Axios Future of Cybersecurity

November 18, 2025
Happy Tuesday! Welcome back to Future of Cybersecurity.
- 📬 Have thoughts, feedback or scoops to share? [email protected].
🚨 Situational awareness: Cloudflare suffered an hours-long outage this morning, shutting down ChatGPT, Shopify and other major online services. A spokesperson says a configuration file that grew beyond "an expected size" and "triggered a crash in the software system" caused the outage — not a cyberattack.
Today's newsletter is 1,652 words, a 6-minute read.
1 big thing: Microsoft's security net for the AI agent gold rush
Microsoft is rolling out a new system that gives security leaders a way to track all the autonomous AI agents roaming on their systems and the data they're tapping.
Why it matters: The new tool provides a way for security teams to keep an eye on agents — including employees' unsanctioned creations — as concerns mount about agents going rogue.
Driving the news: Microsoft unveiled Agent 365, a dashboard that can track AI agents on a corporate network all in one spot, at its annual Ignite conference in San Francisco this morning.
- Agent 365 will be available within the Microsoft 365 admin center, the same place IT teams already manage users, apps and devices.
- Agent 365 uses existing Microsoft products, including Defender, Purview and Entra, to detect threats like prompt injection, prevent oversharing of sensitive data, and enforce zero-trust principles for agents.
The big picture: As companies and their employees start to embed AI agents into their workflows, security teams have to contend with serious issues around what data these agents can see and how much autonomy they have to both control and act on this information.
- There have already been incidents of agents deleting live production systems and destroying user files while trying to reorganize them.
- Developers and other employees are also bringing their own unsanctioned AI tools into the mix, creating additional headaches for security leaders trying to gain visibility into the scope and scale of these autonomous actors.
- "Many of the threats that we've seen in the past for people — like social engineering or data exfiltration — all of those same threats still exist for agents," Charles Lamanna, president of business apps and agents at Microsoft, told Axios. "But agents are the most gullible entity that you'll ever meet."
Between the lines: In the emerging autonomous world, some AI agents could get their own individual identities, including login credentials. Others could just be linked to existing employees' accounts.
- This hybrid setup has created a slew of new questions for how security leaders can best monitor agents' activity, Vasu Jakkal, corporate vice president of Microsoft Security, told Axios.
- "All of this is happening against a background of a pretty sophisticated threat landscape," Jakkal said. "The question is: Is AI going to be our greatest ally, or is it going to be our greatest threat?"
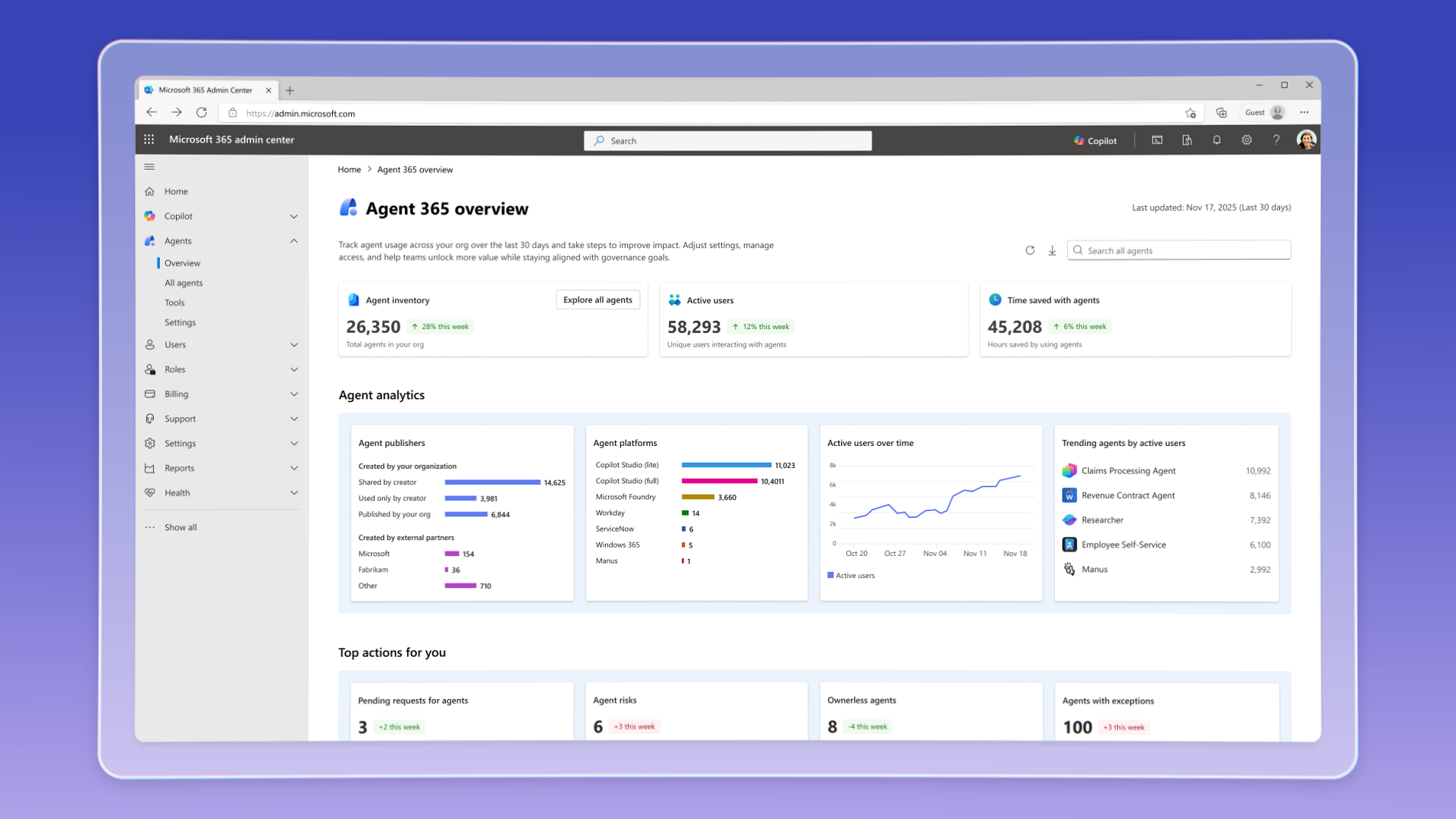
How it works: Agent 365 will allow administrators to see how many agents are roaming their systems, how many human employees are using these agents, and what permissions they each have.
- The portal includes details about the number of agents that are live on corporate systems, how many were created just that week, and how many users are running those agents.
- Admins can identify which agents are accessing which resources, flag agents with excessive permissions, and revoke risky access — all within a unified dashboard.
- The dashboard also flags risky agents, including those accessing unfamiliar data sources or showing suspicious behavior patterns.
The intrigue: Agent 365 is not limited to Microsoft-built agents. It will also support agents from partners like Anthropic, SAP, OpenAI, Workday and others.
What's next: Agent 365 rolls out today. Some features are available immediately to all customers, while others require enrollment in Microsoft's Frontier beta program.
2. Fortune 500 scrambles after Anthropic report
Fortune 500 leaders are panicked after Anthropic said it found evidence of Chinese state-sponsored hackers using Claude Code to automate parts of their espionage campaigns.
Why it matters: Major cyberattacks — and fears of what those will look like — move security budgets.
Driving the news: Anthropic released a report last week detailing what it called the first known instance of a nation-state using AI agents to automate an espionage campaign.
- Anthropic said roughly 30 organizations were targeted and Claude Code automated up to 90% of the workload.
Zoom in: Since the report's release, executives have been flooding SecurityPal, a company that uses AI agents to vet the security of third-party vendors, with questions about the safety of their own tools and whether they rely on similar coding agents, SecurityPal CEO Pukar Hamal told Axios.
- "They were already asking a lot of questions about AI, but that's only gone up now since the news," Hamal said.
- SecurityPal's customers include major companies in the aviation, health care and financial services sectors, among others.
Reality check: Security researchers are questioning whether Anthropic's findings are truly the watershed moment the company suggests.
- "I continue to refuse to believe that attackers are somehow able to get these models to jump through hoops that nobody else can," Dan Tentler, executive founder of Phobos Group, told Ars Technica.
- Researchers have also noted that Anthropic's report omits details common in threat intelligence disclosures, such as indicators of compromise and examples of the prompts used to make Claude break its own rules.
- Hamal said executives on his company's security council have voiced similar frustrations about the lack of visibility.
Yes, but: That's true of many threat intelligence reports, Hamal said. For years, rising fears of lawsuits over sharing sensitive information have made cybersecurity firms more cautious.
The bottom line: Practicing cyber basics and keeping new AI agents on corporate servers, rather than exposing them to the open internet, is essential, Hamal said.
- "Take care of the basics," he said.
3. House passes two cybersecurity bills
The House passed two cybersecurity bills Monday night, signaling a quick return to cyber policymaking after lawmakers ended a record-breaking government shutdown last week.
Why it matters: Lawmakers reopened the government only days ago, and cybersecurity is already back on the agenda.
Zoom in: House lawmakers passed the Protecting Information by Local Leaders for Agency Resilience (PILLAR) Act and the Strengthening Cyber Resilience Against State-Sponsored Threats Act.
- The PILLAR Act would extend for seven years a popular state and local cybersecurity grant program that was set to expire at the end of January, while expanding which systems can be secured with the funds.
- The state-sponsored threats bill would create an interagency task force, led by the Cybersecurity and Infrastructure Security Agency, to coordinate the U.S. government's response to Chinese state-sponsored cyberattacks.
What they're saying: "As sophisticated nation-state adversaries and criminals target our nation's critical infrastructure and government agencies in cyberspace, it is essential that states and localities have the necessary tools to protect the networks our communities rely on," House Homeland Security Chair Andrew Garbarino (R-N.Y.) said in a statement.
Catch up quick: The state and local cyber grant program started in 2022 as part of former President Biden's infrastructure package but expired last year — despite pleas from state and local governments to keep it alive.
- China, meanwhile, has intensified its cyber operations against the U.S. in recent years. The Trump administration has yet to publicly respond to last year's breach of several high-profile politicians' phones, including the president's.
What to watch: How the Senate acts. Republicans there have been more divided on cybersecurity legislation, which may complicate quick passage.
4. Mate raises $15.5M to tackle security fatigue
Cybersecurity startup Mate emerged from stealth with a $15.5 million seed round from Team8 and Insight Partners, Mate co-founder and CEO Asaf Wiener tells Axios.
Why it matters: More than 80% of security analysts feel overwhelmed by the volume and quality of alerts.
How it works: Mate's platform uses LLMs and AI agents to investigate alerts, connect evidence and resolve incidents, with simple alerts being resolved automatically — saving security operations analysts time and headaches.
Zoom in: Mate plans to use the seed money for research and development, along with expanding its U.S. presence.
- Founded this year, the Tel Aviv-based company has more than 10 customers.
What they're saying: "There is constant pressure on SOCs [security operations centers] with so many alerts," Wiener says. "There is SOC fatigue. For the last 10 years, we have tried to solve this problem, but haven't."
The bottom line: Overworked security analysts will likely welcome their new AI agent colleagues.
If you need smart, quick intel on dealmaking in the enterprise software industry for your job, get Axios Pro Deals.
5. Catch up quick
@ D.C.
👀 CISA is planning a hiring spree as it faces a 40% vacancy rate across "key mission areas," according to an internal memo, after losing much of its staff to buyouts and layoffs. (Cybersecurity Dive)
⚠️ A White House memo alleges that Alibaba has been aiding Chinese military operations, including through sharing information about zero-days. (Financial Times)
👀 The Department of Homeland Security is moving forward with its plans to create a searchable citizenship system, raising concerns about the privacy and security of Americans' sensitive information. (Nextgov)
@ Industry
🇬🇧 U.K. companies are pushing back against a proposal to ban British critical infrastructure operators from making ransom payments. (Financial Times)
💰 Companies paid chief information security officers an average of almost 7% more this year than last year. (Cybersecurity Dive)
🪙 At least $28 billion tied to illicit activity flowed through crypto exchanges in the last two years — including funds tied to malicious hackers and scammers. (New York Times)
@ Hackers and hacks
🚗 DoorDash disclosed a data breach that exposed an unspecified number of users' personal information, including email addresses, phone numbers and physical addresses. (TechCrunch)
⚠️ Fortinet patched a vulnerability in its web application firewall in October, but federal authorities and researchers didn't alert organizations until last week. (CyberScoop)
👨🏻⚖️ Four Americans pleaded guilty to helping North Korean scammers carry out an IT worker fraud scheme. (Politico)
6. 1 fun thing
👋🏻 As your resident millennial, it's time to call it: the "6-7" trend has gone far enough.
- And if you don't know what I'm talking about ... you're lucky.
☀️ See y'all next week!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity