Axios Future of Cybersecurity

September 30, 2025
Happy Tuesday! Welcome back to Future of Cybersecurity.
- 👻 It's almost October, and there's nothing spookier than the influx of Cybersecurity Awareness Month pitches I'm getting in my inbox.
- 📬 Have feedback, thoughts or scoops to share? [email protected].
Today's newsletter is 1,898 words, a 7-minute read.
1 big thing: New playbook to squash scams
A group of more than 80 leading organizations from the public, private and nonprofit sectors are calling for a whole-of-government strategy to crack down on scams, according to a new strategy proposal shared first with Axios.
The big picture: Last year, Americans lost more than $158 billion to fraud and scams, or roughly $300,476 per minute, according to the Federal Trade Commission.
- Scams are about more than just filling the bank accounts of one-off cybercriminals: They're often linked back to complex overseas operations that fund various regimes.
- Yet companies and law enforcement have often worked in silos when trying to crack down.
Threat level: Advancements in AI tools will make it easier for scammers to target even more people.
- Scammers can use audio deepfakes to trick people into thinking their loved one is really on the phone asking for money, or use ChatGPT to create fake identification documents.
Driving the news: The Aspen Institute's National Task Force on Fraud and Scam Prevention published a 116-page strategy for fighting scams and sent a letter to Congress today calling on policymakers to make the issue a top priority.
- "This is a different kind of crime, and we can't do it alone," Kate Griffin, director of inclusive financial system at the Aspen Institute Financial Security Program, told Axios.
- The task force includes nearly 80 organizations across the public and private sectors, including major technology vendors, telecommunications providers and federal law enforcement agencies.
Zoom in: Some of their recommendations include:
- Modernizing the way key law enforcement databases that track scams collect and share data.
- Enacting liability protections for companies to share information about how scams have targeted individuals, given that most cyber information-sharing laws have been applied only in the context of hackers targeting companies.
- Applying sanctions and diplomatic pressure on foreign governments and private organizations that aren't perceived to be taking scam activity seriously.
- Exploring the creation of a U.S. National Anti-Scam Center, modeled after similar organizations in the U.K., Australia and Singapore.
- Encouraging the private sector to develop new consumer-facing tools and technologies that can stop scams as they happen.
Between the lines: Kathy Stokes, director of fraud prevention programs at AARP, a member of the task force, told Axios that coordination is the only way to squash scams.
- "We coordinate much worse than the criminals do," Stokes said.
- For years, companies, law enforcement and nonprofits would overemphasize the need to educate the public about how to spot scams. But Stokes said the new strategy goes beyond that, because "we cannot educate our way out of the fraud crisis."
The intrigue: Many task force members have already started working on programs that follow the strategy's recommendations.
- AARP has a Fraud Watch Network, which offers a free helpline for people who have been targeted by scams and connects them with law enforcement as needed.
- Visa, another member, created its own internal scam detection practice this year that proactively hunts and takes down scams on its own payment networks and beyond.
What's next: Several current government officials are already part of the task force, and the Aspen Institute plans to continue to use its convening power to bring people across sectors together to keep working on these issues, Griffin said.
- "We're here to keep creating the spaces where those leaders can come together to turn that blueprint into action."
2. Shutdown fallout hits cybersecurity
Several key federal cybersecurity programs face disruption starting today — either because their funding will be cut off or because Congress has failed to reauthorize them.
Why it matters: The changes mean private companies, as well as state and local governments, will have to rethink how they work with Washington on cyber defense.
Here's what's changing:
🏛️ Information-sharing authority lapses without reauthorization.
- The Cybersecurity Information Sharing Act of 2015 expires today, and Congress has not agreed on reauthorization.
- The law provides liability protections for private companies that share threat intelligence with the government.
- Without it, companies face legal uncertainty that will "likely cause hesitation in sharing and exchanging cyber threats information, especially to government partners," Mike Flynn, vice president of government affairs at the Information Technology Industry Council, said in a statement.
🧳 Cyber staff furloughs if the government shuts down.
- The Cybersecurity and Infrastructure Security Agency (CISA) plans to furlough two-thirds of its staff if Congress doesn't pass a funding deal by the end of the day, according to guidance published over the weekend.
- That estimate is based on CISA's May workforce numbers — but the agency has since faced significant staff departures, suggesting the impact could be deeper.
❌ CISA ends long-standing state and local partnership.
- CISA said Monday it's ending its years-long cooperative agreement with the Multi-State Information Sharing and Analysis Center (MS-ISAC).
- The agreement formally ends today. CISA said it will use a new model to fill resource gaps for state and local governments, many of which depend on MS-ISAC's cyber tools.
- MS-ISAC has already shifted to a fee-based membership system in anticipation of the change, but its leaders warned Axios this month that losing federal funding would undermine the country's cyber defenses.
