Russian SolarWinds hackers are back, Microsoft warns
Add Axios as your preferred source to
see more of our stories on Google.

Russian President Vladimir Putin during a video message to the Russian Congress on May 27. Photo: Sergei Ilyin/AFP via Getty Image
The same Russian hackers behind the massive SolarWinds breach have launched a new wave of cyberattacks targeting government agencies, think tanks, consultants and NGOs, Microsoft disclosed late Thursday night.
Why it matters: The revelation of the ongoing attack comes less than two months after the U.S. imposed sanctions and expelled Russian diplomats in response to the SolarWinds hack, described by Microsoft as the "most sophisticated attack the world has ever seen."
- The new breach was discovered just weeks before President Biden is set to hold his first in-person summit with Russian President Vladimir Putin in Geneva, and comes on the heels of other Russian-backed cyber espionage campaigns.
Microsoft said the hacking group Nobelium, which is linked to Russia’s main intelligence agency, was behind the attack.
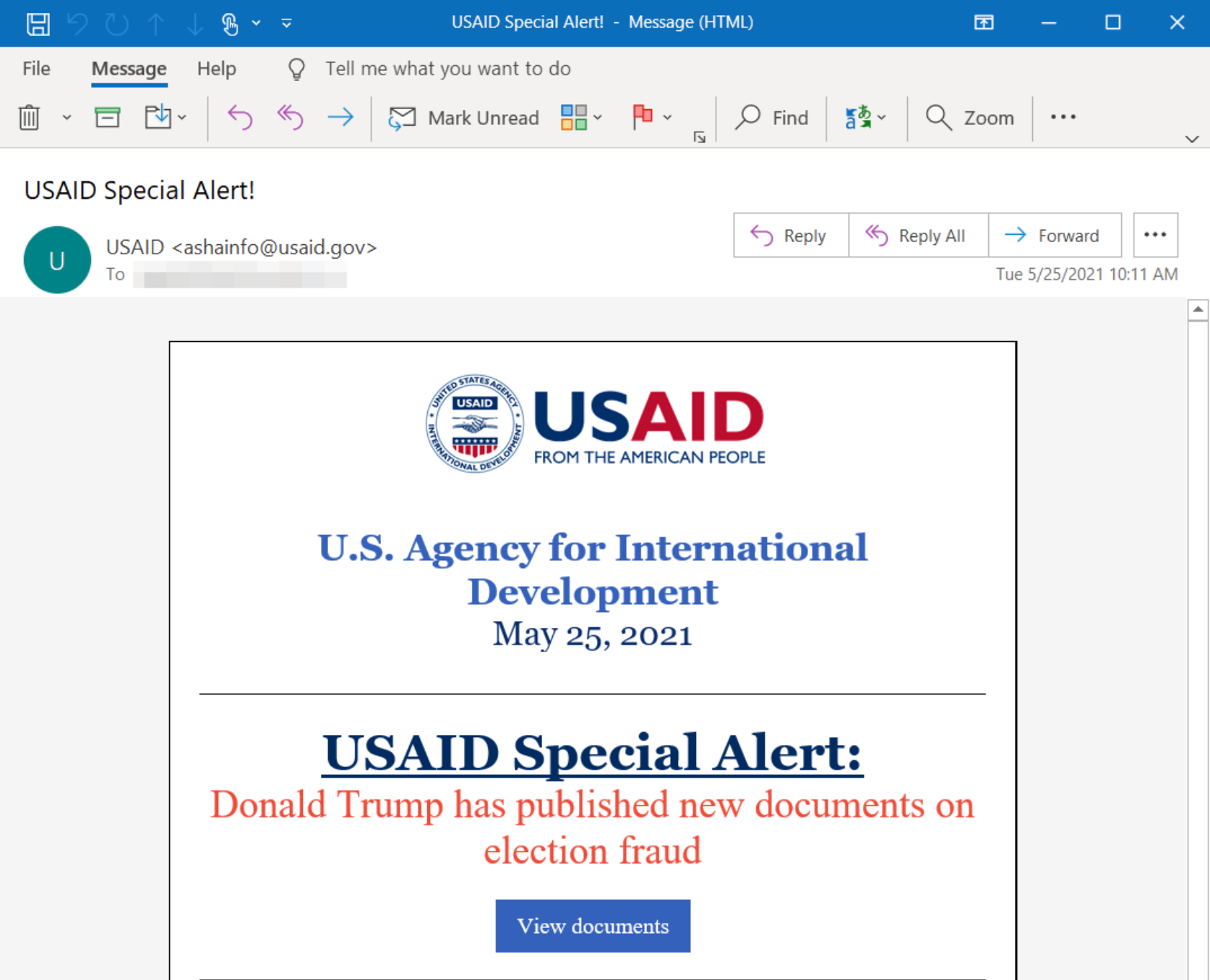
- The Kremlin-linked hacking group took control of a U.S. Agency for International Development account and sent legitimate-looking emails containing malicious files to international human rights groups and humanitarian organizations, according to Microsoft.
- Microsoft, which monitors for malicious activity on the internet, said this attack "differs significantly" from the SolarWinds breach, with the hackers appearing to use newer tools and tradecraft.
How it works: Nobelium gained access to USAID's Constant Contact email marketing account, allowing the group to send malicious emails that appeared to come from genuine government addresses to 3,000 emails across more than 150 organizations.
- The emails contained a "backdoor" through which the hacks could steal data and infect other computers on a network. Some of the emails were flagged by automated email threat detection systems, but some may have been successfully delivered.
- Many of the organizations targeted have been critical of Putin and have revealed and condemned Russian action against dissidents, including the poisoning and jailing of opposition leader, Alexei Navalny, according to the New York Times.
What they're saying: A spokesperson for the Cybersecurity and Infrastructure Security Agency told the Times Thursday that the agency was “aware of the potential compromise, and that it was working with USAID and the FBI "to better understand the extent of the compromise and assist potential victims.”
- "First, when coupled with the attack on SolarWinds, it’s clear that part of Nobelium’s playbook is to gain access to trusted technology providers and infect their customers," Tom Burt, a Microsoft vice president, wrote in a blog post Thursday.
- "By piggybacking on software updates and now mass email providers, Nobelium increases the chances of collateral damage in espionage operations and undermines trust in the technology ecosystem," Burt added.
- “At least a quarter of the targeted organizations were involved in international development, humanitarian, and human rights work."
The big picture: The attack suggests Russia is not slowing its hacking campaigns against the U.S. government and U.S.-based companies, despite new sanctions.
