Axios Codebook

January 13, 2023
😎 TGIF, everyone. Welcome back to Codebook.
- On this Friday the 13th edition, we're delving into one of the scariest things around: the ever-evolving ransomware market 😈.
- 📬 Have thoughts, feedback or scoops to share? [email protected]
Today's newsletter is 1,206 words, a 4.5-minute read.
1 big thing: Ransomware gangs cut to the chase
Illustration: Sarah Grillo/Axios
Criminal gangs are using a new method to guarantee a ransomware payout: They're ditching the part where they lock up a target firm's systems by encrypting them and are skipping straight to holding the company's precious data for ransom.
The big picture: As law enforcement attention on ransomware grows, gangs are constantly looking for less-flashy, but still efficient ways to keep their ransomware attacks going.
How it works: A ransomware attack typically starts with hackers installing file-encrypting malware onto an organization's networks and then displaying a ransom note on every screen.
- In recent years, ransomware criminals have added another layer to their schemes: They steal data before locking an organization out, then demand a second payment to stop them from dumping all the data in public online.
Details: Experts explained to Axios how the new streamlined ransomware attacks work.
- Rather than seeing a pop-up note on their screens, an organization will now get an email from hackers saying they've stolen a certain amount of data and plan to leak it if they don't get a payment.
Between the lines: Focusing solely on data extortion allows hackers to carry out their attacks more quickly and eliminates their reliance on encryption tools that sometimes fail mid-attack.
- Law enforcement is also keener on investigating attacks that involve encryption, seeing as it causes more damage, Drew Schmitt, a principal threat analyst at GuidePoint Security, told Axios.
- Critical infrastructure organizations, like hospitals and schools, might be more willing to pay to prevent data leaks because their information is so sensitive, Crane Hassold, director of threat intelligence at Abnormal Security and a former FBI cyber analyst, told Axios.
Zoom in: The LockBit gang, one of the most active ransomware rings in the last year, has urged members to stop using encryption in attacks on critical infrastructure, Schmitt noted. The group even changed its rules to ban the tactic.
- Rulebreakers get banned from using LockBit's tools — including the hackers who used LockBit ransomware to encrypt some systems at the Toronto-based Hospital for Sick Children last month.
The intrigue: As companies have gotten better at backing up their data to defend against encryption-based ransomware, more victims have just been paying up to keep the data from getting released, Kurtis Minder, CEO of ransomware negotiation firm GroupSense, told Axios.
- In turn, ransomware gangs realized they could still get paid the same with half as much work, Minder added.
Yes, but: Ransomware gangs are far from giving up altogether on the encryption maneuver.
- Most ransomware victims are small to medium-sized businesses that don't have the resources or time to build data backups that they can lean on when a ransomware gang locks up their files, Hassold said.
- Other hackers are still chasing the opportunity for a double payday — one for the decryption key and the other for not releasing the data.
- But some gangs might enlist a data-extortion-only tactic if the encryption tools fail halfway through an attack, Minder said.
Be smart: Companies that have solid endpoint security tools and firewalls, along with constant monitoring and security plans that limit employees access to internal files, are the ones that will best be able to foil most varieties of ransomware attack, Schmitt said.
2. Sanctions fuel boom in illicit crypto activity


Illicit cryptocurrency activity hit an all-time high of $20.3 billion in 2022, according to initial estimates from blockchain analysis firm Chainalysis.
By the numbers: The new record high is mostly due to the growing number of crypto-related entities that the U.S. government sanctioned in 2022, per the report.
- Transactions involving sanctioned entities, such as crypto exchange Garantex and crypto mixer Tornado Cash, accounted for 44% of illicit transaction activity.
- However, while transactions tied to sanctioned entities skyrocketed between 2021 and 2022, transaction volumes fell across nearly all other categories of illicit activity that Chainalysis measures, including ransomware and darknet marketplaces.
- But that downward trend is normal in a falling market, the report notes.
The big picture: Cybercriminals often lean on pseudo-anonymous cryptocurrencies because of their reputation for being harder to trace and their relative freedom from reporting regulations compared to fiat currencies.
- For example, ransomware gangs often demand ransoms be paid using bitcoin.
Between the lines: This year's $20.3 billion record accounts for only 0.24% of all cryptocurrency activity — double last year's 0.12% share but still a minuscule percentage of all transactions.
Yes, but: Researchers said the 2022 total is likely to change throughout the year as they identify new wallet addresses tied to illicit activity.
- For 2021, Chainalysis originally found $14 billion worth of crypto tied to illicit activities — $4 billion less than the revised figure.
3. NSA's plea to keep key surveillance power
Gen. Paul Nakasone testifies before a Senate committee in April 2022. Photo: Win McNamee/Getty Images
The head of the National Security Agency made his case Thursday for lawmakers to keep a key NSA surveillance power intact ahead of a tough reauthorization battle this year.
The big picture: Section 702 of the Foreign Intelligence Surveillance Act is set to expire at the end of the year, jeopardizing a surveillance authority that allows intelligence agencies to collect warrantless online communications from foreign persons.
- The fight over whether to keep Section 702 intact will take up much of Capitol Hill's cybersecurity attention throughout the year.
Driving the news: Gen. Paul Nakasone, the head of the NSA and the U.S. Cyber Command, said during an event Thursday that the surveillance power has allowed the U.S. to stop active terrorist plots, foreign ransomware attacks and planned cyber espionage schemes.
- "This authority provides the U.S. government irreplaceable insights, whether we're reporting on cybersecurity threats, counterterrorism threats, or protecting U.S. and allied forces," Nakasone said.
- "We have saved lives because of 702," he added.
