Axios Codebook

January 31, 2023
Happy Tuesday! Welcome back to Codebook.
- I'm truly devastated by the news that Philz Coffee is leaving the D.C. market. Sure, it's just a simple drip coffee shop, but I appreciate the simplicity!
- 📬 Have thoughts, feedback or scoops to share? [email protected]
Today's newsletter is 1,317 words, a 5-minute read.
1 big thing: FBI reaches out to ransomware victims
Illustration: Sarah Grillo/Axios
The Justice Department's recent, historic operation that thwarted a notorious ransomware gang came with a barely coded messaged: More ransomware victims should call the FBI.
Why it matters: Targets of ransomware and other malicious cyber incidents often fear that if they call the FBI, they'll have to give agents overly broad network access, they'll be named in future litigation, or the attackers will leak sensitive information.
- Federal officials have spent the last few years trying to assuage those concerns as government investments in anti-ransomware initiatives have grown.
Driving the news: Last week, the DOJ unveiled a monthslong operation where FBI agents invaded the Hive ransomware gang's darknet operations. Officials stole and distributed decryption keys to hundreds of victims mid-attack and ultimately shut down some of the gang's key digital infrastructure.
- Most of Hive's victims were U.S. schools, hospitals and other critical infrastructure organizations.
The big picture: At a press conference detailing the campaign, FBI director Christopher Wray estimated that only 20% of Hive's victims reported potential issues to law enforcement during the bureau's seven-month operation.
- Experts told Axios that the speedy assistance officials shared last week could help encourage more ransomware targets to call the FBI when they're attacked.
Flashback: The FBI's quick deployment of a Hive decryption key to victims during the sting operation is a complete 180-degree turn from a similar operation the bureau handled nearly two years ago.
- In 2021, the FBI reportedly held on to a decryption key tied to the massive, ongoing Kaseya ransomware attack for nearly three weeks before handing it out to the hundreds of victim organizations.
Between the lines: Misconceptions about how the FBI and other federal investigators, including those at the Cybersecurity and Infrastructure Security Agency, handle ransomware investigations have led to industry distrust, Adam Flatley, vice president of intelligence at cyber defense firm Redacted, told Axios.
- Many organizations think federal investigators will overrun their internal investigations, but the FBI typically just wants to identify the perpetrators and recover any financial losses, Flatley said.
- While many ransomware gangs threaten victims to not call the feds, the Hive operation shows the FBI is capable of discreetly helping victims, Flatley added.
The intrigue: Helping more ransomware victims also helps the FBI to track trending cyber threats that could pose a broader national security risk to the country.
But many ransomware victims also might not consider calling federal investigators during an incident, Austin Berglas, global head of professional services at BlueVoyant and a former FBI agent, told Axios.
- "If your house is burning, you're doing whatever it takes to make sure that your business stays afloat," Berglas said. "Calling law enforcement is the last thing you're thinking about."
- About 45% of cyber professionals also think calling in law enforcement would slow down data recovery and distract their companies' IT teams, according to a 2021 survey from cybersecurity firm Talion.
Yes, but: While Wray's estimate of 20% might seem low, former agents and officials told Axios that number was a lot higher than they'd expected.
- Critical infrastructure, in particular, has gotten a lot better at calling in the FBI because of the concerted government outreach targeting them in recent years, Berglas said.
Of note: FBI cyber field agents across the country are often looking to meet nearby companies to help establish a relationship before an incident happens.
What's next: All eyes are on how CISA enacts forthcoming cyber incident reporting laws and whether those will help connect ransomware victims with law enforcement resources faster — or disrupt the budding trust being built between industry and federal investigators.
2. New malware targeted Ukrainian energy sector
Illustration: Megan Robinson/Axios
Suspected Russian hackers deployed a new malware wiper against a Ukrainian energy sector company right as Russian armed forces started launching missiles against Ukraine's broader energy infrastructure late last year.
Driving the news: Researchers at Slovakian cyber company ESET found in a report released today that Russian state-sponsored hacking group Sandworm targeted the unnamed company in October with a data-wiping malware.
- ESET researchers have named the new malware strain "NikoWiper," and it's based on SDelete, a Microsoft utility tool used to delete files.
Why it matters: While the Russian "cyber Armageddon" expected during the war in Ukraine hasn't happened, the new finding underscores how Russian military forces and hacking groups continue to share similar goals, the report notes.
Flashback: Russian hackers have routinely tied their malware and phishing attacks to larger, kinetic warfare in the last year.
- For instance, the day before the invasion began, Russia knocked several Ukrainian government websites and banks offline.
The big picture: News of October's seemingly coordinated attack comes amid renewed concerns this week about Russian cyberattacks on Western critical infrastructure.
- Last week, Russian hacktivist group Killnet threatened retaliatory attacks against German organizations after the German government promised to send new tanks to Ukraine.
- Killnet also spent the weekend threatening a longer list of Western organizations in its public Telegram channel — including medical organizations across the U.K., Finland, Norway, Poland, the Netherlands and the U.S.
- Yes, but: It appears Killnet hasn't followed through on any of those threats yet.
3. A different type of hiring spree
Illustration: Allie Carl/Axios
Developers are the most in-demand roles on the dark web, according to recent research from Russian cyber firm Kaspersky.
Driving the news: Kaspersky's analysis of job advertisements posted on dark web forums between January 2020 and June 2022 found that some cybercrime and state-sponsored hacking groups were offering developers upward of $20,000 a month to join their ranks.
- Job ads for developers made up 61% of posts researchers spotted across 155 dark web forums.
The big picture: Cybercriminals and state-backed hacking groups have become increasingly organized in recent years.
- Some groups even mimic professional organizations by conducting job interviews and creating an HR department.
Between the lines: The analysis paints a clearer picture of why some hackers end up being tempted to cross over to malicious work.
Details: Kaspersky analyzed approximately 200,000 employment-related ads posted during the year-and-a-half period.
- Posts peaked in March 2020, as the coronavirus pandemic began, likely due to soaring unemployment rates at the time.
- 82% of relevant advertisements mentioned "test assessments" candidates would have to take, and 37% requested people submit a CV or portfolio.
- Median monthly salaries ranged from $1,300 to $4,000 depending on the role.
- 17% of the job ads were people looking for jobs, rather than groups looking to hire someone.
The intrigue: While Kaspersky analyzed only IT-related jobs, researchers also spotted ads for nontechnical positions — including one moderating a group's Telegram channel.
Yes, but: Not all of the job listings were necessarily criminal or illicit, Kaspersky researchers noted.
- "Most dark web employers offer semi-legal and illegal jobs, but there are ads with potentially legal job offers that comply with national laws," researchers wrote. "An example is creating IT learning courses."
4. Catch up quick
@ D.C.
🛑 The Commerce Department has reportedly stopped providing licenses to U.S. companies to sell equipment to Huawei. (Financial Times)
🏛 TikTok's CEO will testify before Congress in March amid mounting national security concerns. (Axios)
👨🏻⚖️ Rep. Andrew Garbarino (R-N.Y.) is the new chair of the House Homeland Security Committee's cyber subcommittee. (The Record)
@ Industry
📈 Microsoft surpassed $20 billion in revenue from its cybersecurity business in the last 12 months. (Cybersecurity Dive)
👀 Critical infrastructure companies warn their suppliers are increasingly becoming vulnerable cyber threats. (Wall Street Journal)
📲 A look at the new, enhanced privacy settings on iPhones to guide who should use them and when. (Washington Post)
@ Hackers and hacks
👾 A bug in Meta's centralized login system could allow malicious hackers to bypass two-factor authentication. (TechCrunch)
🇬🇧 The Hackney Council, a local government authority in East London, is still struggling to recover from a ransomware attack — more than two years later. (Wired)
5. 1 fun thing
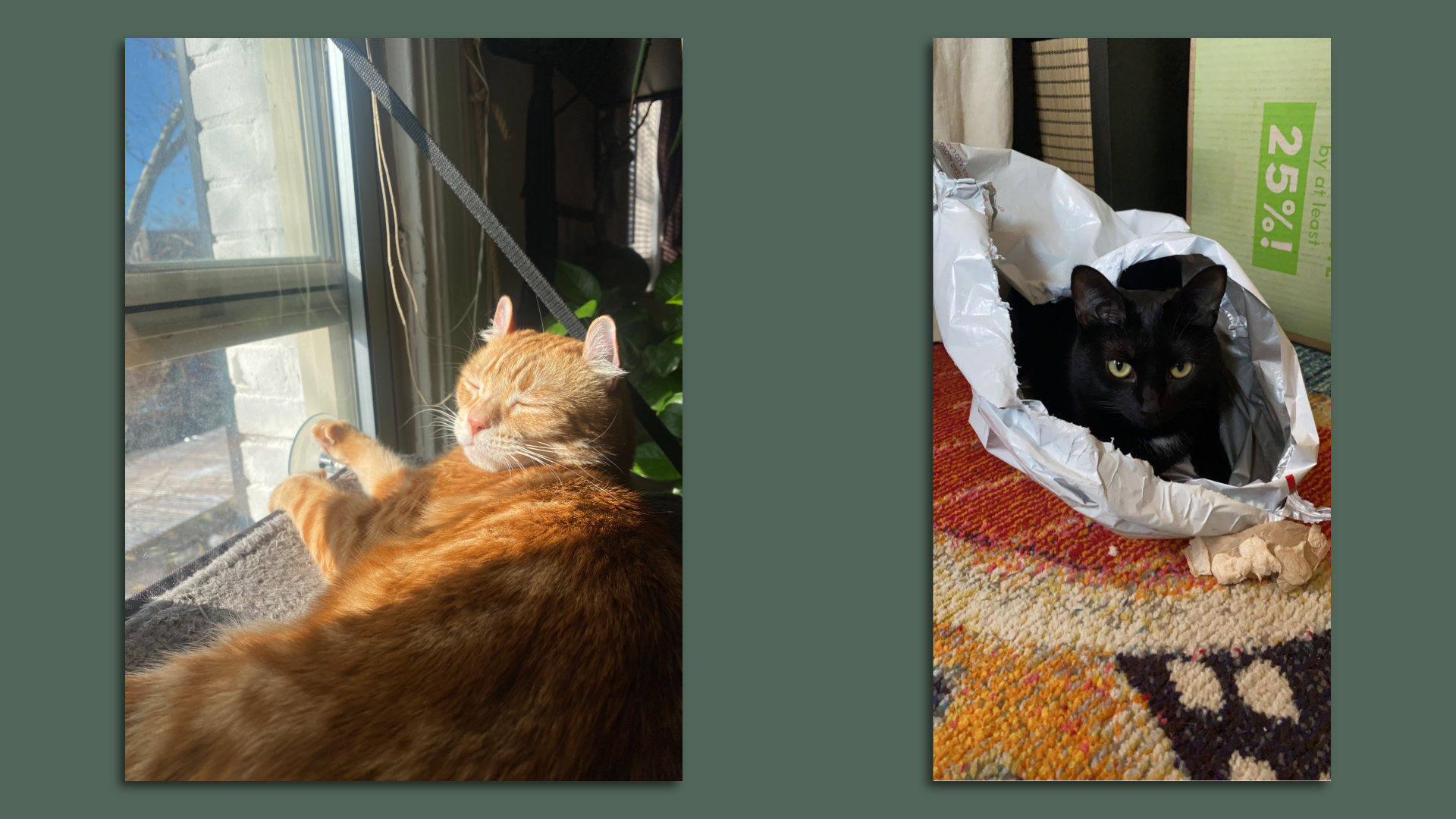
Your Codebook host's two cats — Barry (left) and Lola (right) — seen sunbathing and recycling, respectively. Photo: Sam Sabin/Axios
It's been a tough few days in the world — here's some Barry and Lola content to bring some joy to your day 🥰.
- And I wouldn't be mad if you all responded with your own pet pics 👀.
☀️ See y'all on Friday!
Thanks to Peter Allen Clark for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.