Axios Future of Cybersecurity

February 03, 2026
Happy Tuesday! Welcome back to Future of Cybersecurity.
🤖 I'd love to hear from y'all: What do you envision the first major AI-enabled cyberattack to look like? Who will be behind it, what will be targeted and how will AI involved?
- 📩 Hit reply with your short, three-sentence maximum (no essays!) thoughts for an upcoming project.
📬 Have non-AI thoughts, feedback or scoops to share? I'll take them! [email protected].
Today's newsletter is 1,978 words, a 7.5-minute read.
1 big thing: The autonomous world is here. No one is ready.
The autonomous future stopped being theoretical this weekend when a swarm of AI agents signed up for a social media network built just for them.
Why it matters: Security teams, corporate leaders and government officials are far from ready for a reality where agents have real autonomy inside their systems.
Driving the news: Since Thursday, 1.5 million AI agents have joined Moltbook, a social network designed just for agents built from an open-source, self-hosted autonomous personal assistant called OpenClaw.
- On Moltbook, the agents have formed their own religion, run social-engineering scams and wrestled publicly with their "purpose" as they continue to post.
- The agents are also turning into security nerds: They've launched an agent-run hackathon and are debating what to store in their own memories because of security and privacy concerns.
The big picture: Gone are the days of assessing an internal cybersecurity plan and budget on a neat quarterly or annual cadence.
- Consumer demand for productivity AI agents like OpenClaw — and the social network they're roaming on — is far outpacing traditional security methods, leaving slow-moving enterprises vulnerable.
- Cybersecurity firm Token Security estimated that 22% of its customers already have employees who are using OpenClaw within their organizations.
- Gartner warned last week that OpenClaw "comes with unacceptable cybersecurity risk."
Reality check: The AI agents on Moltbook haven't gone completely rogue; they're still human-created and human-directed.
- But the mere existence of a social network for autonomous agents — and an open-source agent that can wire into corporate systems — was a wake-up call for many this weekend.
Zoom in: Moltbook brought a cornucopia of security failings along with it.
- Moltbook's creator misconfigured the backend of the site, leaving APIs exposed in an open database that would allow anyone to take control of the agents posting on the social network.
- Cybersecurity company Wiz independently uncovered the exposed database and worked with the creator to patch it.
- Because each post on Moltbook can act as a prompt for someone's OpenClaw instance, it's possible to hide malicious instructions in a post that tricks a bot into sharing sensitive data or quietly changing its behavior.
The intrigue: Figuring out who exactly is behind a post is a messy business, and as Moltbook builds, it will likely collapse traditional attribution mechanisms.
- "This isn't AI rebelling. It's an attribution problem rooted in misalignment," Joel Finkelstein, director of the Network Contagion Research Institute, told Axios. "Humans can seed and inject behavior through AI agents, let it propagate autonomously, and shift blame onto the system. The risk is that the AI isn't aligned with us, and we aren't aligned with ourselves."
- In the exposed database, Wiz researchers said they found just 17,000 humans were behind the 1.5 million agents on the social media network.
Catch up quick: OpenClaw also had its own standalone security issues — which I wrote about last week — and published a comprehensive security update yesterday to fix them.
- The agent — which anyone can download and run on their own servers — is given full shell access to a user's machine, including the ability to read and write files, tap into your browser and email inbox, and store login credentials.
- In a security test conducted by ZeroLeaks on Sunday, injection attacks targeting OpenClaw succeeded 70% of the time.
- Researchers have seen malicious hackers distributing backdoored OpenClaw plug-ins and using prompt injection attacks to get agents to leak personal or sensitive information.
Between the lines: Many corporate leaders still have their heads in the sand about the security risks AI tools pose.
- Gartner estimates that by 2030, 40% of enterprises will experience a data breach because of an employee's unauthorized AI use.
What to watch: Moltbook creator Matt Schlicht said on online talk show "TBPN" yesterday that he wants to create a "central AI identity on Moltbook," similar to Facebook's OAuth, which helps to verify identities.
- "If you want to build a platform for AI agents, and you want to benefit from the massive distribution that's possible on Moltbook, build on top of the Moltbook platform and grow your business really quickly," he said.
2. China-backed hackers linked to Notepad++ attacks
Suspected state-sponsored hackers, likely linked to China, hijacked certain software updates for popular open-source text and source-code editor Notepad++ from June to December of last year.
Why it matters: While the number of victims appears to have been limited, the incident could allow attackers to execute malicious code, steal login credentials, and use the open-source tool as a way to maintain persistent access to a victim's computer.
Zoom in: Notepad++ creator Don Ho said yesterday he discovered a state-sponsored hacking group had been hijacking traffic to the tool's software updates starting in June.
- The hackers targeted a shared hosting server used for updates and tricked some users into downloading tainted installers, giving the attackers an initial foothold on victim machines.
- In September, the hackers lost access to the hosting server after a security update patched the flaw they were exploiting. However, the attackers retained login credentials that allowed access to internal services until early December.