Why it matters: Nakasone's comments set the stage for the arguments that the intelligence community is likely to make as lawmakers debate the merits of the program throughout the year.
Yes, but: Civil liberties and privacy advocates have long argued that Section 702 sweeps up far too many Americans' electronic communications, such as emails and text messages, when they talk with people in other countries.
- Some Republican lawmakers are also likely to argue for either letting 702 expire or limiting its scope as their party grows more critical of the intelligence agencies.
4. Catch up quick
@ D.C.
🇷🇺 U.S. and Ukrainian officials say Russian hackers are increasingly targeting Ukrainian services used in daily life. (Politico)
⚠️ A watchdog report warns that the Interior Department's lax cybersecurity policies have led to weak employee passwords and patchy multifactor authentication implementation. (Nextgov)
@ Industry
📉 Cybersecurity company Darktrace cut its revenue growth forecast for the fiscal year ending in June, resulting in the stock falling below its listing price for the first time. (Reuters)
📧 Cloudflare rolled out new email security capabilities to better protect against phishing, malware and other cyber threats. (Wall Street Journal)
@ Hackers and hacks
👑 British postal service Royal Mail is responding to a ransomware attack linked to apparent Russian criminal hackers. (BBC)
🐦 Twitter says there's "no evidence" that user data being sold online was obtained by exploiting a security vulnerability in the company's systems. (Variety)
👀 Two large insurance companies — Aflac and Zurich — said this week that Japanese customer data had been leaked after an attack on a third-party service provider. (The Record)
5. 1 fun thing
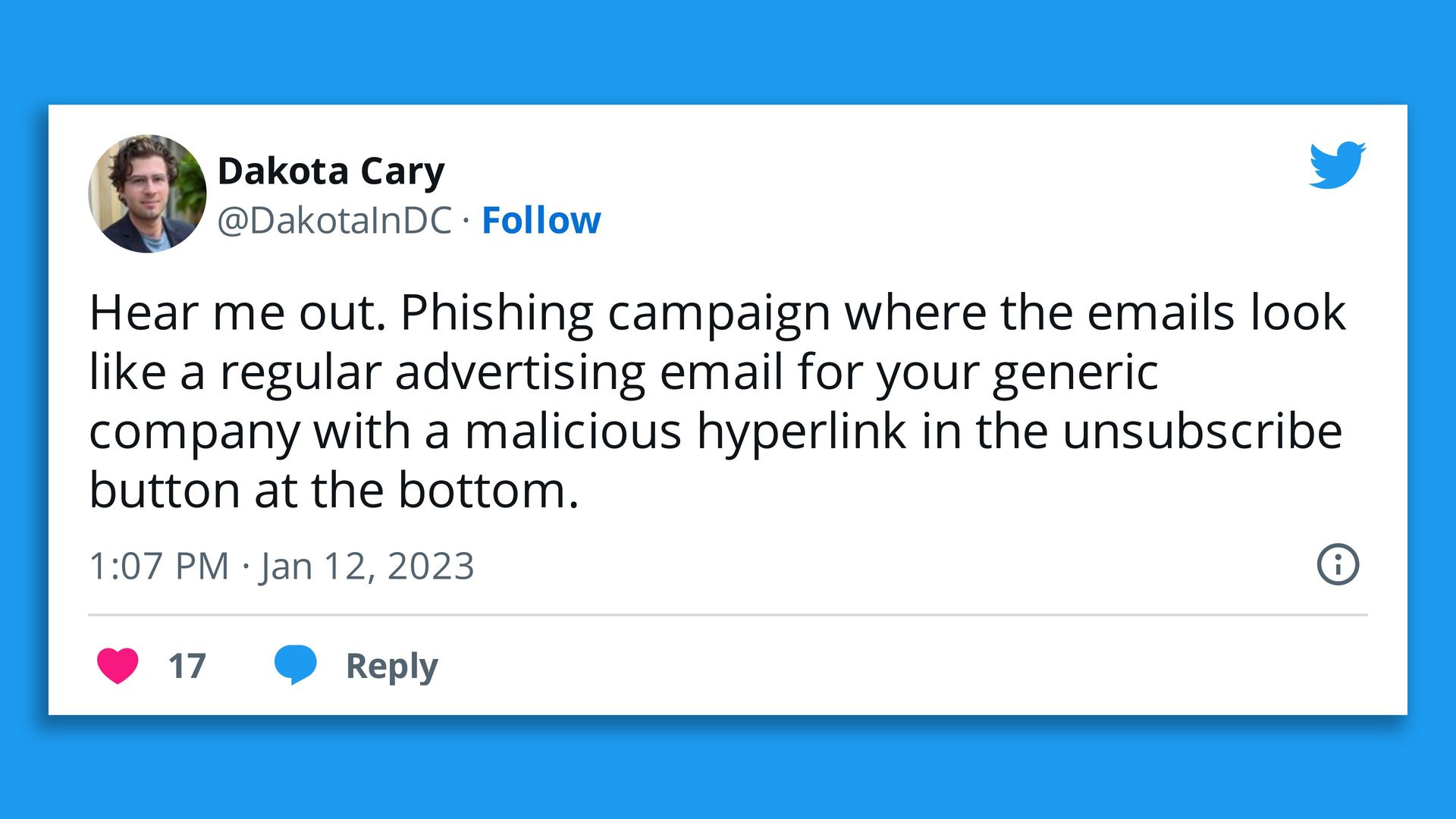
Screenshot: @DakotaInDC/Twitter
New fear unlocked: Going to unsubscribe from an unwanted email and accidentally downloading malware 🙃.
☀️ See y'all on Tuesday!
Thanks to Scott Rosenberg for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.