Axios Future of Cybersecurity

February 17, 2026
Happy Tuesday! Welcome back to Future of Cybersecurity.
📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,993 words, a 7.5-minute read.
1 big thing: Doorbell cams and surveillance tech face growing public backlash
Sentiment around widely used home surveillance tools is souring as high-profile cases reveal just how deeply law enforcement can tap the data they generate.
Why it matters: What once felt like a personal security upgrade now feels to many like participation in a broader law enforcement apparatus they didn't sign up for.
- New AI advancements have made it easier to search, cross-reference and retain massive amounts of video and license plate data, raising the stakes of what once felt like localized neighborhood tools.
Driving the news: A Super Bowl ad for Amazon's Ring doorbell camera touting the ability of the device's new Search Party feature to locate lost dogs has spurred widespread backlash.
- Many viewers assumed the tool was also able to track and identify people who walk by their front doors.
- Customers posted about destroying their Ring doorbell cameras. Reddit users claimed they were requesting refunds from Amazon.
- Even a popular social media account that rates dog photos posted a video accusing Ring of pushing a "lucrative mass surveillance network" that turns "private homes into surveillance outposts."
In a statement, Ring spokesperson Yassi Yarger said that the company is focused on "giving camera owners context about critical events in their neighborhoods" and that Search Party "doesn't process human biometrics or track people" and is designed to track only lost dogs.
- "Camera owners have always been able to share their videos with others if they choose," Yarger said. "We're using AI to give camera owners relevant context about when sharing might help those in their community — while keeping that choice in their hands, not ours."
By the numbers: In the week after the ad aired, nearly 50% of the social media conversations about Ring were considered negative, compared with 14% that were positive, according to data shared by PeakMetrics.
The big picture: The Super Bowl ad came at a time of simmering concerns around the partnerships personal surveillance tools have with law enforcement.
- Last week, FBI Director Kash Patel said agents investigating the disappearance of Nancy Guthrie were able to "actually excavate material that people would think would normally be deleted and no one would look for" from her Nest smart doorbell camera.
- Flock Safety, the AI-powered license plate reader that's been rapidly expanding across American cities, is reportedly allowing ICE to tap into its databases — prompting some cities to postpone or cancel their contracts.
- On Thursday, Amazon canceled its partnership with Flock Safety. The companies said the partnership would "require significantly more time and resources than anticipated."
- "This integration was never live, and no videos were ever shared between these services," Yarger said.
- Protesters have also been calling on Palantir, which provides AI surveillance technologies, to end its contracts with ICE. (Palantir CEO Alex Karp has argued that protesters should be "protesting for more Palantir.")
Catch up quick: For years, consumers largely accepted the privacy tradeoffs that came with internet-connected cameras.
- Law enforcement has been using footage from the devices to aid investigations for years. Some deals allow users to voluntarily share their videos with law enforcement, while others require officials to submit formal legal requests.
- Adoption of doorbell cameras has continued to rise across the country as users seek to protect their homes from break-ins and other crimes. The same month in 2019 that reports found hackers were breaking into Ring doorbells, the company reported record sales.
- Flock Safety, which was founded in 2017, is in more than 6,000 communities and cities across the country, according to a company fact sheet.
The other side: Law enforcement argues these technologies help to speed up criminal investigations.
- While announcing the Flock partnership cancellation, Ring reiterated that users have full control over whether specific videos are shared with law enforcement.
- The blog post also included a celebration of those who opted to share videos in response to the December shooting at Brown University. "One video identified a new key witness, helping lead police to identify the suspect's vehicle and solve the case," the company wrote.
Yes, but: Privacy advocates have argued the data shared through surveillance technologies is being used in some cases to prosecute protesters and surveil activists.
What to watch: Even as some consumers ditch the technologies, the surveillance ecosystem they helped build isn't going away.
2. Critical infrastructure hacks turn existential
China-linked efforts to burrow into critical infrastructure across the globe for potentially destructive cyberattacks are unlikely to ever be stopped, a top operational security firm warned in a briefing with reporters last week.
Why it matters: Any illusion that global cyber conflict is simply defined by digital spies trying to steal state secrets is officially gone as governments add destructive attacks on critical infrastructure to their arsenals.
Driving the news: Dragos, a cybersecurity firm focused on protecting critical infrastructure, found in its annual threat report, published today, that Voltzite — a group that overlaps with China's Volt Typhoon — continued to target cellular routers and gateways to break into electric, oil and gas companies last year.
- Dragos also observed Voltzite using a botnet to scan for weaknesses across the energy, oil, gas and defense sectors.
Threat level: "We just got more cases this year showing that [Voltzite is] ongoing," Dragos CEO Robert M. Lee told reporters in the briefing. "They're still very active, and they're still absolutely mapping out and getting into, embedding into U.S. infrastructure."
- That's partly because the group doesn't rely on custom malware that's easier to detect.
- Instead, it blends into normal network activity by using legitimate credentials and native system tools, making it far harder to distinguish from routine operations.
The big picture: Since 2023, the U.S. government has been warning about China-linked attackers positioning themselves to disrupt U.S. critical infrastructure in the event of a Taiwan conflict.
- But many critical infrastructure sectors lack the tools to even detect groups like Voltzite and Volt Typhoon that are lurking on the technologies that operate their infrastructure, Lee said.
- "We're going to have to live with the reality that a portion of our infrastructure is currently compromised and will remain compromised at the current trajectory of the community."
Zoom in: Water utilities often need city leaders to approve their expenditures, and it's a tough sell to invest in protection against a threat that may not exist in their specific networks.
- "It's not like the water sector doesn't care," Lee said. But he said many lack budgetary or security resources.
What to watch: Within the next three to five years, many electric utilities will have better visibility into the threats on their operational technology as they implement a North American Electric Reliability Corp. standard that requires them to have internal network security monitoring tools.
3. Exclusive: VulnCheck nabs $25M Series B funding
Vulnerability management startup VulnCheck has raised a $25 million Series B round led by Sorenson Capital, the startup first shared with Axios.
Why it matters: AI tools are helping researchers uncover even more software bugs, driving market appetite for tools that can help security teams sort through the growing backlog.
Zoom in: Founded in 2021, VulnCheck provides both enterprise and government customers with an autonomously updated dataset about the most critical existing vulnerabilities and how hackers are exploiting them.
- The data helps companies sift through the flood of bug reports tied to flaws across their software environments.
- In the last year, VulnCheck grew enterprise annual recurring revenue by 557% and government ARR by 306%, CEO Anthony Bettini told Axios.
- The latest funding brings VulnCheck's total venture funding to $45 million. National Grid Partners joined the round as a new investor, alongside existing backers Ten Eleven Ventures and In-Q-Tel.
What they're saying: "The vulnerabilities that are getting exploited typically aren't zero-days," Bettini said.
- "They're typically vulnerabilities that are ... publicly disclosed, and what's happening on the threat actor side is they're exploiting them faster and faster — and that's largely due to automation."
The big picture: AI models are getting better at finding and validating bugs in software. Anthropic's Claude Opus 4.6 model, released this month, identified roughly 500 zero-day flaws in open-source software during initial testing.
- At the same time, the rise of vibe coding is accelerating the release of insecure applications.
Between the lines: AI may accelerate vulnerability discovery, but automating the rest of the vulnerability management lifecycle is far more complicated.
- Patching and testing how severe a bug is requires nuanced information about each individual system, and creating a patch isn't a guarantee if a system needs to be completely rebooted or is in operational technology that can't be shut down (like a tool that helps run a railroad).
What's next: VulnCheck plans to use the funding to hire, expand its product offerings, and deepen its international footprint.
4. ICYMI: Pentagon threatens Anthropic punishment
Defense Secretary Pete Hegseth is "close" to cutting business ties with Anthropic and designating the AI company a "supply chain risk" — meaning anyone who wants to do business with the U.S. military has to cut ties with the company, a senior Pentagon official told Axios.
- The senior official said, "It will be an enormous pain in the ass to disentangle, and we are going to make sure they pay a price for forcing our hand like this."
Why it matters: That kind of penalty is usually reserved for foreign adversaries.
Chief Pentagon spokesman Sean Parnell told Axios: "The Department of War's relationship with Anthropic is being reviewed. Our nation requires that our partners be willing to help our warfighters win in any fight. Ultimately, this is about our troops and the safety of the American people."
The big picture: Anthropic's Claude is the only AI model available in the military's classified systems and is the world leader for many business applications. Pentagon officials heartily praise Claude's capabilities.
- As a sign of how embedded the software is within the military, Claude was used during the Maduro raid in January, as Axios reported Friday.
Breaking it down: Anthropic and the Pentagon have held months of contentious negotiations over the terms under which the military can use Claude.
- Anthropic is prepared to loosen its current terms of use, but it wants to ensure its tools aren't used to spy on Americans en masse or to develop weapons that fire with no human involvement.
The Pentagon claims that's unduly restrictive and that there are all sorts of gray areas that would make it unworkable to operate on such terms.
- Pentagon officials are insisting in negotiations with Anthropic and three other big AI labs — OpenAI, Google and xAI — that the military be able to use their tools for "all lawful purposes."
The other side: The Pentagon can already collect troves of people's information, from social media posts to concealed-carry permits, and there are privacy concerns that AI could supercharge that authority to target civilians.
5. Catch up quick
@ D.C.
👀 Jeffrey Epstein spent years communicating with cybersecurity experts and attempting to attend two major hacker conferences, according to documents released by the Department of Justice. (Politico)
🧳 A senior Cybersecurity and Infrastructure Security Agency official warned employees that the agency will soon restructure its cybersecurity division, likely resulting in layoffs. (Cybersecurity Dive)
🇮🇷 The Iranian government is surveilling protesters likely through cellphone location data and facial recognition technologies. (New York Times)
@ Industry
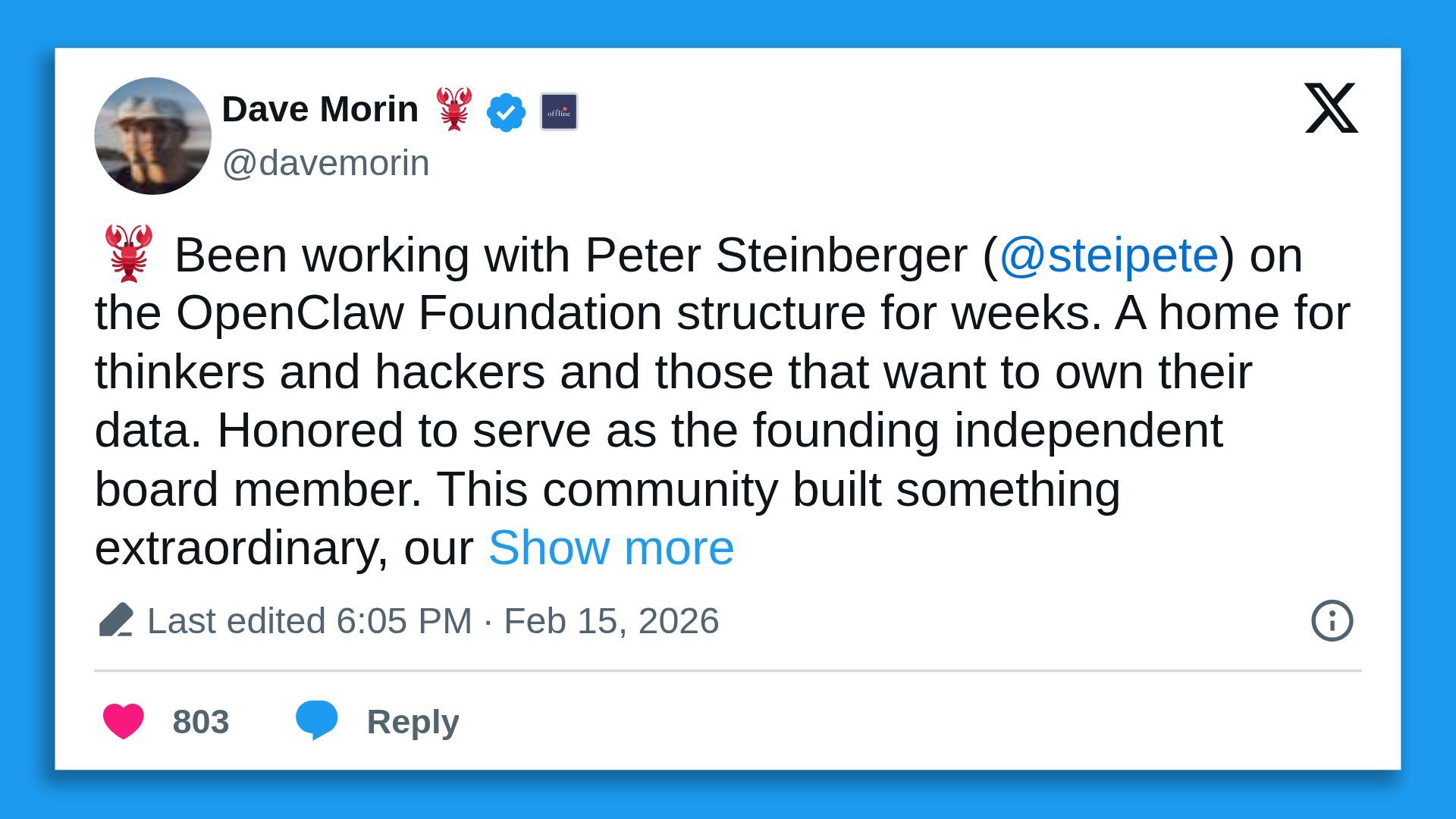
🦞 OpenAI has hired the creator of OpenClaw, the open-source autonomous personal AI agent. (TechCrunch)
🤖 Google says it's being inundated by so-called distillation attacks against its AI model Gemini wherein "commercially motivated" actors are repeatedly prompting the chatbot so they can try to learn how it operates and clone it. (NBC News)
@ Hackers and hacks
⚠️ Microsoft patched critical zero-day vulnerabilities in Windows and Office that hackers are actively exploiting. (TechCrunch)
🍎 Apple disclosed its first actively exploited zero-day of the year, targeting iPhones and iPads. (CyberScoop)
6. 1 fun thing
🦾 Looks like we'll soon have a new open-source foundation in the community.
☀️ See y'all next week!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity