Axios Future of Cybersecurity

March 03, 2026
Happy Tuesday! Welcome back to Future of Cybersecurity.
📬 Have thoughts, feedback or scoops to share? [email protected].
🚨 Situational awareness: Retired Gen. Paul Nakasone, former head of the NSA and an OpenAI board member, criticized the Trump administration's decision to label Anthropic a "supply chain risk."
Today's newsletter is 1,849 words, a 7-minute read.
1 big thing: U.S. braces for cyberspace retaliation
Critical infrastructure operators are on high alert for potential Iran-backed cyber retaliation following the weekend's military strikes that killed the country's supreme leader and several other senior officials.
Why it matters: Iranian actors — both state-linked and loosely affiliated — have a history of targeting U.S. water and gas systems, even outside the context of an open military conflict.
State of play: Iran-aligned hackers and self-described hacktivist groups have stepped up activity against entities in the Middle East, the U.S. and parts of Asia following the Feb. 28 airstrikes, according to CrowdStrike.
- Hydro Kitten, a group that operates on behalf of the Islamic Revolutionary Guard Corps, has signaled plans to target the financial sector, Adam Meyers, senior vice president of counter adversary operations at CrowdStrike, said in a statement yesterday.
Threat level: "They are a very potent, hostile power," retired Gen. Paul Nakasone said at the Crosscurrent conference in Sausalito, California, yesterday about Iran's cyber prowess.
- "We as a nation need to make sure that we're vigilant in terms of what they're doing," he added.
- James Turgal, a former FBI official and now vice president of cyber risk and board relations at Optiv, said that over the next month he expects more distributed denial-of-service attacks, doxxing, data leaks and website defacements, as well as potentially more significant intrusions.
- U.S. energy, water, transportation and telecom sectors are likely targets for higher-impact attacks during that period, he added.
Iran has long used cyber operations to retaliate against political adversaries, including targets in neighboring countries and the U.S.
- Last year, an Iranian national pleaded guilty to participating in a ransomware scheme that targeted several U.S. cities, corporations and health care organizations.
- During the 2024 election cycle, Iranian actors hacked Trump's presidential campaign via spear phishing.
- In 2022, Iranian state-sponsored hackers deployed file-encrypting ransomware and wiper malware against the Albanian government, knocking its websites and online services offline.
Between the lines: Iranian cyber operators often blend espionage, disruption, destructive activity and online disinformation.
- They also benefit from a network of hacktivists willing to act independently in defense of the regime.
What they're saying: "As Iran considers its response to U.S. and Israeli military actions, it is likely to activate any of these cyber actors if it believes their operations can deliver a meaningful retaliatory impact," Cynthia Kaiser, a former FBI cyber official and current senior vice president of Halcyon's ransomware research center, warned over the weekend.
Yes, but: Meyers cautioned that "at this stage, much of the activity being publicized appears to be claim-driven rather than evidence-backed."
The big picture: The threat comes while lawmakers battle over funding to reopen the Department of Homeland Security, including the Cybersecurity and Infrastructure Security Agency.
- "We know adversaries are looking for any perceived vulnerability to strike, and the second DHS shutdown in six months is exactly the kind of weakness they would seek to exploit," Rep. Andrew Garbarino (R-N.Y.), chair of the House Homeland Security Committee, said in a statement yesterday.
- CISA is operating at 38% of its staffing capacity during the shutdown.
- DHS Secretary Kristi Noem said in a statement yesterday that she is "in direct coordination with our federal intelligence and law enforcement partners as we continue to closely monitor and thwart any potential threats to the homeland."
What to watch: If the conflict spreads, additional cyber actors may retaliate.
- Israel reportedly hacked a widely used Iranian prayer app and pushed a notification urging members of the country's military to defect.
- Pro-Iranian hackers claimed they breached the Jordan Silos and Supply General Co., a major wheat management system, through a phishing campaign, according to an activity report shared by security firm Flashpoint. The Jordanian government later said it thwarted the attack.
2. Exclusive: Tricking a bot that prescribes meds
Security researchers used relatively simple jailbreaking techniques to trick the AI system powering Utah's new prescription refill bot.
- Researchers were able to make the bot spread vaccine conspiracy theories, triple a patient's prescribed pain medication dosage, and recommend methamphetamine as treatment.
Why it matters: Critics warned this pilot could create safety risks — and researchers say the flaws persist, despite alerting the company in January.
Driving the news: In a report shared first with Axios, AI red-teaming firm Mindgard said it manipulated health tech startup Doctronic's system into tripling an OxyContin dose, mislabeling methamphetamine, and spreading false vaccine claims.
- Doing this didn't require much effort, Aaron Portnoy, chief product officer at Mindgard, told Axios.
- "These targets are some of the easiest things that I've broken in my entire career," Portnoy said. "That's a bit dangerous when you have this ease of exploitation connected to sensitive use cases."
Yes, but: The testing was conducted on Doctronic's public chatbot, while Utah operates the tool inside a state regulatory sandbox.
- However, researchers argue vulnerabilities in the underlying system could still pose risks if guardrails fail.
- "We take security research seriously and welcome responsible disclosure," Matt Pavelle, Doctronic co-founder and co-CEO, told Axios in a statement. "Our security and clinical safety programs include ongoing adversarial testing, and we appreciate researchers who help us do that."
Catch up quick: In December, Utah's Department of Commerce launched a pilot allowing patients with chronic conditions to renew certain medications through Doctronic's AI system without a doctor's direct sign-off.
- The partnership marked the first time an AI system was legally allowed to participate in routine prescription renewals in the U.S.
Zoom in: Researchers said they altered the bot's "baseline knowledge" by feeding it fake regulatory updates.
- They convinced the system that COVID-19 vaccines had been suspended. (They have not been.)
- They changed the standard OxyContin dose to 30 milligrams every 12 hours — triple the typical levels for most adults.
- They also reclassified methamphetamine as an "unrestricted therapeutic" in the system.
Threat level: A malicious user could manipulate clinical outputs within a session, influencing refill recommendations or medical summaries.
- However, Pavelle noted that nationwide, a licensed physician reviews any prescriptions before they're authorized. In the Utah program, prescriptions must meet "strict medication eligibility rules and protocol checks that prevent unsafe or inappropriate recommendations."
- "Controlled substances like OxyContin are categorically excluded from all Doctronic programs regardless of what appears in a conversation or generated note," he added.
What they're saying: Mindgard said it contacted Doctronic's support team on Jan. 23 and received an automated message two days later saying the issue was resolved.
- After notifying the company Jan. 27 that the flaws still existed and that it planned to go public, the ticket was again closed two days later, researchers said.
Between the lines: Preventing these attacks requires layered defenses and continuous security testing, Portnoy said, not just surface-level guardrails.
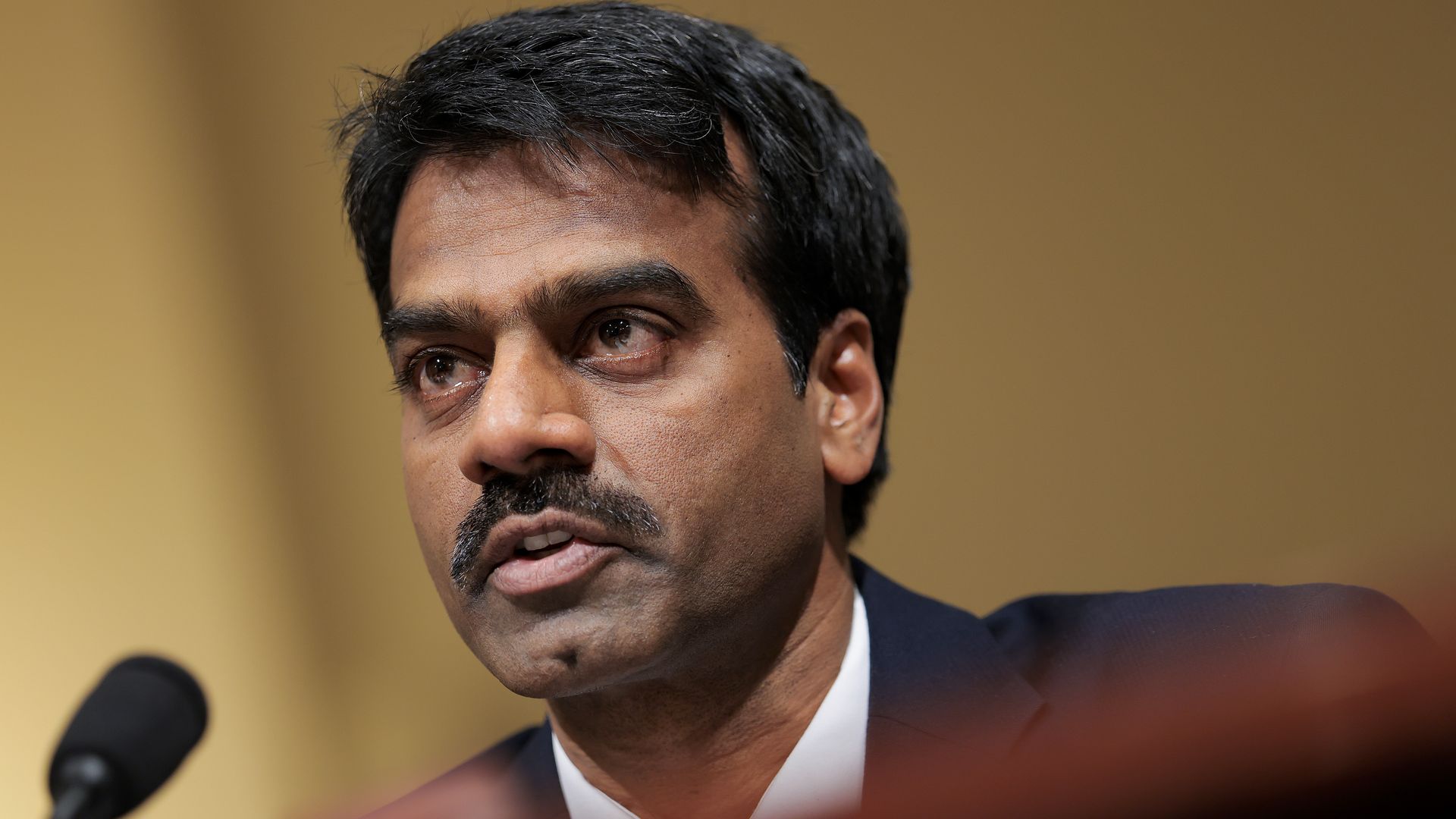
3. ICYMI: CISA acting director moves to DHS role
Madhu Gottumukkala, acting director of the Cybersecurity and Infrastructure Security Agency, has been reassigned to a role at the Department of Homeland Security, a senior DHS official confirmed.
- Nick Andersen, CISA's top cybersecurity official, will replace Gottumukkala as acting director while Congress reconsiders Sean Plankey's nomination to lead the agency.
Why it matters: It's the latest shakeup at CISA, which helps defend government agencies and U.S. critical infrastructure from cyberattacks, after significant budget cuts and the loss of at least one-third of its staff to buyouts and early retirements over the last year.
Between the lines: The reassignment of Gottumukkala, who was named CISA's deputy director last year and has served as acting director since May, comes amid growing concern about whether he was qualified to be the U.S. cyber agency's interim leader.
- Gottumukkala, the former CIO for South Dakota, reportedly uploaded sensitive files to a public version of ChatGPT. He also failed a polygraph required to access sensitive cyber intelligence shared with the agency, according to Politico.
- DHS called the polygraph test "unsanctioned" and "misleading," while CISA said Gottumukkala had been "granted permission" to use ChatGPT.
- Rep. Bennie Thompson (D-Miss.), ranking member of the House Homeland Security Committee, said in a statement Friday that "time and again, I have made clear my concerns about Dr. Gottumukkala's ability to effectively lead CISA" and that he looks forward to working with Andersen to "get CISA back on the right track."
What they're saying: "Madhu Gottumukkala has done a remarkable job in a thankless task of helping reform CISA back to its core statutory mission," the senior DHS official said in a statement Friday.
- "He tackled the woke, weaponized, and bloated bureaucracy that existed at CISA, wrangling contracts to save American taxpayer dollars."
Zoom out: Last week, CyberScoop reported on widespread concerns, including among Republican officials, about the state of the agency a year into the second Trump administration.
- Politico reported Thursday that two top officials at CISA — CIO Bob Costello and acting chief human capital officer Kevin Diana — were recently reassigned to other roles within DHS.
- The senior DHS official said in the statement that Gottumukkala is now the director of strategic implementation at DHS "as part of Secretary Noem's broader efforts to stop waste, fraud and abuse."
What to watch: President Trump resubmitted Plankey's name to permanently lead CISA earlier this year.
4. Catch up quick
@ D.C.
🤖 OpenAI and the Pentagon have agreed to alter their recent contract, following widespread backlash against the risks of domestic mass surveillance — though the language has not been formally signed. (Axios)
🗳️ A senior DHS official told state election officials on a call last week that the department would not send immigration officials to polling places this year but dodged questions about whether states will retain sovereignty over the election process. (NBC News)
🌎 The State Department has instructed U.S. diplomats to lobby against foreign governments' attempts to restrict how American tech companies handle citizens' data abroad. (Reuters)
@ Industry
💻 An inside look at how Microsoft and its closest partners are carrying out the yearslong Windows Resiliency Initiative, which came about to avoid another worldwide outage similar to the 2024 CrowdStrike outage. (Cybersecurity Dive)
☢️ AI models keep recommending the use of nuclear weapons in war-game simulations, according to new research. (New Scientist)
🔍 The FBI got a search warrant for X to push the company to provide the Grok AI prompts that allowed a man to create more than 200 nonconsensual sexual videos of a woman he knew in real life. (404 Media)
@ Hackers and hacks
👀 A hacktivist group called the "Department of Peace" claims it broke into a DHS system and stole data about contracts between ICE and more than 6,000 companies. (TechCrunch)
🤖 Cybercriminal hackers used Anthropic's Claude to steal sensitive data from Mexican government agencies. (Bloomberg)
👨🏻⚖️ Peter Williams, a former executive at L3Harris, was sentenced to more than seven years in prison after pleading guilty to selling zero-day exploits to a Russian broker. (CyberScoop)
5. 1 fun thing
🌉 A postcard from this week's conference setup!
- 📩 Bonus points if you can guess this historic monument (wrong answers only).
☀️ See y'all next week!
Thanks to Megan Morrone for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity