Robocall Elimination Act and the SCAM Act.
2. Congress throws a lifeline to info sharing
A decade-long information-sharing program is poised to get a two-month reprieve in the government funding deal that senators approved this week.
Why it matters: The private sector and the federal government haven't had a full view of the digital threat landscape for six weeks after companies lost prized liability protections and grew more reticent to share information.
Driving the news: The Cybersecurity Information Sharing Act of 2015 expired Sept. 30, ending those protections for companies that shared information about cyber threats or breaches with federal law enforcement and government agencies.
- Since then, lawmakers and the White House have been debating the best path forward.
- The Trump administration endorsed a clean, 10-year reauthorization. Senate Homeland Security leader Rand Paul (R-Ky.) and some House Republicans want changes before reauthorizing the program.
Zoom in: Under the short-term deal lawmakers are debating this week, Congress would extend liability protections until Jan. 30.
- No other changes would be made to the program. It's unclear if the extension would retroactively cover information shared with the government since Oct. 1.
Reality check: The long holiday recess falls right in the middle of this two-month period, leaving lawmakers virtually no time to iron out a long-term deal.
What to watch: How much influence the White House ends up having on the Senate.
- Paul has vocally opposed a push to bypass his committee and bring a 10-year reauthorization to the floor.
3. Amazon uncovers identity security zero-days
Amazon researchers warned today that an advanced hacking group was exploiting flaws in Cisco and Citrix software months before the companies disclosed them.
Why it matters: Targeting both flaws at once suggests that the hackers were running a coordinated campaign against systems that control logins and remote access.
Zoom in: Amazon's threat intelligence team said in a report published this morning that it found hackers targeting vulnerabilities in Cisco's Identity Services Engine and Citrix's Gateway VPN.
- The two flaws — which have since been patched — would allow a threat actor to sneak into company networks and traverse them without triggering security alarms.
- Amazon's researchers said they spotted hackers targeting these flaws through the company's MadPot honeypot system.
- Spokespeople for Cisco and Citrix did not respond to requests for comment.
Threat level: Researchers uncovered the campaign after Cisco had issued a partial fix for its ISE software and before Citrix publicly disclosed its own flaw.
- The hackers' malware was custom built for Cisco ISE environments and ran entirely in the system's memory, leaving little to no trace on infected networks.
What's next: Cisco and Citrix have released patches, and Amazon is urging security teams to restrict employee access to sensitive security tools and management portals.
4. Beware deepfake holiday scams
Nearly half of adults say they or someone they know has already encountered a deepfake holiday scam, according to new survey data from McAfee.
Why it matters: Generative AI-powered video tools, like OpenAI's Sora, are making deepfakes frighteningly believable and hard to detect.
By the numbers: 26% of the 8,600 adults around the world surveyed online in August said they'd personally encountered a holiday scam that used deepfakes or fake celebrity endorsements.
- Another 20% who hadn't personally seen one said they knew someone who had.
- The scams were most commonly spotted by 25- to 44-year-old respondents.
The big picture: Holiday shopping is a major target for scammers hoping to lure customers to their fraudulent websites — offering deep discounts to get them to buy fake products.
- 22% of respondents in McAfee's survey said they had been scammed during past holiday seasons.
What to watch: To avoid getting scammed, McAfee recommended in a blog post yesterday that people go straight to a retailer's site, rather than clicking on a link in an email or text message.
- Pausing for a few moments to check for obvious signs of a scam is also a good practice, McAfee said.
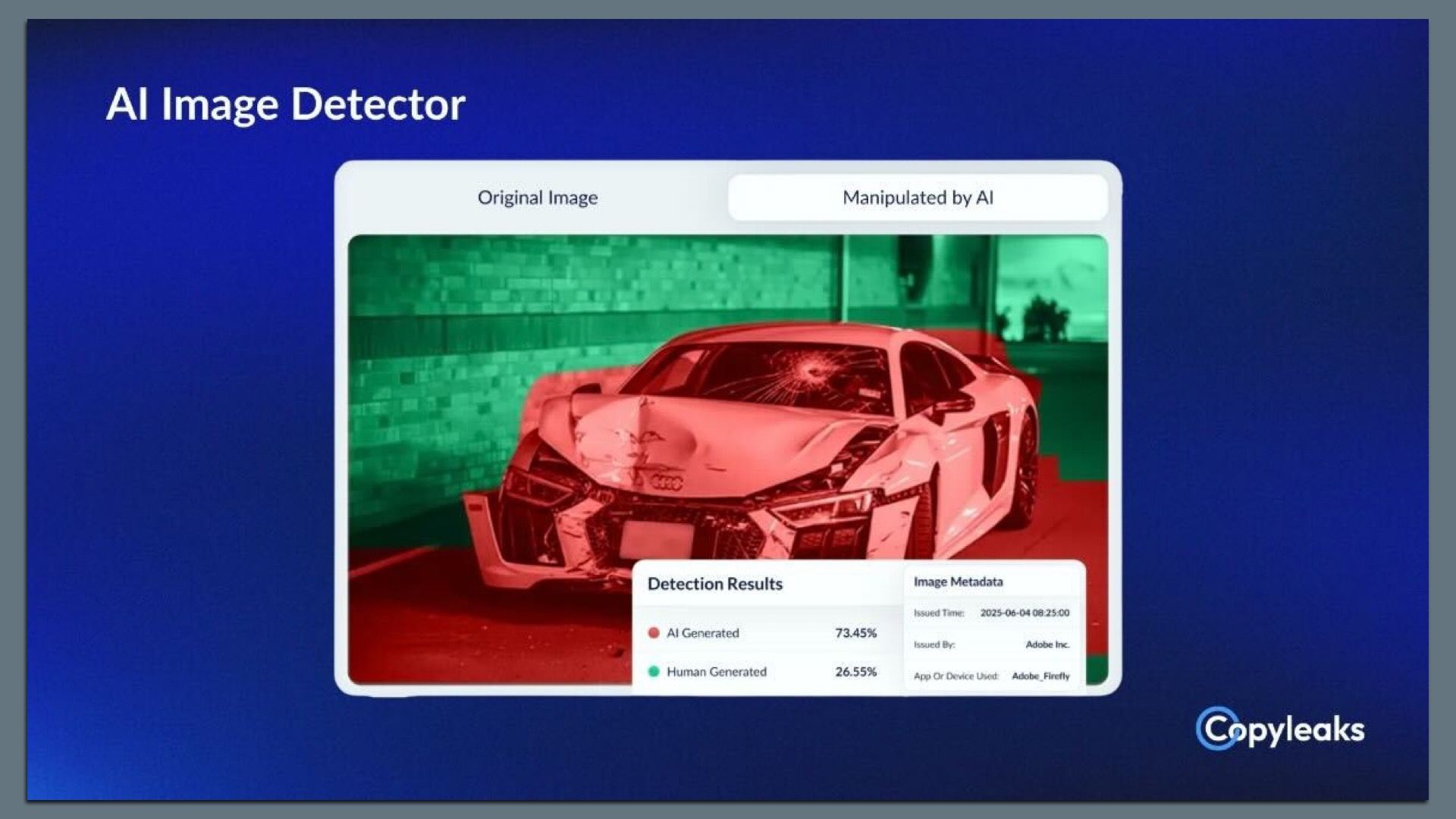
5. Exclusive: Copyleaks scans for AI in images
Copyleaks, known for its software to detect plagiarism and AI-generated text, is expanding into identifying AI use in images, the company shared first with Axios on Monday.
Why it matters: Beyond misinformation, AI image tools are fueling fraud, from fake receipts to doctored insurance claims.
Zoom in: The new Copyleaks detector assigns each image an AI-use probability score and shows where AI was likely applied on an image.
- There's a public demo of the tool.
Zoom out: CEO Alon Yamin told Axios the company sees a broad range of markets for the new tool, including education, financial services and publishing.
- "It used to be 'seeing is believing,'" Yamin said. "It's not anymore the case. So how are you making sure that you're able to really authenticate the content and understand its source?"
- As it does with its text-based detection tools, Copyleaks will charge institutions using its image detector based on volume.
Yes, but: Detecting AI-generated content is tricky; detecting whether AI is used for fraud is even trickier.
- Some phone cameras today use AI to combine multiple exposures for a "best take" or to fill in details on a zoomed-in shot.
- Limited Axios tests found mixed results — the tool flagged some AI-created images of official documents but missed others. It also returned false positives on images that weren't AI generated.
What's next: Copyleaks says that in 2026, it plans to expand into identifying the use of AI in audio and video.
6. Catch up quick
@ D.C.
📦 A recent court filing shows that the shutdown-related government layoffs affected 54 employees at the Cybersecurity and Infrastructure Security Agency. (Nextgov)
🇪🇺 European lawmakers are considering far-reaching changes to the EU's hallmark privacy law to turbocharge AI business in the region. (Politico)
⚠️ A recent cyberattack against the Congressional Budget Office remains a live threat. (Politico)
@ Industry
✅ Google cleared the U.S. Justice Department's antitrust review for its $32 billion purchase of cloud security company Wiz. (Bloomberg)
📈 1Password says it's topped more than $400 million in annual recurring revenue. (CNBC)
💰 Truffle Security, which provides visibility for credential management, raised a $25 million Series B round led by Intel Capital and a16z. (Axios Pro)
@ Hackers and hacks
📰 The Washington Post confirmed it's one of the latest victims of the Cl0p ransomware gang's attacks against vulnerable Oracle E-Business Suite products. (Reuters)
🤖 Some private ChatGPT conversations were indexed in a developer tool used to monitor Google search traffic. (Ars Technica)
👨🏻⚖️ A federal judge reimposed the original sentence for Paige Thompson, who was convicted for the 2019 Capital One data breach that affected more than 100 million people. (CyberScoop)
7. 1 fun thing
🔐 It's not just your parents: Even the Louvre is still using an insecure, easy-to-guess password.
☀️ See y'all Tuesday!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity