Axios Codebook

February 21, 2019
Welcome to Codebook, the cybersecurity newsletter recommended by 4 out of 5 dentists.
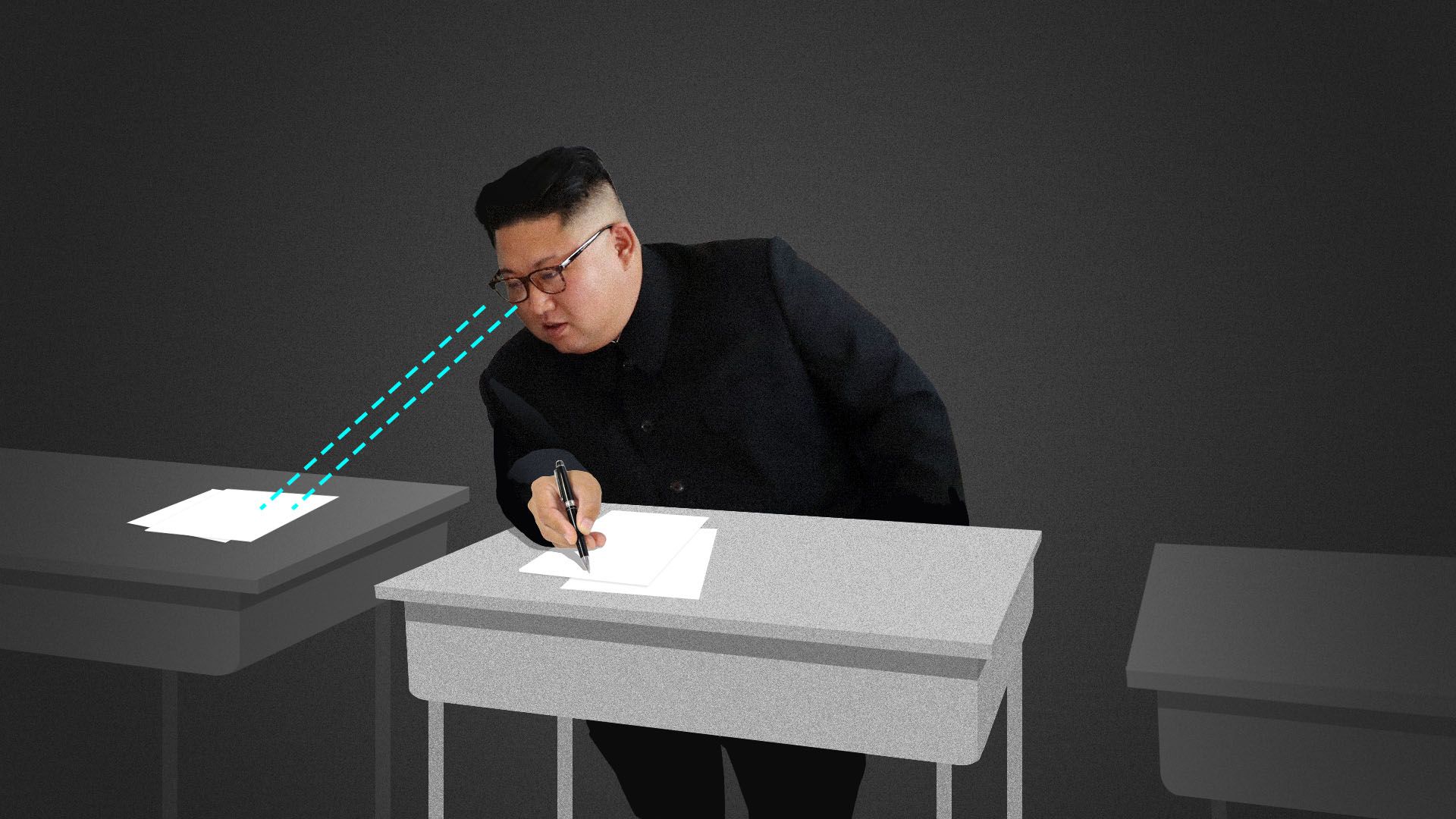
1 big thing: North Korean hackers could start stealing business secrets
Illustration: Sarah Grillo/Axios
As North Korea tries to rev up its economy, it may shift its hacking efforts from financial thievery to stealing intellectual property, China-style. That's according to a contested new theory from cybersecurity firm CrowdStrike.
Why it matters: North Korea is already one of the "big four" hacking threats — along with China, Russia and Iran — but it currently focuses on cash theft to fill its sanctions-drained coffers. Though experts are mixed on the likelihood Pyongyang's hackers would switch to the model China used to build its domestic industries, most seem to think it's a threat worth keeping an eye on.
The theory works like this:
- North Korea's long-held strategy, known as the byungjin line, had emphasized parallel development of nuclear and economic might. Now, the only goal is the latter — the Kim regime declared victory on the former last April.
- North Korea's chief resource right now, beyond its heavily sanctioned mineral deposits, is a giant corps of state-sanctioned cyber criminals.
- "North Korea will want to leapfrog its way into the global economy," said Adam Meyers, vice president of intelligence at CrowdStrike. "Vietnam is frequently mentioned as the model North Korea would follow to build a sustainable economy. But China would be on the table, too."
While CrowdStrike isn't seeing any current intellectual property theft, Meyers suggested a shift (if one is coming) could happen in the next two years.
- Depending on the continuation of sanctions, there aren't too many ways to spur economic growth in North Korea, noted Meyers — there are no viable sources of external investment.
Yes, but: North Korea lacks the infrastructure for the kinds of high-tech manufacturing that China succeeded with. Despite the finest 1970s-era Soviet manufacturing technology, North Korea doesn't have the equipment to mass-produce cheap, modern products, even if it stole the know-how to make them.
- Also, "they’re making a fair amount of money through hard currency, and they'd have to reassign those resources to do this," noted a skeptical Adam Segal, director of the digital and cyberspace policy program at the Council on Foreign Relations.
- Segal views North Korean IP theft as a technically possible but remote chance.
What they're saying: Other experts thought the possibility was, at least, something to monitor.
- Robert Manning, an Atlantic Council resident senior fellow with previous stints at the Office of the Director of National Intelligence and State Department, said he wouldn't be surprised by the development. But he cautioned that any intellectual property theft would probably skew toward goods that are easy to fabricate.
- That would include products like pharmaceuticals and pirated movies rather than the consumer, telecommunications and computer memory chip products China appropriated. Of course, North Korea might steal more complex secrets and sell them to other nations, Manning said.
- Jenny Town, an analyst for the Stimson Center and managing editor of its North Korea-focused 38 North blog, said the shift CrowdStrike is predicting is something to watch out for.
- "It has been dangerous in the past to underestimate North Korea on these things," Town said.
The big picture: With a summit between President Trump and North Korean leader Kim Jong-un slated for next week, the isolated regime's international situation is more in flux than it has been for decades.
2. Ukraine commits to joining NATO
Ukrainian President Petro Poroshenko signed a constitutional amendment Tuesday committing the country to joining NATO and the European Union.
Why it matters: Obviously, there are bigger factors at play here than just cybersecurity. From this newsletter's perspective, two factors resonate:
- Ukraine is under continual cyberattack from Russia, including two successful attacks on the power grid. If Ukraine was under the NATO umbrella, the U.S. might be obligated to respond.
- Russia blames the U.S. for NATO expansion. Russia doesn't always respond well to perceived slights on the international stage, including that time it messed with the 2016 U.S. election in part because it felt left out of the Olympics.
3. Kaspersky's U.S. sales skid
Kaspersky announced 4% global revenue growth in 2018 despite a 25% drop in U.S. sales.
The big picture: While Huawei is the current poster child for tech companies accused by the United States of sabotaging products to aid a government's espionage efforts, Russia-based Kaspersky was Huawei before it wasn't cool.
Meanwhile: Vermont announced it would wean the state off use of Kaspersky products, as well as ZTE and Huawei products. (StateScoop)
4. Microsoft expands security tools to European elections
Our headline Tuesday night read "Microsoft: Fancy Bear targeted European think tanks." But it's worth noting that news story came to light in context of Microsoft expanding access to free security tools already offered to protect U.S. and Canadian groups "underpinning the democratic process" to 12 European nations.
Why it matters: Microsoft is one of a number of firms that offer free security products for elections (Google, CloudFlare and Synack are others). But the more widely known names offering this kind of service, the better.
- In the United States, local elections groups have been hesitant to take free products without better guidance about which products are useful and which are snake oil trying to use the election for their own publicity.
- Microsoft doesn't have that kind of recognition problem.
- That doesn't make any of the other products less good. Whether you've heard of Synack or not, for example, it's a firm vetted and used in government contracts.
5. Sandia National Lab sends hackers to HADES

Circa 1550. Original Artwork: An engraving by W Stukeley. Photo: Hulton Archive/Getty Images
Sandia National Lab announced Wednesday it had developed a system to trick hackers into improving network defenses against them.
Details: Active defense — creating fake networks and documents to slow hackers — is not a new concept in security, but it is currently a rapidly evolving one. Honeypots, fake networks used to observe hackers in their element, are also a tried and true technique.
- Sandia's High-Fidelity Adaptive Deception & Emulation System (HADES) advances both concepts. It diverts detected hackers to a high-end simulated network to observe their techniques, monitors how they operate and automatically updates network defenses to defend against them.
The two-year project to create HADES was done in concert with security data analysis firm Splunk.
6. Odds and ends
- Extortion rings will pay as much as $1 million a year for insiders with access. (Digital Shadows)
- The threat information sharing group serving the retail and hospitality industry changed its name to reflect that (BusinessWire)
- Your catty corporate blog headline of the day: "Sorry, we didn’t mean to keep that secret microphone a secret, says Google." (Naked Security)
- North Korean hacking tools were spotted in attacks on Russia. (CyberScoop)
- Facebook! Blockchain! (The Verge)
- An ATM jackpotting tool was designed to look like a slot machine. (SecurityWeek)
- I can't be the first person to tell you this, but harvesting the blood of teenagers is ethically questionable at best. (CNBC)
Codebook will return next week.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.