Go deeper: Bloomberg's fraying "secret chips" story
Add Axios as your preferred source to
see more of our stories on Google.
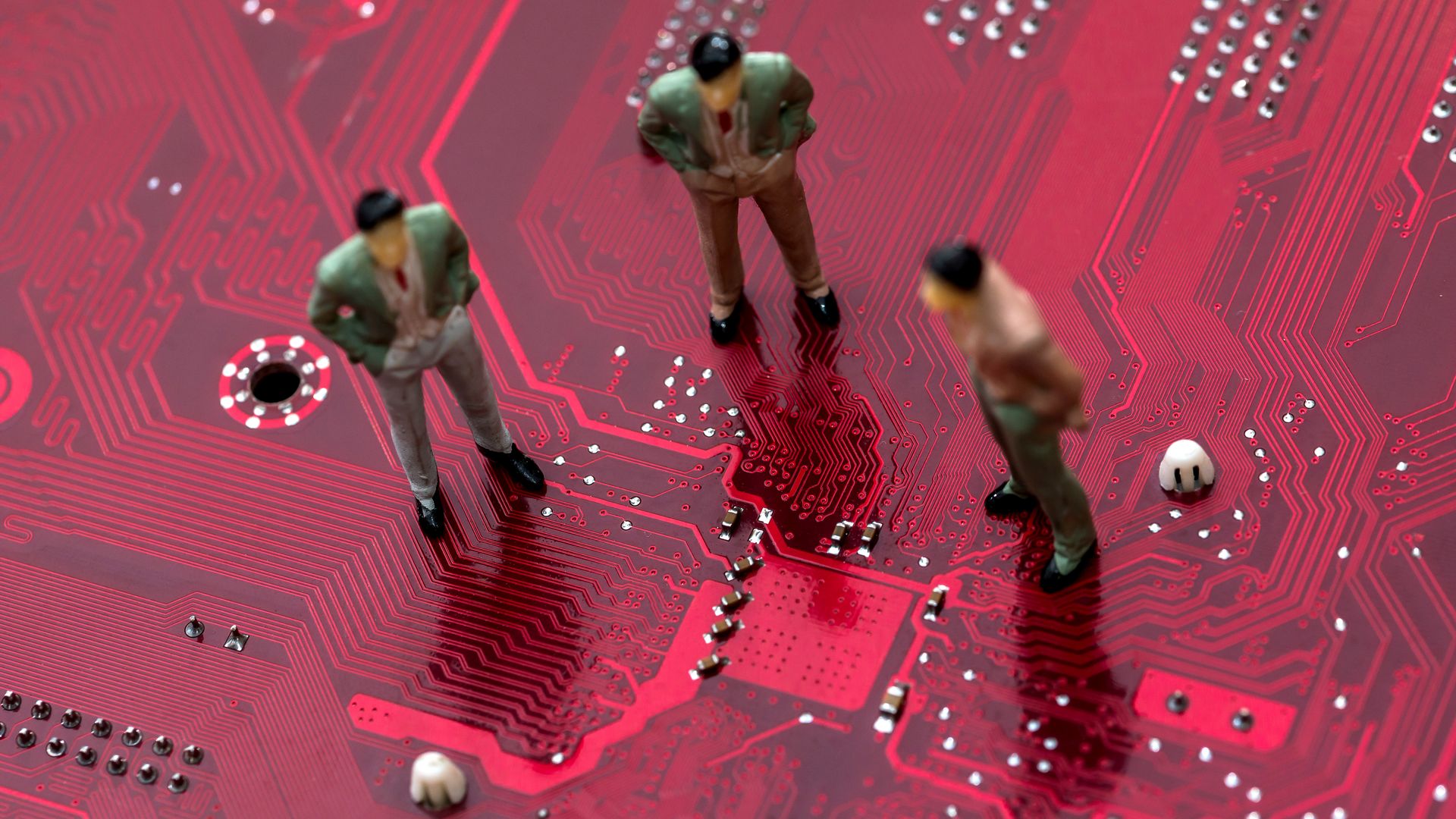
Photo: Alfexe/via Getty Images
Last Thursday Bloomberg reported that authorities were investigating Supermicro, which manufactures server motherboards, for shipping equipment implanted with chips that China could use to spy on users.
The big picture: The piece was a bombshell, but a raft of vehement denials from everyone involved — including Apple and Amazon, which Bloomberg claimed discovered the secret chips in their own servers — has made the story increasingly hard to believe.
Why it matters: If the piece is a mistake, it is not a small one. Shares in Supermicro stock dropped more than 50% after the story, wiping away nearly $600 million in market cap. But this isn’t just about one firm’s fortunes — the kind of sabotage described in the story, if real, could compromise major institutions.
- Supermicro products — and the web and cloud services fueled by them — are used by defense, banks, hospitals and other groups.
- A state election official who spoke to Codebook was concerned that state accounts might have been made vulnerable to attack.
It's hard to believe that Amazon, Apple and Supermicro are all fabricating their emphatic denials of the Bloomberg story.
- Some users dismissed the denials on Twitter, declaring “I can’t trust corporations” — a distrust that many tech companies have brought upon themselves.
- But lawyers who spoke to Codebook said the detailed denials wouldn’t just be a public relations issue if incorrect or fudged.
- “The companies [would] risk enforcement by the FTC for engaging in a deceptive act that is likely to harm consumers,” emailed David Vladeck, Georgetown professor and former head of the Federal Trade Commission’s Bureau of Consumer Protection, adding, “I am strongly disinclined to think they are lying.”
- Apple would only have compounded its woes Monday by repeating its claims in a letter to two congressional committees.
- Homeland Security and the British cybersecurity office, the National Cyber Security Centre also denied knowledge of Bloomberg’s claims.
The big question: Flustered cybersecurity pros have been left wondering how much of the story is accurate. The expert consensus is that it's more likely that Bloomberg is wrong than that the companies and government agencies are lying.
- One key voice disapproving of the piece is security researcher Joe FitzPatrick, who is quoted in the story. According to the Risky Business podcast, FitzPatrick says he emailed Bloomberg before the article was published that their story "didn't make sense."
Bloomberg noted in a statement sent to Codebook Tuesday that Joe FitzPatrick had no direct knowledge that the story was incorrect.
- "The specific ways the implant worked were described, confirmed, and elaborated on by our primary sources who have direct knowledge of the compromised Supermicro hardware. Joe FitzPatrick was not one of these 17 individual primary sources that included company insiders and government officials, and his direct quote in the story describes a hypothetical example of how a hardware attack might play out, as the story makes clear."
Early Friday, one lawmaker’s office hinted to Codebook that Bloomberg's article might be accurate — but backtracked later in the day. Also on Friday, Sen. Gary Peters (Mich.) sent a letter to Secretary of Defense Jim Mattis asking about armed forces’ knowledge and exposure.
Our thought bubble: It’s possible that well-meaning sources confused malware Apple reportedly found in Supermicro firmware with a hardware-based espionage campaign. The two are not equivalent — the firmware problem was quickly dealt with.
Glass houses disclaimer: Reporters make mistakes. Codebook makes mistakes. Sources are sometimes wrong. And good journalism often necessitates anonymous sources.
Editor's note: This story has been updated with new comment from Bloomberg.
