Axios Future of Cybersecurity

December 09, 2025
Happy Tuesday! Welcome back to Future of Cybersecurity.
✈️ I'm recovering from jet lag after an evening flight out to the East Coast.
- 📬 Want to make my day? Send some scoops! [email protected].
🗓️ Join me tonight in D.C. for conversations with Georgia Attorney General Christopher Carr and Visa's chief risk and client services officer, Paul Fabara, about all things retail fraud and scams. RSVP here.
Today's newsletter is 1,422 words, 5.5-minute read.
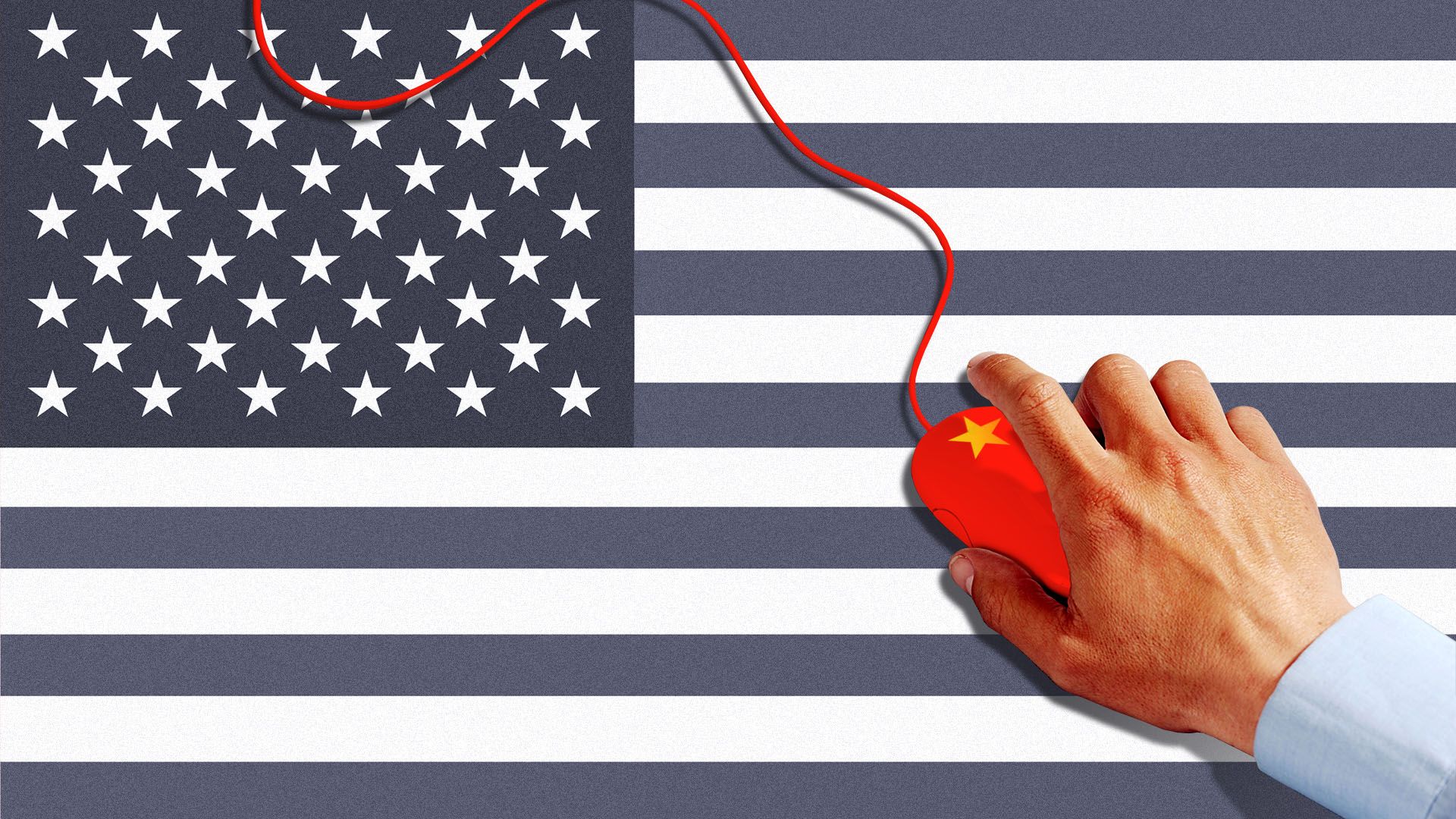
1 big thing: How China is shackling Trump's cyber agenda
President Trump wants to drive a hard line against nation-state cyber hackers.
- There's just one — pretty significant — obstacle in his way: China.
The big picture: China is America's biggest cyber adversary, but it's also the country that wields the most economic leverage over the U.S.
- For the Trump administration, keeping its promise to strike back against nation-state cyber spies, including China's, is a lower priority than managing trade ties with Beijing.
Driving the news: The Trump administration has paused plans to sanction China over last year's Salt Typhoon intrusions, according to a Financial Times report last week.
- Officials worry sanctioning China over Salt Typhoon would hurt the trade deal framework the U.S. and China struck in October.
- Thus, the administration has still yet to mount any public response to one of the most sweeping cyber espionage campaigns ever to hit the U.S.
- The White House did not respond to a request for comment. A Treasury spokesperson declined to comment.
What they're saying: "We've made ourselves into a big target," Matt Pearl, director of the strategic technologies program at the Center for Strategic and International Studies, told Axios.
- "It would be unfortunate if this was more than a short-term, tactical decision."
Between the lines: This isn't the first time the Trump administration has sidestepped national security concerns for economic considerations.
- Trump said Monday that he was lifting a blockade on exports of Nvidia's H200 chips to China, in exchange for a 25% cut from future sales for the U.S. government.
- Meanwhile, the TikTok ban — which passed with huge bipartisan majorities due to fears of cyber-enabled Chinese disinformation and data sharing — is still in limbo. The ban started as Trump's idea in 2020, before he changed his tune and declined to enforce it.
Zoom out: Trump's China problem comes as his administration reworks the federal government's role in cybersecurity policy and struggles to get top leaders in place.
- A forthcoming cyber strategy, expected as soon as next month, is reportedly just five pages.
- Congress failed this year to approve Trump's pick to lead the Cybersecurity and Infrastructure Security Agency — forcing the administration to resubmit a nominee for consideration in 2026.
- The Federal Communications Commission voted last month to roll back Salt Typhoon-inspired cyber rules for telecommunications providers.
- CISA is now ramping up for a hiring spree after losing more than a third of its headcount this year to buyouts and layoffs.
Reality check: China has been behind a range of cyberattacks on government agencies in the last year — and the Trump administration hasn't publicly responded to any of them.
- Anthropic uncovered evidence of China using its AI model to orchestrate 80%-90% of a cyber espionage campaign.
- The Salt Typhoon hackers reportedly broke into the phones of Trump and Vice President Vance.
- The U.S. has also said China breached the Treasury Department last December.
Yes, but: Sanctions are just one tool the administration can use to target China, and it's been common in past administrations to tamp down anti-China rhetoric and actions during similar economic negotiations, Pearl said.
- Indictments of individual hackers, visa restrictions and offensive cyber strikes are all on the table, Pearl added.
- The annual defense policy bill includes millions for the U.S. Cyber Command to increase its own cyberspace operations.
2. Adversarial hackers target open-source flaw
At least two China-linked hacking groups are actively targeting a critical vulnerability in the widely used React web framework, researchers warned.
Why it matters: The framework is the backbone of most modern-day web applications. If successful, hackers could exploit the flaw to execute malicious command right on a victim organization's servers.
Driving the news: The React Foundation disclosed a severe flaw in the framework on Wednesday that targets how it decrypts information transmitted to a user's web server.
- The flaw — which is being called React2Shell — is uniquely bad, receiving a rare 10 out of 10 severity score on the Common Vulnerability Scoring System.
- Maintainers started working with affected hosting providers and open-source projects to implement fixes before the flaw was publicly disclosed.
