World's most popular hotel door lock vulnerable to hackers
Add Axios as your preferred source to
see more of our stories on Google.
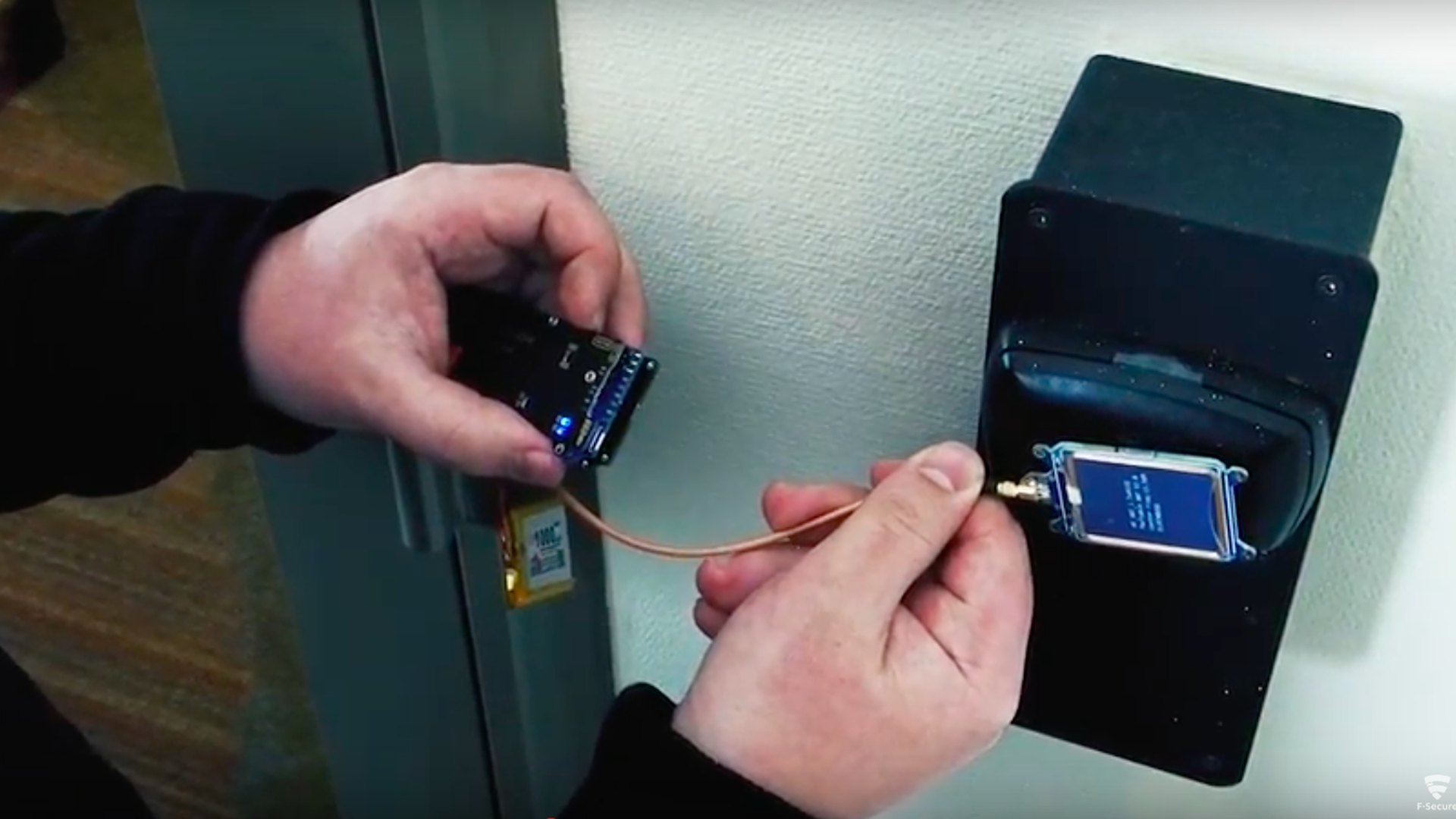
F-Secure researchers unlock a hotel door using their device in a YouTube video. Screengrab: YouTube
Tomi Tuominen and Timo Hirvonen, both researchers at cybersecurity firm F-Secure, have discovered a security flaw in the most popular manufacturer line of digital hotel locks.
Why it matters: Though they've worked with the manufacturers on a patch that has already been released, it is likely that not all the doors have been patched yet as 40 thousand hotels use the locks. The duo noted to Axios that manufacturer Assa Abloy's locks were very secure and the company was attentive to the problem. This is a prime example of a company doing everything right and still having vulnerabilities because no product is 100% secure.
F-secure researchers demonstrate their hotel door hacking device.
The details: "It started at a hacker conference in Berlin in 2003," said Tuominen. "We came back to our room and found that our friends laptop had been stolen. But the locks didn't show any signs of being broken into. The hotel didn't take us seriously because, I think, they thought we were hippies in black t-shirts."
- Thus started a near 15-year side project where the duo researched how they could hack the locks. It took until last year to have a major breakthrough to digitally break the locks, during which time they learned "it's actually much easier to break the lock with a wire hanger."
How it works: They began by taking any key from a target hotel, even an expired one. That key gives them location specific information to be used in the attack.
- The keys cards are embedded with one of an innumerable amount of potential passwords — too many to fire off possible passwords at a door until it opens. But Tuominen and Hirvonen figured out how to reduce the possible set of passwords for the master key to a set small enough for a device try all of them in just a few minutes.
- Once the device discovers the master key, it works on any door.
The remediation: Assa Abloy worked with the researchers to release a patch for the doors earlier this year. They also discovered and helped patch a glitch that gave them access to the key database with access to certain business systems on a hotel network.
- The patch requires each door to be updated individually, which could have slowed the patching process at some hotels. Tuominen and Hirvonen created an Android app that will test keys to see if doors have been patched.
- They will present their project at the Infiltrate conference this week, but are leaving out key details to ensure that attackers don't victimize hotels that haven't fixed the issue yet.
