Axios Codebook

April 28, 2023
😎 TGIF, everyone. Welcome back to Codebook.
- 🥱 You're forgiven if you're reading this email while still in your PJs after a jampacked RSA.
- 📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,438 words, a 5.5-minute read.
1 big thing: The Biden cybersecurity team's united front
Illustration: Shoshana Gordon/Axios
The Biden administration's cyber team arrived at RSA with — for the first time — a clear message about how each agency approaches the government's vast cyber mission.
Why it matters: That team hasn't felt so united in recent months, with reports of bickering between two top White House cyber officials, the recent departure of the first-ever national cyber director, and stories about disgruntlement inside the country's top cybersecurity agency.
- But at RSA, officials brushed off those concerns and presented what could be the clearest picture yet of the Biden administration's new cyber offices and their responsibilities.
The big picture: Since President Joe Biden took office, his administration has created at least three new high-ranking cyber roles:
- Congress created the Office of the National Cyber Director right as the Biden administration started.
- Biden's White House established a new cyber-focused deputy national security adviser role inside the National Security Council, which Anne Neuberger now holds.
- And the State Department established a new ambassador at large position for cyberspace and digital policy last year. Nathaniel Fick was sworn in as the title's first holder in September.
Between the lines: The creation of so many new cyber offices in such a short time — on top of the continued expansion of the Cybersecurity and Infrastructure Security Agency — caused confusion among policymakers, executives and their lobbyists about who they should turn to in the event of a major cyber incident.
What they're saying: "We're two grownups working in the White House on the same issue, and there's plenty to go around," acting national cyber director Kemba Walden told Axios about her relationship with Neuberger during a press roundtable at RSA.
- "There's genuinely plenty of work to go around, and I'm just grateful that we have smart leaders that are thinking about this thoughtfully and who are passionate," she added.
Zoom in: Walden and her team weren't the only ones in San Francisco trying to clarify their role in the Biden administration's cyber vision this week.
- CISA appeared on several panels and at events that established the agency as the clear intermediary between private companies and the U.S. government when attacks happen or new threat intelligence pops up.
- Fick appeared on a panel that highlighted his office's facilitation role between U.S. entities and international allies on all cyber issues — including everything from cyber aid to Ukraine to standards-setting for 5G deployment.
- The White House, primarily through Walden's office, showed that it's now the go-to for cyber policymaking and government coordination — especially with regard to the national cyber strategy and regulating critical infrastructure.
- The National Security Agency and the U.S. Cyber Command are the primary sources for intelligence about cybercriminals and nation-state actors, and the offices are sharing this data more with their agency partners.
Yes, but: It remains to be seen how sturdy these definitions will be in practice.
- The White House's two cybersecurity offices have overlapped on some policymaking decisions, such as the creation of the national cyber strategy, as Bloomberg detailed.
- An NSC spokesperson told Axios that Neuberger's position "coordinates across all departments and agencies, developing and implementing policy focused on defensive and offensive cyber and emerging technology."
- Meanwhile, CISA, the NSA and State each coordinate with their international counterparts on various issues, from threat intelligence sharing to the establishment of secure-by-design principles.
2. 💬 Overheard at RSA
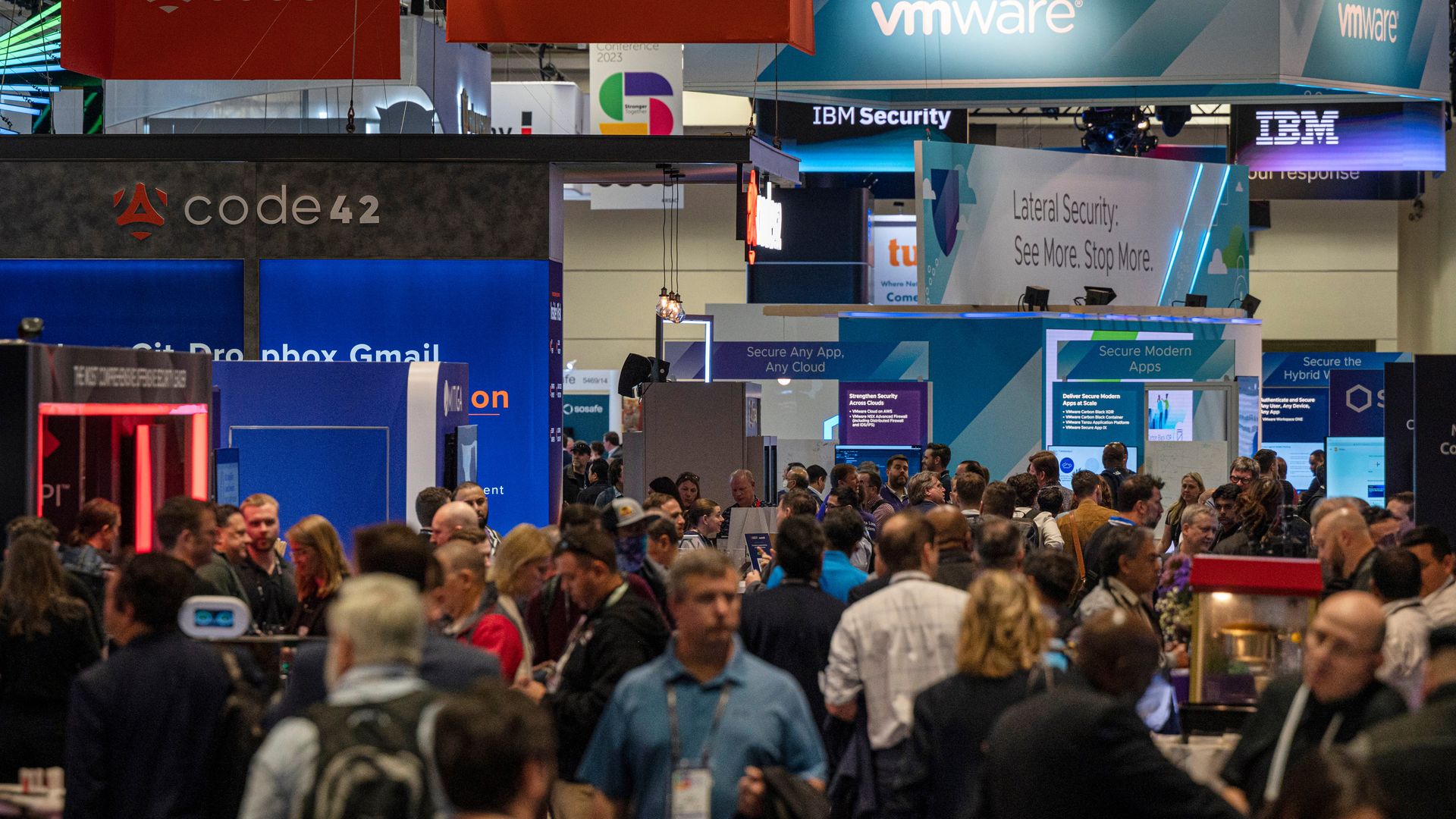
Attendees walk the floor during RSA on Wednesday. Photo: David Paul Morris/Bloomberg via Getty Images
Plenty of AI hype, doomsday analyses, and helpful tips and tricks flooded our brains at RSA. Here are some of the takeaways from convos throughout the week:
👀 Mandiant is side-eyeing the teens.
- "There's a group of teenagers and folks in their 20s that live in the United States, live in the United Kingdom, and typically speak English as their first language that are incredibly effective social engineers," Charles Carmakal, chief technology officer at Mandiant, told reporters Monday.
- "We've seen very young individuals break into some of the biggest organizations by leveraging these techniques that are so hard to defend against," he added.
- Yes, but: Not everyone agrees. "I don't fear the teenagers necessarily," Chester Wisniewski, field CTO of applied research at Sophos, told Axios. "It's not a good trend, but teenagers are going to get into trouble no matter what."
🤖 People are already exhausted from the ChatGPT hype cycle.
- "I'm sure it will eventually be included in malicious campaigns we're seeing, but I think a few people are a bit too trigger-happy on this one," Jean-Ian Boutin, ESET's director of threat research, told Axios.
- "I don't think we're at that inflection point where it's going to take over and the attackers are just going to be able to automate cybercrime," John Dwyer, head of research at IBM Security X-Force, told Axios.
🇮🇱 The U.S. spyware crackdown — which is likely to impact several Israeli spyware makers — hasn't hindered cyber intel-sharing with Israel.
- "The relationship is still strong and good," Rob Joyce, NSA's director of cybersecurity, told Axios during a press briefing.
- "Our relationship is government-to-government, but the White House and the policymakers have been pretty clear on the proliferation of dangerous cyber tools, and so they're working that across a number of international partners," he added.
3. 🌉 CISA makes the rounds in the Bay Area
Eric Goldstein, CISA's executive assistant director for cybersecurity, answers questions from Axios' Sam Sabin at an Axios event in San Francisco. Photo: Chris Constantine for Axios
The best data the federal government has suggests that only a quarter of cyber incidents are reported to the government, a top cyber official told Axios.
Why it matters: Without those reports to the government, it's much more difficult for the feds to either prosecute cybercriminals or help recover any stolen funds or data from a breach.
- A lack of reporting also skews the government's insights into the prevalence of certain cyber threats.
What's happening: Eric Goldstein, CISA's executive assistant director for cybersecurity, relayed the reporting stat during an Axios event here in San Francisco this week.
- Among those reports to the federal government, only "a tiny fraction" have "usable technical data" from their systems that could be helpful for the Pentagon and law enforcement to track down the malicious actors.
- That's not because of malicious negligence, but because so many organizations lack the visibility they need into their own networks to get that data, Goldstein added.
The big picture: CISA is the private sector's main point of entry into the federal government, and as such, the agency spent most of its trip meeting with the private sector to figure out what's missing and how it can connect with more companies.
- CISA hosted a private roundtable Wednesday with 38 companies to get feedback on how its public-private partnerships are going, as well as to hear what changes companies would like to see from the agency, Goldstein said.
- Throughout RSA, CISA also hosted listening sessions to collect feedback on its recently proposed principles for designing products with security in mind, Goldstein added. Another CISA official told CyberScoop the agency held three listening sessions on the secure-by-design principles — two with industry partners and another with the open-source community.
Between the lines: CISA is also in the middle of creating regulations for enforcing a mandatory cyber incident reporting law that requires critical infrastructure organizations to report significant incidents within 72 hours.
- Such reporting laws could help the government better track threats, as well as require companies to better monitor their own networks.
4. Catch up quick
@ D.C.
🤖 Senate Intelligence Committee Chair Mark Warner (D-Va.) is pushing AI firms to prioritize cybersecurity now before their products become even more popular. (CyberScoop)
🫠 NSA's cyber leader warned that AI's impact on the threat landscape is only just beginning. (Wired)
📲 Washington state is the first to adopt a new law protecting consumer health and location data that could reveal someone is seeking an abortion. (Bloomberg Law)
@ Industry
📦 More than a year later, a logistics company is still dealing with the fallout from a cyberattack that caused system outages. (Wall Street Journal)
📊 Global cyber insurance prices rose by 11% in Q1 2023, compared to 28% at the end of 2022. (Cybersecurity Dive)
@ Hackers and hacks
😵💫 Hackers are getting better at evading endpoint security tools. (Bloomberg)
🍎 Data stolen during the ransomware attack on the Minneapolis Public Schools district earlier this year was posted on Twitter, Facebook and other websites. (NBC News)
5. 1 fun thing
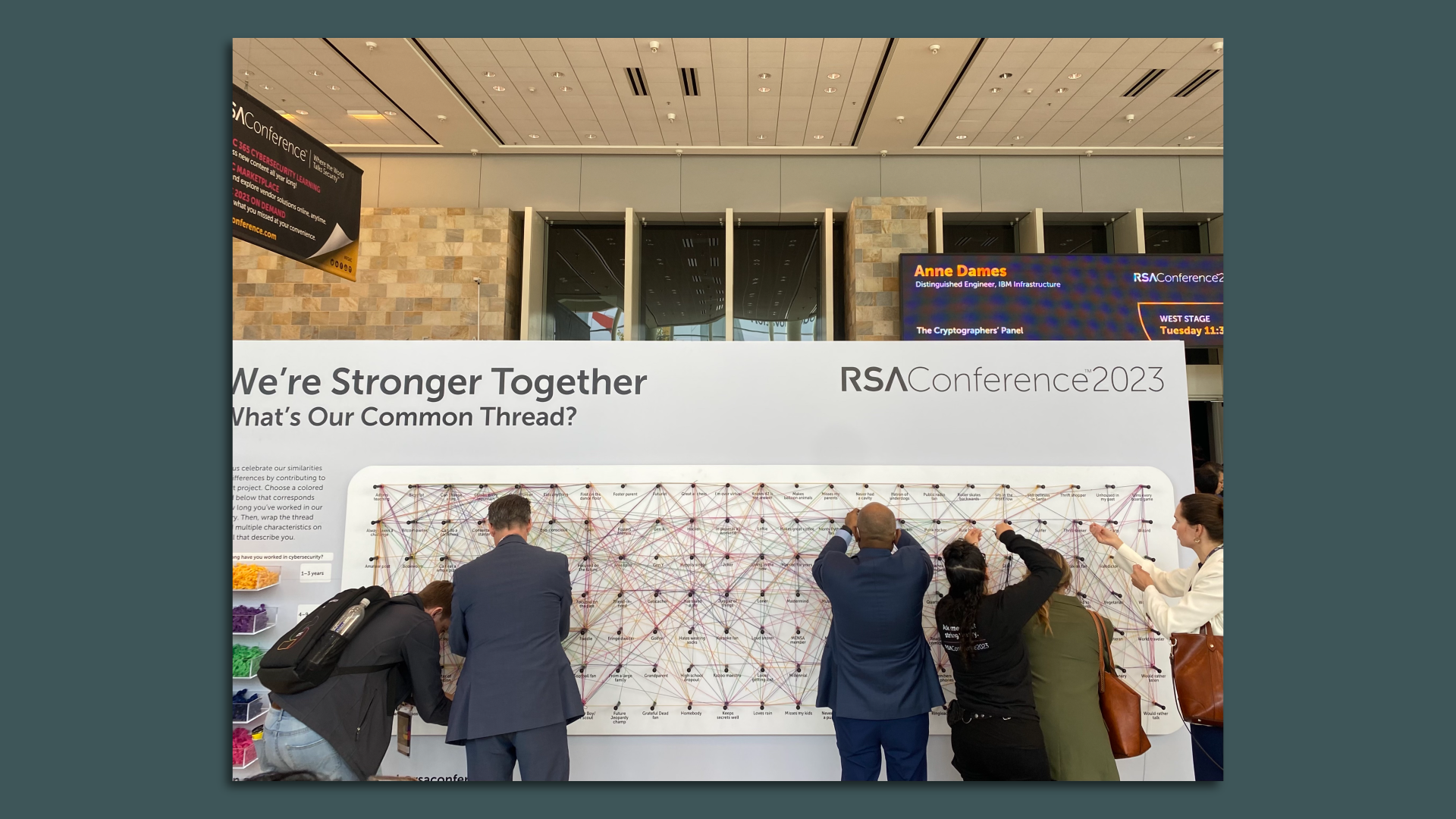
Interactive installation at the 2023 RSA Conference in the Moscone Center. Photo: Sam Sabin/Axios
I really enjoyed watching people fill out this interactive board in the Moscone West convention center throughout the RSA week.
- The board asked people to pick a colored thread based on how many years they've been in cybersecurity: Yellow for one to three years of experience, purple for four to nine years, green for 10 to 14 years, and so on.
- From there, people wrapped the thread around several characteristics that described themselves, which included a range of things like "amateur poet," "bad at math" and "Bitcoin owner."
✈️ See y'all on Tuesday!
Thanks to Scott Rosenberg for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.