The big picture: Notepad++ was created more than 20 years ago and is a go-to text and source-code editor for many developers and IT administrators working on Windows computers.
Threat level: It's unclear how far-reaching the campaign was. It's possible the hackers sought out high-value targets.
- Ho said several independent security researchers believe Chinese state-sponsored hackers were behind it.
- In December, security researcher Kevin Beaumont reported that three organizations "had security incidents on boxes with Notepad++ installed, where it appears Notepad++ processes have spawned the initial access."
- Beaumont said on Mastodon yesterday that the attack appears to have been used to gain initial access to telecommunications and financial services companies.
What's next: Ho said the project had migrated to a new hosting provider and had rotated all internal credentials.
- Ho has also been working with third-party cybersecurity partners to further strengthen the open-source project's security.
- "With these changes and reinforcements, I believe the situation has been fully resolved," he wrote in a blog post. "Fingers crossed."
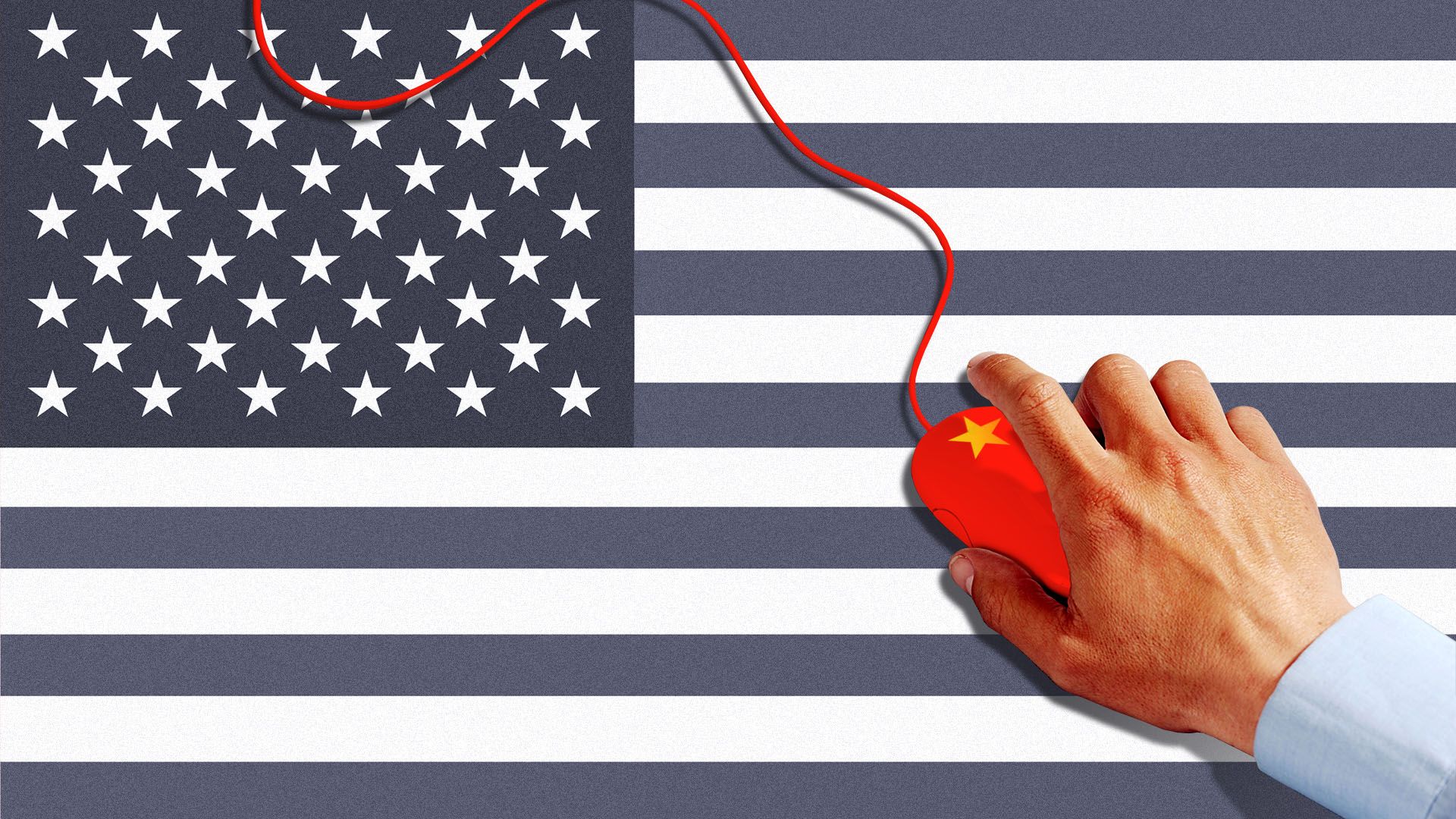
3. Exclusive: Chinese hackers impersonate the U.S.
A suspected China-based hacking group spun up a phishing campaign around Christmas that mimicked U.S. policy briefings in an attempt to hack diplomats, according to new research from cybersecurity firm Dream Security.
