Hackers target African banks using North Korean tactics
Add Axios as your preferred source to
see more of our stories on Google.
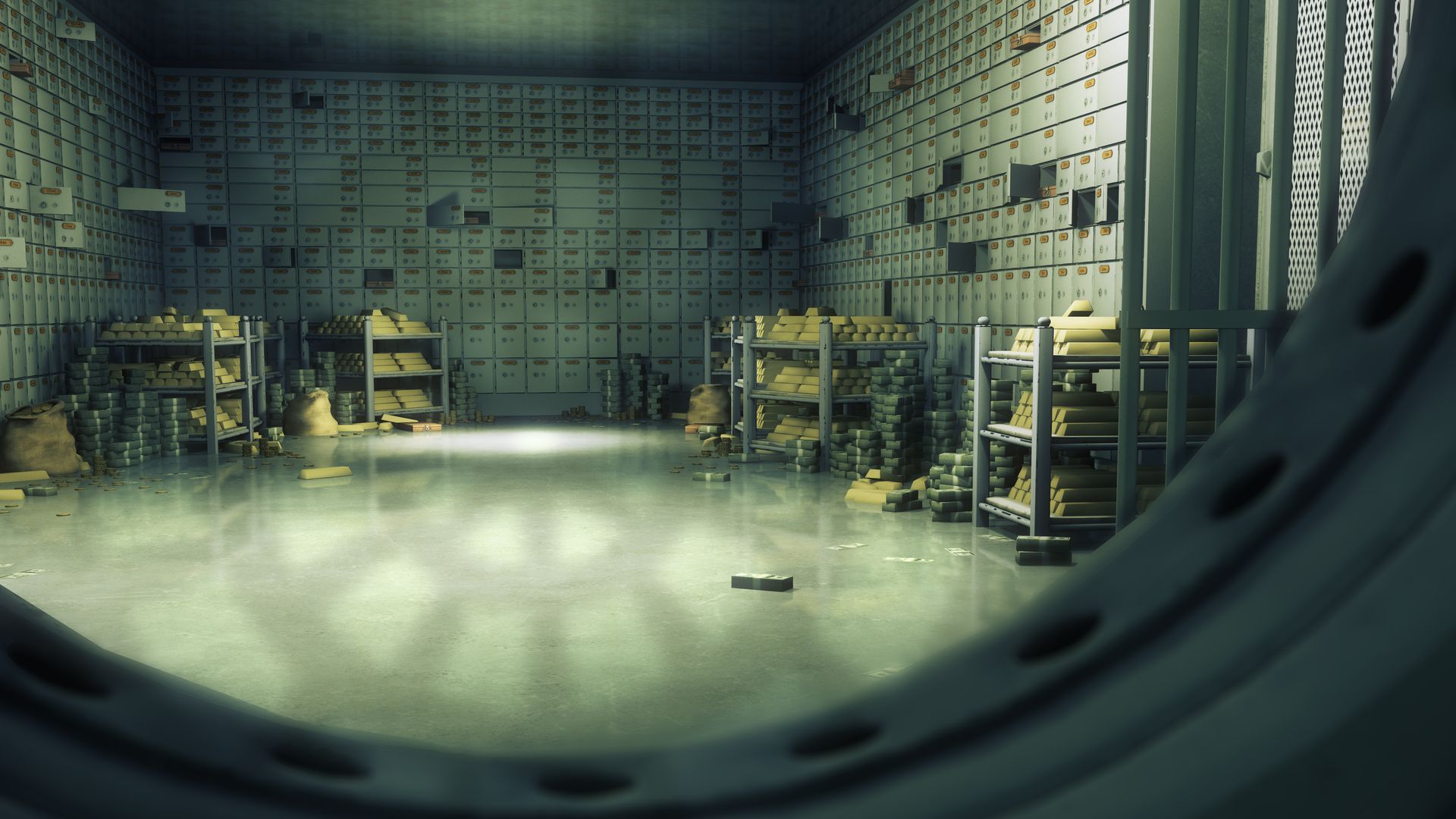
Bank vault. Photo: Matjaz Slanic/Getty Images
A cluster of attempted digital robberies at West African financial institutions appear to have been imitating the North Korea-linked Lazarus Group's run of heists, according to Symantec.
Why it matters: Lazarus, internationally notorious for the Sony hack and the WannaCry malware, is currently very active stealing funds to support the Kim Jong-un regime. The Symantec finding is fascinating as an example of how attacks trickle down from nations to more common criminals.
The big picture: "It seems like after the high public profile of the North Korea thefts, these hackers took those tactics," said Jon DiMaggio, a senior threat intelligence analyst at Symantec.
Details:
- The Lazarus group has utilized the SWIFT system, which banks use to request money from one another, in several high-profile thefts, but the attacks Symantec documented did not.
- What they did use were a similar set of tools to what Lazarus used to set up those attacks, as outlined in a 2017 alert.
- Symantec did not want to publicly specify the exact tools that were used.
Background: This isn't the first time DiMaggio said he had seen hackers influenced by a high-profile Lazarus attack. After the group's most famous heist, the theft of $81 million from the central bank of Bangladesh, a separate criminal group added SWIFT fraud to their toolkit.
Symantec's report outlined four different techniques of attacks currently being used in Africa that may represent more than one criminal group.
- The first, the one flagged as similar to the SWIFT heists, targeted firms in Ivory Coast and Equatorial Guinea.
- All four clusters used a mix of easily purchasable malware and "living off the land" techniques — avoiding detection using as much software already on victims' computers during the break-in as possible.
- The other groups of attacks spanned Ivory Coast, Ghana, the Democratic Republic of the Congo and Cameroon.
Historically, West African financial groups have not been common targets for hackers, according to the Symantec report. DiMaggio believes that a softer regulatory structure may have made African banks a tempting target.
The bottom line: DiMaggio stressed that IT staff globally have to become more accustomed to looking for living-off-the-land attacks that don't appear to create suspicious network traffic. "You have to look at legitimate traffic," he said. "You can't just wait for a warning screen to flash red."