- Server network operators, including Cloudflare, Amazon Web Services and Fastly, have also rolled out patches. (Cloudflare's rollout even caused a 25-minute outage.)
- CISA is requiring civilian federal agencies to patch vulnerable systems by Dec. 26.
Threat level: Within hours of that public disclosure, Amazon threat researchers detected multiple China-linked hackers targeting the vulnerabilities in the wild.
- The React framework is downloaded more than 55 million times each week on the npm repository.
- Palo Alto Networks said last week that it had identified more than 968,000 vulnerable instances in its own customer data.
Yes, but: Detecting and finding all vulnerable versions of the React framework on a network is a tricky task.
- Web applications are nesting dolls of open-source code and projects — so it's normal for developers to not know for certain if a popular piece of open-source code is in their enterprise software.
What to watch: Experts are already warning that this vulnerability will lead to cyber intrusions for years to come, similar to the Log4Shell flaws uncovered in late 2021.
3. AI-generated kidnapping scams are coming
Criminals are using AI-generated photos and videos of people's loved ones to create virtual kidnapping scams for ransom, the FBI warned Friday.
The big picture: AI-related scams, from widespread voice-cloning tools to increasingly realistic AI-generated pictures and videos, are leaving people more vulnerable to fabricated crimes as the line between real and fake blurs.
How it works: In these scams, the FBI said, criminals text victims claiming to have kidnapped a loved one and demand payment, often escalating violent threats if the ransom is not paid immediately.
- When victims ask for proof, scammers send what appears to be a real photo or video of the loved one, sometimes using timed messaging features so the recipient can scrutinize it only briefly.
Yes, but: Upon closer view, many AI-generated photos and videos contain inaccuracies.
- Victims should look for missing tattoos or scars and imprecise body proportions, the FBI said.
By the numbers: A deepfake attack occurred every five minutes globally in 2024, while digital document forgeries jumped 244% year over year, according to the Entrust Cybersecurity Institute.
- U.S. losses from fraud that relies on generative AI are projected to reach $40 billion by 2027, according to the Deloitte Center for Financial Services.
Zoom out: Anyone targeted by a suspected AI scam should contact their loved one before agreeing to any terms or payments. Establishing a family or friend safe word can also help distinguish real from fake.
- The FBI noted that criminals act quickly to induce panic, so it's important to pause and question whether the self-declared kidnapper's claims are legitimate.
4. Catch up quick
@ D.C.
💸 CISA is ending a pay incentive program designed to recruit and retain cyber talent away from the private sector as it transitions fully to the Department of Homeland Security's Cybersecurity Talent Management System. (Bloomberg)
🏛️ The annual defense policy bill includes millions to boost Cyber Command's operations and pushes regulators to harmonize cyber rules for defense contractors. (Nextgov)
🪖 The Pentagon's inspector general says Defense Secretary Pete Hegseth put U.S. forces at risk when he sent sensitive information about a strike in Yemen over Signal. (Axios)
@ Industry
❌ Gartner is advising companies to block users from downloading and installing AI browsers due to the data security and privacy risks. (The Register)
🧳 Former cyber ambassador Nathaniel Fick is joining Cerberus Capital Management as chief strategy officer. (Bloomberg)
⚠️ Apple has sent users in 84 countries a warning that state-backed hackers may be targeting their devices. (Reuters)
@ Hackers and hacks
👯♂️ Virginia-based twin brothers and government contractors who previously served prison time for hacking the State Department were just arrested again for allegedly tampering with government databases. (Axios)
🧱 Several government agencies warned that Chinese hackers are targeting governments worldwide with the Brickstorm malware strain to maintain long-term access in victim organizations. (The Record)
📲 This holiday season, text message scammers are luring victims in with promises of unclaimed tax refunds and mobile rewards points. (KrebsOnSecurity)
5. 1 fun thing
🚽 Uh, beware the "smart" toilet camera that promises end-to-end encrypted photos....
☀️ See y'all next week!
Thanks to Dave Lawler for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Future of Cybersecurity, spread the word.
Sign up for Axios Future of Cybersecurity