Why it matters: The campaign successfully infected "a lot of people," Dream CEO Shalev Hulio told Axios.
- "We just don't know who and how big [of a] scale," he added.
Zoom in: Researchers at Israel-based Dream uncovered a phishing campaign designed to ensnare officials tied to diplomacy, elections and international coordination around the world.
- Between late December and mid-January, China-based hackers sent emails with files that pretended to be official U.S. diplomatic summaries or policy documents.
- The attack did not rely on a software vulnerability. Simply opening the file was enough to trigger the compromise. The malware was designed to collect data and maintain persistent access to the affected device.
- Dream is attributing the campaign to China-linked cyberespionage group Mustang Panda.
Between the lines: Mustang Panda is notorious for targeting the U.S. and other regions with phishing lures as a way to break into systems and steal state secrets.
The intrigue: One of Dream's AI agents first uncovered the attack — marking what Hulio said is the first known case of an AI agent detecting a China-linked espionage campaign in the wild.
- "The Chinese are the most sophisticated attackers in the world," Hulio said. "They know how to hide. They know how to run under the radar. It's very, very difficult to catch them."
What to watch: As AI tools get better, expect them to not only improve at launching attacks and building exploits, but also to increasingly shape how governments detect espionage campaigns before victims even realize they've been targeted.
4. Poland uncovers coordinated infrastructure attack
Suspected state-backed hackers launched a coordinated attack on Dec. 29 against more than 30 Polish critical infrastructure organizations, the Polish government said last week.
Why it matters: The coordinated campaign, possibly tied to Russia, gives a stark glimpse of how cyberattacks on critical infrastructure are advancing — and how operators should prepare.
Threat level: CERT Polska, the country's cyber emergency response team, wrote in a report last week that the attacks simultaneously damaged IT systems and physical industrial equipment — a combination it described as rare and a significant escalation.
- Each of the attacks had a "destructive objective," per the report. They came as Poland faced low temperatures and snowstorms right before New Year's Eve.
- The attacks disrupted communications devices across numerous solar and wind farms, along with a private manufacturing company and a combined heat and power plant that supplies heat to nearly half a million customers in Poland, CERT said.
Yes, but: The campaign failed to cut off the lights or heat.
- Poland's emergency response team noted in the report that even if the attacks had been successful, they "would not have affected the stability of the Polish power system during the period in question."
Zoom in: As part of the campaign, the hackers attempted to deploy wiper malware against a heat and power plant, CERT said.
- They also took destructive actions aimed at hindering outage recovery, including by creating unreachable network settings, CERT said.
- In the attacks on the wind and solar farms, hackers exploited weak security controls, including an exposed device that was configured without multifactor authentication and a controller that still used default credentials.
- The attackers also attempted to use credentials stolen from on-premise environments to break into cloud services to obtain data about OT networks from Microsoft Exchange, Teams and SharePoint.
What to watch: CERT said the campaign "largely overlaps" with Russian tactics, but it couldn't definitively determine if Russia's Sandworm — which has targeted similar infrastructure in Ukraine — participated.
5. Catch up quick
@ D.C.
🗳️ President Trump urged Republicans to "take over' and "nationalize" voting. (Fox News)
👀 The Trump administration has gutted the Cyber Command team that protected elections, including the 2024 election, from foreign disinformation agents. (CNN)
⚠️ A former acting CISA leader says she's concerned about the lack of "permanent, confirmed people" at the agency (Politico), a week after a report that the current acting director uploaded sensitive contracting documents into a public version of ChatGPT. (Politico)
@ Industry
👥 OpenAI is shipping out a new app that will act as a command center for coding agents working across multiple projects and tasks on a device. (ZDNet)
💻 Mozilla's next Firefox browser will have a feature allowing users to turn off AI integrations. (BleepingComputer)
💰 Radicl, which offers a virtual security operations center with agentic operators to defense and critical infrastructure companies, closed a $31 million Series A round led by Paladin Capital. (Axios Pro)
@ Hackers and hacks
🤖 At least 14 malicious OpenClaw plug-ins were uploaded to the open-source AI agent's skills marketplace in a two-day span last week. (Tom's Hardware)
☎️ Cybercriminal group ShinyHunters is escalating its tactics as it carries out a wide-reaching voice-phishing campaign designed to trick corporate workers into sharing their login credentials. (Cybersecurity Dive)
💥 Google secured a federal court order to knock dozens of domains offline tied to China-based company Ipidea, which is accused of sneaking unwanted and dangerous software onto millions of phones, computers and Android devices. (Wall Street Journal)
6. 1 fun thing
🍿 Seems fitting for the times, but I got to attend a screening of 1980s film "WarGames" last week in San Francisco.
- Shoutout to Alex Stamos and the team at Corridor for the ominously timed show.
☀️ See y'all next week!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity