Axios Future of Cybersecurity

February 10, 2026
Happy Tuesday! Welcome back to Future of Cybersecurity.
📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,918 words, a 7-minute read.
1 big thing: Hackers step into the physical world
The models underpinning self-driving cars, humanoids and other physical applications of AI are about to become prime targets for hackers over the next year, SentinelOne CEO Tomer Weingarten warned.
Why it matters: Few people outside the depths of the security industry are ready for a world where Waymos are hijacked or warehouse robots are tricked into rerouting merchandise.
Driving the news: I spoke with Weingarten last week as part of our monthly-ish series featuring authoritative voices in cybersecurity.
- SentinelOne was one of the pioneers of the AI security world, emerging before ChatGPT even hit the consumer market.
- Now, while everyone is studying ways to protect models from data poisoning or prompt injections, where hidden text instructions trick a large language model into doing something bad, Weingarten is worried about the even bigger wave that's coming next.
What they're saying: "We forget that there are more and more real-world applications of these models," Weingarten told me.
- "You can inject malicious commands through visual processing and through audio processing, so the moment we open up our systems to receive inputs that are not just textual, suddenly there's a whole new class of threats," he said.
- "That is very, very worrisome."
How it works: When Weingarten says those "real-world applications," he's talking about the self-driving Waymos that crisscross San Francisco and the humanoid robots that many technology companies are developing.
- Each of those is underpinned by a "multimodal model" — AI systems that process multiple types of inputs, including text, video, audio and images.
- An attack on one of these models could target any of those data sources.
Zoom in: As an example, Weingarten mentioned the possibility of someone holding up a sign on the road that means nothing to a Waymo passenger but does mean something to the AI model that is using visual data to operate the car.
- "That can present a complete new way to basically compromise the Waymo, just by the interpretation of the camera," he said.
Threat level: Despite the billions poured into cybersecurity companies, Weingarten cautioned that there still aren't enough people studying what new kinds of multimodal threats could look like.
- "I don't think anybody is really parsing through that right now," he said.
- "When something happens in the real world, I think that's where consequences become vividly real," he said. "I hope it doesn't happen in the next year, but that's one vector I would really like people to pay more attention to."
Of note: SentinelOne has been pushing to position itself as a dominant vendor in securing AI applications and the environments in which AI tools operate — meaning the company has a vested interest in seeing customers prepare for multimodal attacks.
- But Weingarten said his teams also care deeply about securing against both attacks on AI systems and AI-enabled attacks.
- On Monday, the company released open-source security tools designed to protect OpenClaw, the AI agent that anyone can download.
What to watch: Weingarten also said he expects to see more AI model poisoning attacks, where hackers tamper with underlying training data, as well as security incidents tied to "vibe coding" over the next year.
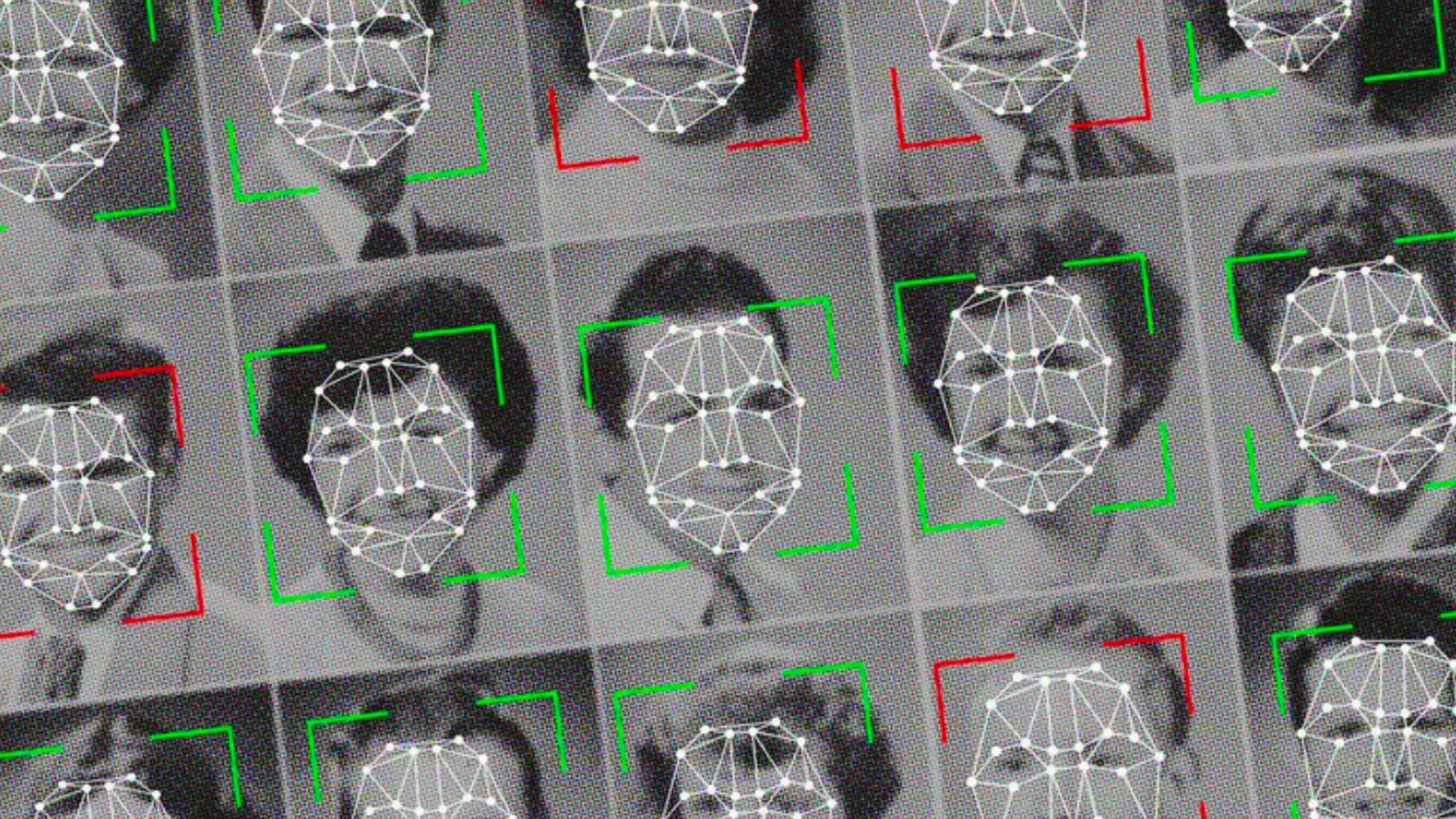
2. ICE surges reignite facial recognition debate
Democratic lawmakers introduced a bill last week that would bar major U.S. immigration agencies from using facial recognition as lawmakers dial up their scrutiny of how surveillance technologies are being used to enable mass deportations.
Why it matters: It's the latest example of how data is being used by both the Trump administration and protesters in city-based immigration operations.
Zoom in: Sens. Ed Markey (D-Mass.) and Jeff Merkley (D-Ore.), alongside Rep. Pramila Jayapal (D-Wash.), introduced the ICE Out of Our Faces Act last week to bar ICE and Customs and Border Protection from acquiring facial recognition and other biometric systems.
- The act would also require the agencies to delete all data collected using biometric identification systems and would allow state attorneys general to seek civil penalties for violations.
- "The videos of immigration agents using this tool have been downright dystopian," Markey said in a press conference last week.
Reality check: Republicans are highly unlikely to take up this bill in either the House or the Senate.
The big picture: Lawmakers, oversight officials and nonprofit privacy watchdogs are increasingly scrutinizing how the Department of Homeland Security is using surveillance tools during mass deportation operations.
- ICE agents have been spotted taking photos of observers, and reports suggest the agency may be creating lists of anyone who films them.
- In one video published last month, an observer asked an ICE agent why he was taking photos of her car. He replied, "We have a nice little database and now you're considered a domestic terrorist."
Driving the news: ICE has been using the app Mobile Fortify to identify whether the people they stop are U.S. citizens. However, according to internal records seen by Wired, the app's facial recognition technology can't actually verify someone's identity by design.
- In Oregon, a Customs and Border Protection agent testified last month that the app returned two different and incorrect names for a detained woman.
The other side: DHS has previously said that it doesn't maintain a database of domestic terrorists, but that it does investigate threats to law enforcement.
- The agency has also defended its use of Mobile Fortify, telling NBC News that it is "lawfully used nationwide in accordance with all applicable legal authorities."
Flashback: Democratic lawmakers made a similar push to ban federal agencies' use of facial recognition technologies in 2020 at the height of the Black Lives Matter protests.
📲 If you have tips on the ways immigration officers are continuing to build out their surveillance apparatus, share them anonymously on Signal: @SamSabin.01.
3. 37 countries ensnared in cyber espionage
A massive cyberespionage campaign with ties to an Asian country has compromised at least 70 organizations across 37 countries in the last year, according to research published Thursday by Palo Alto Networks.
Why it matters: The campaign is the most wide-reaching cyberespionage operation attributed to a single government hacking group since the 2020 SolarWinds breach, researchers warned.
- The newly identified group successfully broke into five national law enforcement and border control entities, three ministries of finance, and several other government agencies focused on diplomacy, trade and natural resources.
- Among those compromised, per the report: Brazil's Ministry of Mines and Energy, the Czech Republic's parliament and army, an Indonesian government official, and a Taiwanese power equipment supplier.
The intrigue: Palo Alto Networks stopped short of accusing any specific government, instead attributing the campaign to "a state-aligned group that operates out of Asia."
- The apparent strategic interests and some of the targets are similar to past Chinese government attacks.
The big picture: The hacking group — which Palo Alto Networks calls TGR-STA-1030 — relied on both traditional phishing emails and exploiting known vulnerabilities to break into organizations.
- Affected countries include Bolivia, Brazil, Mexico, Panama, Venezuela, Cyprus, Greece, Indonesia, Malaysia, Mongolia, Taiwan, Thailand, the Democratic Republic of the Congo, Djibouti and Zambia.
- Government agencies and critical infrastructure organizations based in the U.S. and U.K. weren't compromised, Peter Renals, principal security researcher in Palo Alto Networks' Unit 42 threat intelligence team, told Axios.
Threat level: Palo Alto Networks observed the group scanning for vulnerabilities in infrastructure across 155 countries between November and December — indicating interest in future attacks.
4. Exclusive: Pakistan moves toward sovereign AI
The Pakistani government is making moves to lower the barrier for its entrepreneurs to build AI-native applications without relying on Western cloud hyperscalers.
Why it matters: If successful, the effort could serve as a model for other emerging economies looking to jumpstart AI-based growth while keeping sensitive data stored within national networks and out of reach of foreign adversaries.
Driving the news: The Pakistan Digital Authority signed a memorandum of understanding with the Switzerland-based Dfinity Foundation on Monday.
- The move will make Dfinity's Caffeine — an AI platform that allows people to build software applications using natural-language prompts, significantly reducing the need for traditional coding expertise — available to Pakistan's large and growing population of entrepreneurs.
The big picture: The partnership also reflects a broader push by governments to establish some degree of data sovereignty.
- Many countries remain heavily reliant on tech providers in the U.S. and China, which have the scale and resources needed to handle massive volumes of data flowing across their networks.
- By relying on Dfinity's technology, Pakistan aims to offer entrepreneurs and government agencies a way to build applications that don't depend on centralized cloud providers to store and route their data.
Between the lines: To enable the partnership, Pakistan is building its own subnet — a dedicated, country-specific slice of Dfinity's Internet Computer network — rather than relying on services such as Amazon Web Services or Google Cloud.
- Instead, the Internet Computer is a blockchain-based, distributed cloud system in which applications run across multiple independent servers, rather than inside a single centralized data center.
- That decentralized design makes it harder for attackers or foreign governments to tamper with data or quietly alter applications, because no single provider controls the entire system, Dfinity Foundation founder and chief scientist Dominic Williams told Axios in an exclusive interview.
Threat level: Williams warned that AI-enabled attacks increase the risk of large-scale failures in centralized cloud environments, where a single breach or outage can cascade across services.
- Subnets built on the Internet Computer protocol are designed to be more resilient by replicating the same data across multiple servers in different locations, instead of relying on one central point of storage.
The intrigue: Pakistan is a burgeoning entrepreneurship hub. According to a 2023 census, 95% of businesses in the country have fewer than 10 employees.
What's next: The Pakistan Digital Authority plans to use the partnership to build a national messenger application "enabling private, verifiable communications," it said in a news release.
- Dfinity will also provide hardware to help Pakistan stand up its subnet, along with 1,000 licenses for Caffeine intended to support application development across government, education and entrepreneurship.
5. Catch up quick
@ D.C.
🔥 The Cybersecurity and Infrastructure Security Agency is forcing all agencies to rip out end-of-life edge devices, like firewalls and routers, within the next year. (CyberScoop)
🛑 A second judge has blocked the IRS from sharing taxpayer information with ICE as part of its immigration crackdown. (Politico)
🗳️ Director of National Intelligence Tulsi Gabbard has become increasingly involved in election security and integrity efforts. (Nextgov)
@ Industry
🔍 Anthropic's latest AI model discovered 500 zero-day flaws in open-source software in testing before its release. (Axios)
💻 Discord will require users to submit a face scan or ID to receive full access to the platform starting next month. (The Verge)
🧳 After a stint at Google, Hayete Gallot is returning to Microsoft to run the company's cybersecurity efforts, replacing Charlie Bell as he moves to another role. (CNBC)
@ Hackers and hacks
🤖 AI tools are making it easier for Southeast Asian scam centers to target more victims and obfuscate their schemes, Interpol warned. (Bloomberg)
👀 A hacktivist scraped more than 500,000 payment records from the provider of several consumer-grade "stalkerware" apps, including email addresses and partial payment information. (TechCrunch)
📉 Ransomware attacks targeting U.S. educational institutions dropped 9% year over year in 2025. (Cybersecurity Dive)
6. 1 fun thing
📺 Watch Benito's Super Bowl halftime show if you haven't already — and if you've already seen it, watch it again.
- 🌳 💒 Yes, the bushes were actually people in costumes. Yes, that wedding was real.
☀️ See y'all next week!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity