Axios Codebook

March 27, 2018
Welcome to the first issue of Codebook! Tell all your friends to sign up here. Also tell some people who are not your friends.
Reply to this email to reach me with tips, comments and suggestions. You can also reach me on Twitter @joeuchill.
Why Codebook will be different
Codebook, we hope, will be a place to discuss cybersecurity, policy and science without trying to scare or shame you. The market is already crowded with people who will try to frighten you into clicks or condescend you into better security practices. But after 30 years of trying that without security getting much better, maybe it's time to try something different.
1. Exclusive: ‘Redirecting' extremists away from radical content
Illustration: Sarah Grillo / Axios
It’s no secret that the internet is a fertile recruiting ground for extremists of all types. But a five-month effort trying to combat extremism shows promise in getting would-be white nationalist and ISIS sympathizers to click away from radical content.
- Moonshot CVE, an anti-extremist consultancy, ran ads directed at users searching for propagandist torture videos and using searches like "how to join ISIS" or "kill all the Jews."
- The group was able to divert 1,300 at-risk Google searchers to counter-narratives debunking propaganda or presenting an alternate worldview.
Why it matters: The internet is a major recruitment and organizational tool for extremist groups. Rather than count on websites to police themselves, Moonshot aims to temper extremists' ability to find that content. Based on Moonshot's numbers, there's reason to hope that someone can head would-be extremists off at the pass or even direct them to help, including mental health programs, an option they tested.
The effect: Moonshot’s redirecting strategy worked on 1,300 people out of 56,000 attempts. That's a fairly strong outcome — 20% more effective than the average ad on Google search.
The mental health option: Moonshot also experimented with offering ads for mental health services to those searching for extremist content. It appears to be a viable option. Their targets were 48% more likely to click on an add for psychiatric support than a control group. Those searching for the most violent content clicked on the ad 115% more often.
The big picture: Redirecting a person once does not inherently mean they will be dissuaded from seeking extremist material again. However, many former extremists say that mental health and social work were critical to leave violent movements. But while Moonshot is still tinkering with the content on the other end of their ads, it all means nothing if the ads don't work — which they appear to.
2. Tom Ridge: Election security is not the only security
Photo illustration: Axios Visuals
Election security is sucking up all the oxygen in policy conversations these days. As a result, the first secretary of the Department of Homeland Security worries Congress is letting other aspects of cybersecurity slip through the cracks.
“We should be as obsessed with cybersecurity as we are with elections,” said former Secretary Tom Ridge, also a former Pennsylvania Governor and a recent add to the board of alliantgroup, which helps find tax rebates for cybersecurity firms.
Economic security: “No one thinks democracy is as important as Tom Ridge,” he told me, “but our economic security is at stake.“
- Ridge worries that broad cybersecurity threats to businesses and critical infrastructure are being thrust to the wayside while lawmakers focus most of their attention on election security.
- He believes lawmakers will need to focus on more than one aspect of cybersecurity at a time, which has so far been a difficult ask.
- To wit: A few years ago, automotive hacking was the hip topic for legislation, but faded into the background when election hacking stole most of the attention. Election hacking even swallowed up the next major breach as well, even though Equifax's massive scope seemed tailor-made to spur legislation.
Homeland has no real home: Jurisdictional problems make legislation even more difficult, said Ridge. Despite having a committee called the Homeland Security Committee, every committee maintains an interest in the security of whatever it is it discusses. “Government wasn’t designed to regulate security,” he said. “I spent more time on The Hill talking to committees than Donald Rumsfeld, and the DOD had two wars going on.”
3. Be careful with rumors on Facebook and ICE
A Monday Intercept piece about an ICE investigation involving Facebook spawned spate of headlines like "ICE accused of using Facebook to track undocumented immigrants." The Intercept piece doesn't actually show that.
Here's why.