3. U.S. agencies patch Cisco devices amid hacking
The top U.S. cyber defense agency ordered all federal civilian agencies last week to patch vulnerable Cisco networking products that state-backed hackers are actively targeting.
Why it matters: Federal cyber investigators have already found evidence of compromised devices, and CISA is aware of hundreds of potentially vulnerable Cisco devices across the federal government, a U.S. official told reporters.
Driving the news: Cisco said Thursday that it's been working with "multiple government agencies" to investigate attacks on its firewalls that have let hackers implant malware, execute command and possibly exfiltrate data from the compromised devices.
- The company also disclosed and released patches for three zero-day vulnerabilities in its Adaptive Security Appliances — although attackers have been targeting only two of them.
Threat level: During its threat-hunting campaign, CISA uncovered evidence that some federal devices had already been compromised.
- Cisco attributed the attacks to ArcaneDoor, a hacking group that predominantly targets networking devices and has been active since 2023. Some researchers have linked the group to China-based hackers, but the U.S. has not formally attributed the attacks.
- In some cases, the hackers have "modified commands to allow for persistence across reboots and software upgrades," Chris Butera, acting deputy executive assistant director for cyber at CISA, told reporters.
State of play: A U.S. official told Cybersecurity Dive that at least 10 organizations worldwide have been breached, including multiple federal agencies.
- On Friday, the MS-ISAC said it had proactively identified more than 400 "likely vulnerable devices" across its state and local government members and had sent notifications to them. However, the MS-ISAC has not received information about any actual hacks, according to Randy Rose, vice president of security operations and intelligence at the Center for Internet Security.
- CISA spokesperson Marci McCarthy said in a statement yesterday that the "vast majority of the federal civilian executive branch agencies have submitted initial reports to CISA" about whether they are vulnerable or compromised.
Between the lines: CISA is issuing the directive in part to get a better handle on the scope of the intrusions on U.S. networks and across critical infrastructure, Butera added.
The intrigue: Cisco said it was first alerted to these attacks on government organizations in May, but the company and CISA only went public with their findings on Thursday.
📲 If you're a cyber investigator with a tip, you can reach me confidentially on Signal at SamSabin.01.
4. Whistleblowers warn of DOGE security risks
The Department of Government Efficiency has been pushing agency employees to create databases that have little to no oversight and contain sensitive personally identifiable information about every American, according to a report from Senate Democrats released last week.
Why it matters: The report confirms what many news investigations and whistleblower complaints have been warning about, and it marks the first congressional inquiry into the ways DOGE is using Americans' data.
Driving the news: Sen. Gary Peters (D-Mich.), ranking member of the Homeland Security Committee, released a report Thursday investigating how DOGE has been accessing Americans' data, based on staff visits to various agencies.
- Peters' staff also interviewed several whistleblowers who detailed how DOGE had been compiling and accessing this data — often storing it in cloud environments that lack proper security controls.
- The report also found that most agencies could not identify who was in charge at the DOGE teams that were overhauling their offices.
- The report concludes that there's a clear pattern across agencies: "Officials who questioned DOGE were pushed out, and DOGE-affiliated personnel were installed in key positions such as Chief Information Officer," the staff wrote.
Zoom in: Whistleblowers also told Peters' staff that DOGE employees at the Social Security Administration have had access to Americans' information, including their Social Security numbers, in a cloud environment "without any verified security controls and without standard agency visibility into their use of that data," according to the report.
- "If penetrated, this data vulnerability could result in the most significant data breach of Americans' sensitive data in history," the report added.
Flashback: Almost immediately after President Trump unveiled DOGE, Elon Musk hired dozens of people — many of whom lacked experience with sensitive government records — to slash staff and build new tech tools that ingest agency data.
What's next: Peters' office is calling for the SSA to shut down its new cloud environment that has sensitive information and for all DOGE work at the SSA and White House offices to cease until agencies can determine the chain of command.
5. Catch up quick
@ D.C.
👀 President Trump urged Microsoft to fire Lisa Monaco, deputy attorney general in the Biden administration, and said the government has revoked her security clearances. (Axios)
🧬 Customs and Border Protection has been harvesting DNA from American citizens, including minors, and putting the samples in an FBI crime database, according to recently released government data. (Wired)
🤖 The Trump administration approved the use of Elon Musk's Grok across the federal government. (Axios)
@ Industry
🦾 Anthropic says its latest model is enhanced to find and patch vulnerabilities in codebases. (Anthropic)
💰 The U.K. government underwrote a 1.5 billion pound ($2.01 billion) loan to Jaguar Land Rover to help bring the automaker's manufacturing operations back online after a crippling cyberattack. (Wall Street Journal)
🇵🇸 Microsoft says it has terminated the Israeli military's access to its Azure cloud platform after the company found the military had been using it to store information from millions of Palestinian civilian phone calls. (The Guardian)
@ Hackers and hacks
🇨🇳 Suspected Chinese hackers have infiltrated law firms and software developers as part of a sophisticated espionage campaign targeting trade secrets, according to Mandiant. (CNN)
🚔 Authorities arrested someone in connection with a cyberattack that caused disruptions at several European airports last week. (BBC)
🏫 Hackers claim they stole pictures of more than 8,000 children from the Kido nursery chain, which operates across the U.S., the U.K., India and China. (The Guardian)
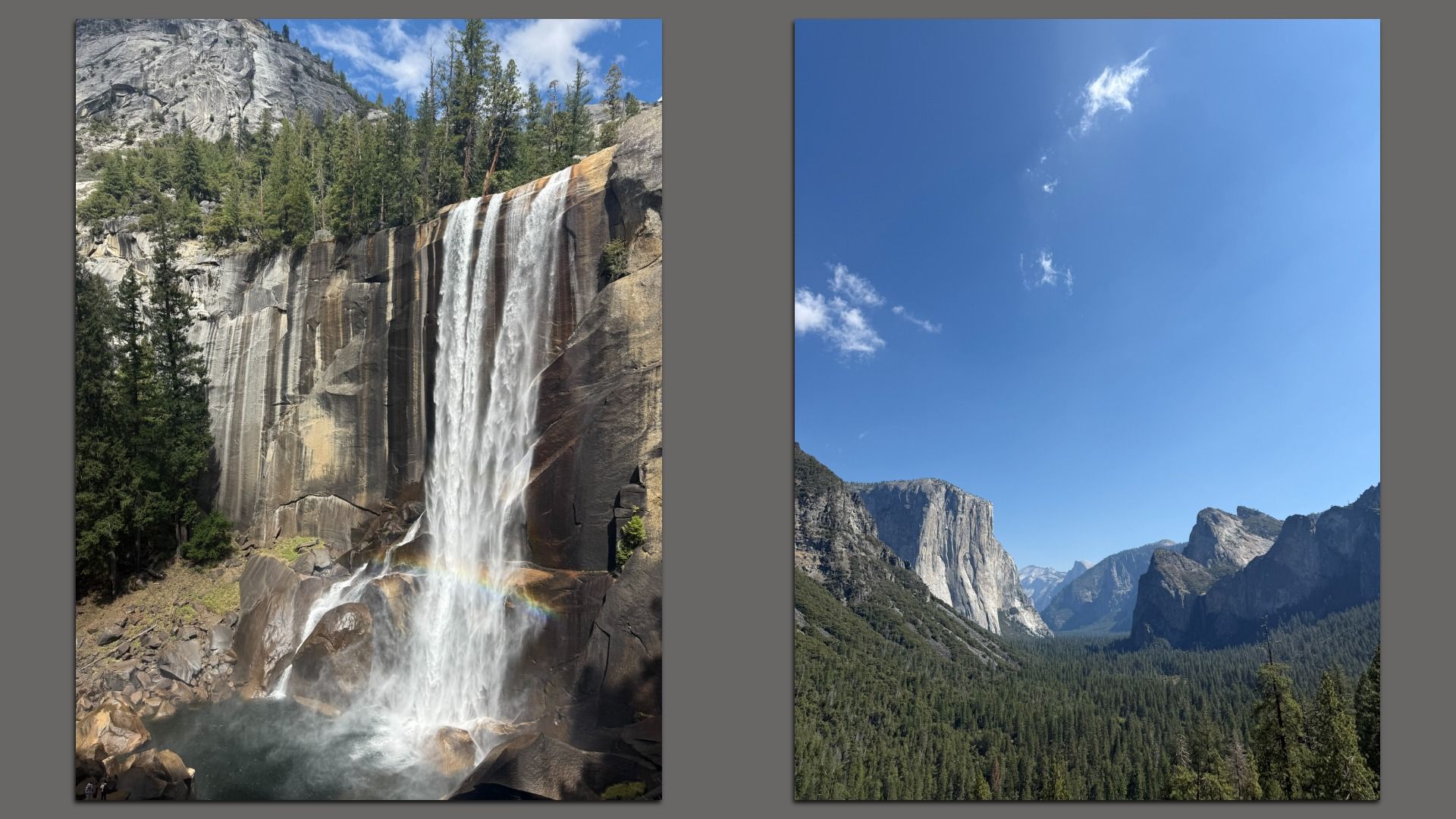
6. 1 fun thing
🏕️ I crossed another national park off my list this month.
- ✅ In case you were wondering: I highly recommend a visit to Yosemite.
☀️ See y'all next week!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity