AMD chip flaw disclosure report met with industry skepticism
Add Axios as your preferred source to
see more of our stories on Google.
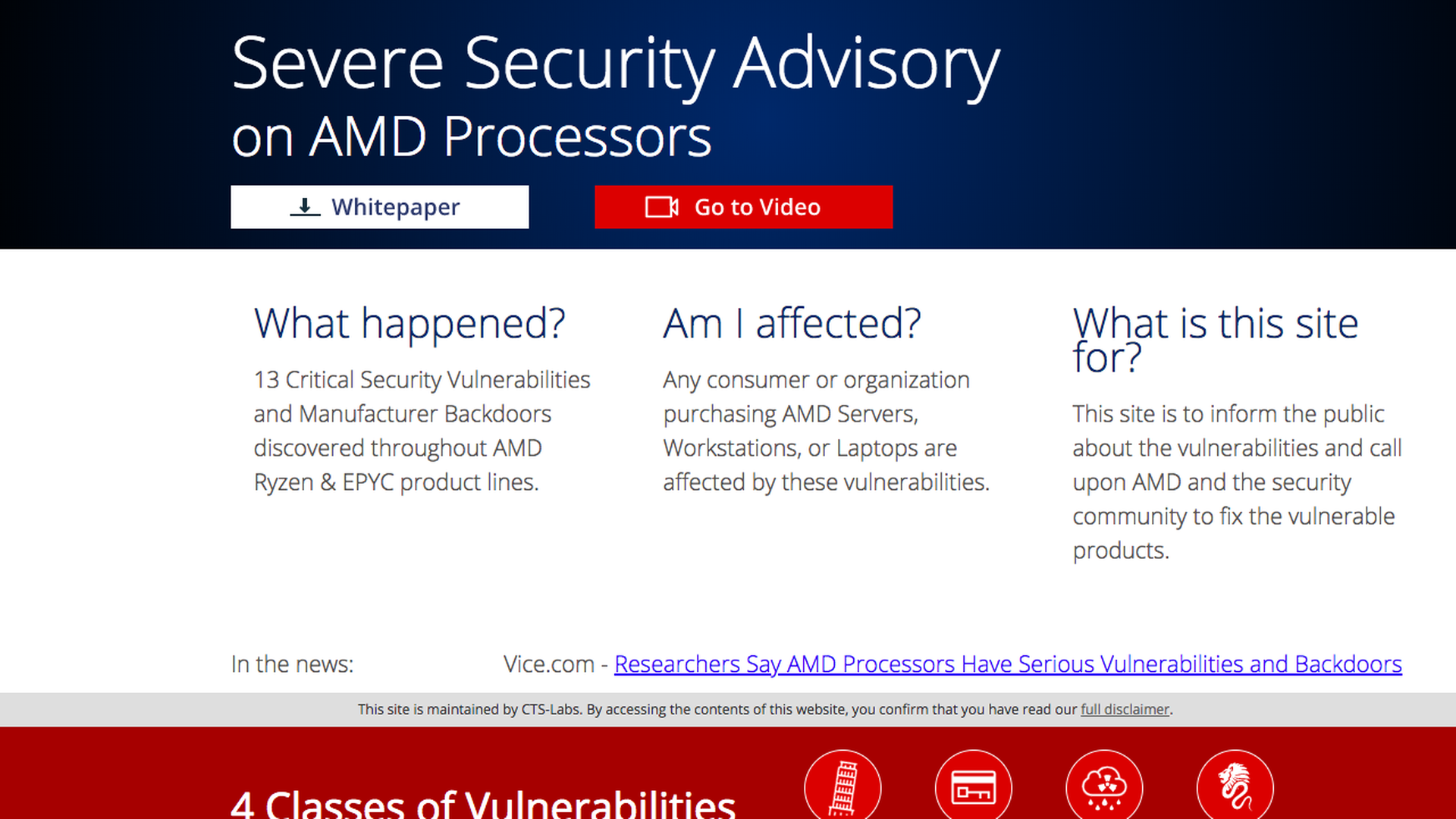
A screen capture of the AMDflaws.com website. Joe Uchill / Axios
An upstart cybersecurity research group and trading firm claimed Tuesday that security flaws in AMD computer processors "could potentially put lives at risk." But many in the security community say the widely covered report was dangerously overhyped in an attempt to drive down AMD's stock price.
Why it matters: CTS-Labs and Viceroy Research ultimately did not move the market — AMD finished up for the day. But the media bought into the chaos, at least a little, which could have disastrous effects to security-concerned owners of AMD products.
The intrigue: CTS posted a slick website devoted to the AMD flaws they discovered, complete with video interviews and charts and images ready for the media to use — a marketing effort that started at least three weeks ago when the "amdflaws.com" web domain was registered. Yet they only gave AMD 24 hours to patch the issues before going public.
- The industry standard is to give at least 90 days for a company to demonstrate it is working on a patch before going public.
What they're saying: Viceroy Research claims the vulnerabilities should be enough to bankrupt AMD. In its report, it wrote "We believe AMD is worth $0.00 and will have no choice but to file for Chapter 11 (Bankruptcy) in order to effectively deal with the repercussions of recent discoveries."
- In its own report, CTS ends with a disclaimer acknowledging it may be betting against AMD's stock price. "[W]e may have, directly or indirectly, an economic interest in the performance of the securities of the companies whose products are the subject of our reports."
What independent researchers are saying: Many researchers note that the white paper released by CTS provides no technical detail, making it impossible to evaluate the claims. But the suite of four potential attacks described by CTS are, at a minimum, already covered by one layer of computer security. All of them essentially require the computer to have already been hacked before they can be used to inflict more damage. In short, it can make bad worse, but not create the bad.
- "It feels like they may have some valid security research and they’ve come up with a case study how not to disclose it," said researcher Kevin Beaumont. "It feels like a press exploit on top of vulnerability research."
- Rapid7 Research Director Tod Beardsley emailed that one of the vulnerabilities appears to simply be that the user might intentionally install malware onto a component known as the BIOS. "In the end, an 'unauthorized BIOS update' is, itself, an attack that is usually mitigated by normal operating system, firmware, and physical controls," he wrote via email.
- Even the outside expert used by CTL-Labs — Dan Guido, CEO of Trail of Bits —
was skeptical about the marketing push behind the flaws, tweeting "Regardless of the hype around the release, the bugs are real, accurately described in their technical report (which is not public afaik), and their exploit code works."