The background: The Intercept found emails and evidence in a public records request that ICE agents had used data from Facebook to track a suspect. The story would later be updated with a statement from Facebook that it had responded to a lawful government request for information on a man being investigated as a active child predator.
Active child predators and undocumented immigrants are not the same thing: A correction to the story reads "The documents reported on in the story do not establish that the target of the investigation was an immigrant or that the individual was being pursued for immigration violations."
One more drip in Facebook's water torture: Facebook is drowning in data privacy scandals, including whether it should have done more to prevent Cambridge Analytica from fraudulently acquiring user data.
- Big tech firms, including Facebook, Microsoft and Google are actually fairly diligent about defending users from improper warrants.
- Depending on who you ask, this may be a less than ideal arrangement — privacy advocates say it forces users to count on corporations to protect their privacy.
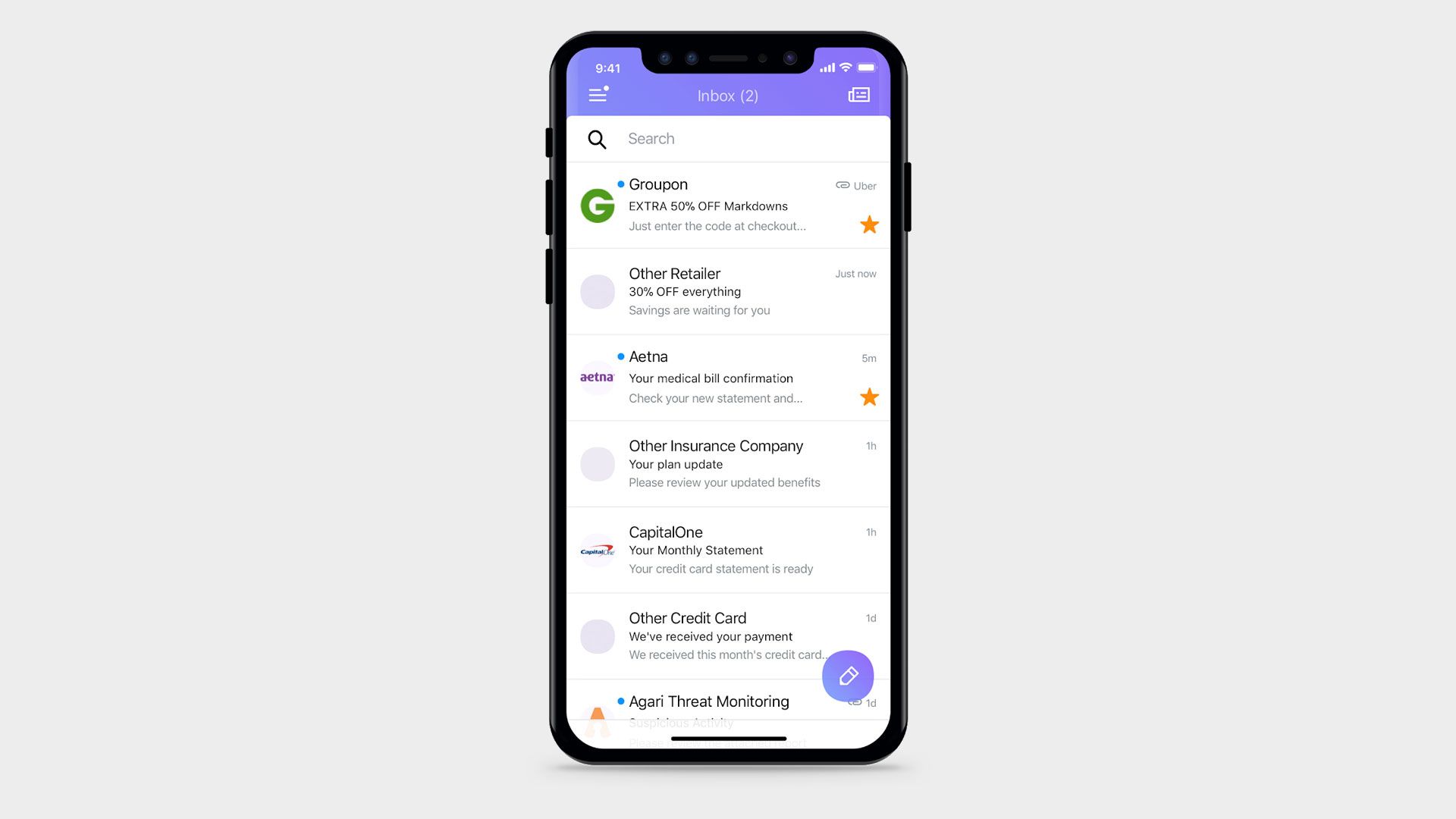
4. Google, Microsoft, Comcast team up for anti-fraud email standard
Courtesy of Agari
You probably take for granted that this email, sent from an Axios email address, came from Axios (it did!). For lay users, it's difficult to tell if an email is authentic. A new email security standard being rolled out today aims to address that.
Email security firm Agari announced a new email security standard that'll make it easier for users to tell which emails came from authentic sources. Comcast, Google, Microsoft and Yahoo worked on the standard, and a pilot test will run on Yahoo's platform.
Why it matters: Email wasn’t designed with security in mind. When an email says it is from your bank, the email standard doesn’t do anything to authenticate whether the email actually came from the bank or from someone pretending to be the bank.
The old way to prevent fraudulent email: There is an add-on standard that many service providers use, known as DMARC, that double checks with the sender’s email server that an email is authentic. Many organizations, including governments and major corporations, don’t use DMARC, although adoption is growing. That might be little comfort to users, most of whom do not how to tell if that system was in effect.
Enter BIMI: The new standard, Brand Indicators for Message Identification (or BIMI) places a visual cue — a company logo — over an email. Not only will it help people know when an email has been authenticated, but it will “absolutely boost adoption,” said Agari co-founder Patrick Peterson.
- Peterson believes it will blend a branding opportunity with a chance to signal good security practices, something irresistible to marketing departments even when the message didn't hit home with security teams.
Editor's note: An earlier version of this story incorrectly said Google, Microsoft and Comcast were involved in the trial when they were only involved in the standard.
5. DHS adds former EAC chair as new election cybersecurity advisor
Matt Masterson, the most recent chairman of the Election Assistance Commission (EAC), has been added as an election cybersecurity advisor to the Department of Homeland Security’s National Protection and Programs Directorate. Congress and the Trump administration recently decided not to take Masterson on for another term at EAC.
Why it matters: Masterson is a well-liked figure in election security circles, known for conducting thorough outreach with the states on cybersecurity and for listening to cybersecurity experts after years of them being viewed as a nuisance. Just hiring the man — even before he does any actual work — is a useful signal to those communities.
6. Odds and ends
- Europol confirms the arrest of the suspected leader of the Carbanak group. Carbanak ATM malware and it’s later replacement, Cobolt, netted $1.2 billion over five years. (Europol)
- Researchers found even more CPU security flaws similar to Specter. (Ars Technica).
- A Trump ally is suing Qatar for allegedly hacking his emails and smearing him in the press. (Axios)
- Mozilla, maker of the web browser Firefox, launched an extension to up Facebook privacy. (Mozilla)
- The U.S. Digital Service is humming along in the Trump administration, per a new report. (Axios)
- The RSA security conference added some female keynote speakers after criticism for under representation. (Axios)
- The ultra-hard-to-track cryptocurrency Monero isn't actually quite that hard to track. (Wired)
- The director of Harvard's Belfer Center cybersecurity center argues the U.S. use offensive hacking to cut off other nations attacks. (Foreign Affairs)
Thanks for reading. Remember, if you keep this email in good condition, one day it will be a collectors item. Our next issue will be on Thursday. See you then!
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.