Axios Codebook

March 26, 2019
Welcome to Codebook, the cybersecurity newsletter that only interviews people's enemies.
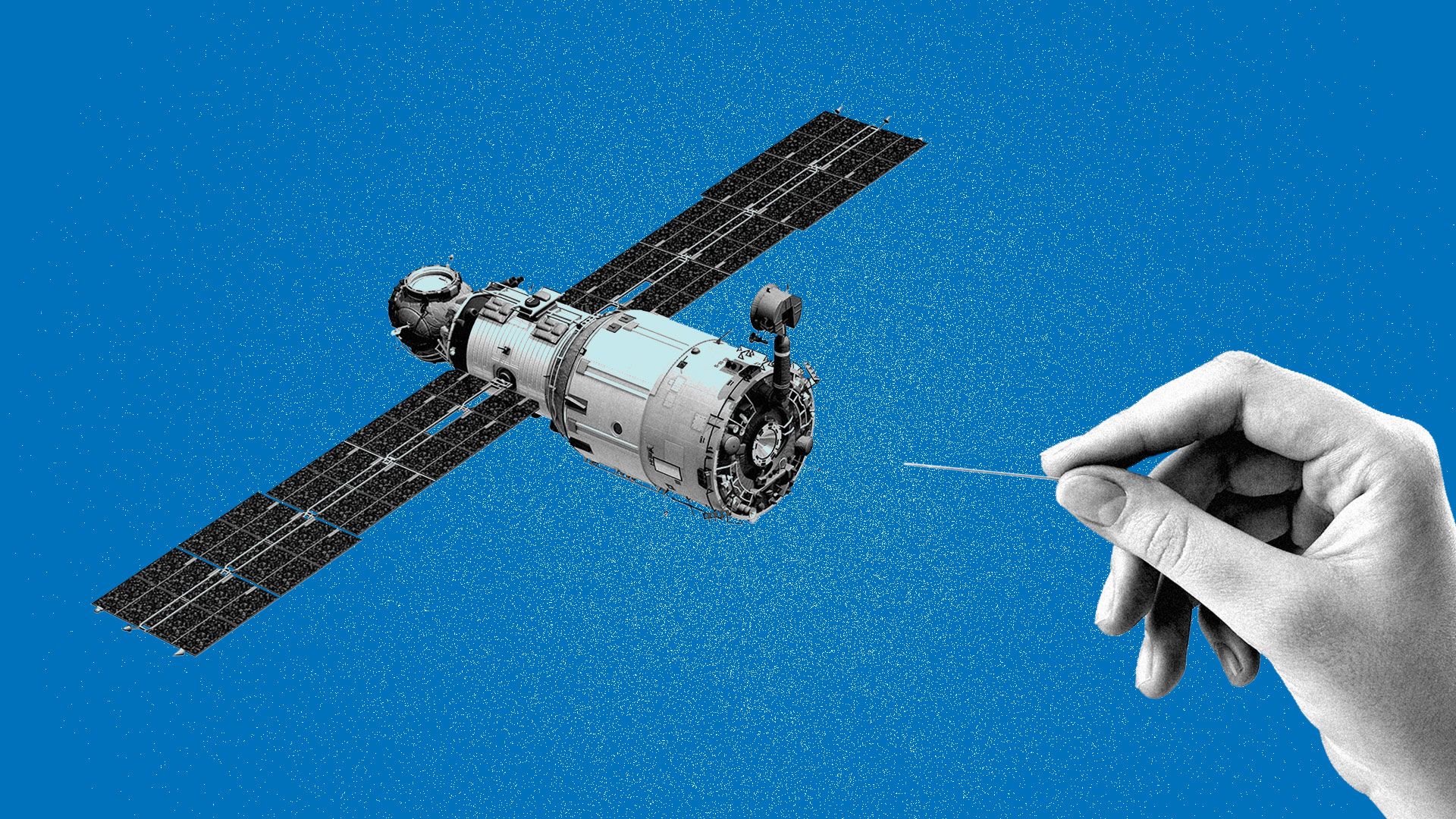
1 big thing: How Russia tampers with GPS
Illustration: Aïda Amer/Axios
Satellite navigation systems like the Global Positioning System (GPS) make so many different pieces of our global infrastructure tick that most countries treat their signals as sacrosanct, knowing that interfering with them could have devastating effects. But a new report released Tuesday is giving us the first broad view of a country — Russia — that's pervasively tampering with the service.
The big picture: Global navigation satellites — including GPS and less-used competing services like Russia's GLONASS — are coordinated networks of atomic clocks in outer space that can be used to triangulate precise locations or coordinate precise timing. Without them, everything from global shipping to financial markets would suffer.
Why it matters: It's easy to see the military, transportation and pizza delivery importance of precise location information. The timing signals are extremely important, too.
- The stock market needs precision timing to handle transactions down to the fractional second.
- Precise timing is a critical component in telecommunications because it allows national and international networks to synchronize.
The intrigue: Russia has been called out several times before for interfering with global positioning satellite systems, and it is known to capitalize on interfering with GPS for military and national security purposes like no other country. But before the study by the C4ADS think tank, no one had really taken a scientific look across all of Russia's activities to see how constant the disruptions are.
- To do that, C4ADS used University of Texas equipment placed on the International Space Station to monitor more than 9,800 suspected instances since 2016 where fraudulent global navigation signals appear to have been broadcast in the Russian Federation, as well as instances where similar signals were broadcast in Russian conflict zones like Crimea and Syria.
C4ADS is not formally accusing the Russian government of being behind any of the fraudulent, "spoofed" signals. It would be impossible to make that kind of determination from the space station.
But, but, but: It is clear that many of the instances largely serve Russian national interests.
- In Russia, C4ADS found that several spoofed signals came from areas where Russian VIPs (like President Vladimir Putin) were traveling or that contained military or domestic facilities Russia wants to protect (including a "multimillion-dollar 'palace'" reportedly built for Putin).
- Those areas broadcast the coordinates of airports in places where there are no airports.
- The spoofing was frequent enough that C4ADS reports the Russian internet firm Yandex had to redesign its ride sharing app. Otherwise, it billed passengers for sudden trips to the airport whenever their driver passed through a spoofed area.
- Airports that mysteriously seemed to appear in the Black Sea were so disruptive that the United States issued a warning to international cargo firms.
Why airports? Many manufacturers of drones use GPS chips to prevent their products from flying into airport airspace. C4ADS suspects the spoofing was to prevent drone attacks or surveillance.
Meanwhile, Russia also used spoofing in combat zones, particularly Syria, to try to limit attacks against its installations.
Go deeper: Read more, including how Moscow uses GPS hacking in battle.
2. EU passes controversial copyright law
A controversial European Union copyright law cleared its last hurdle Tuesday, to the dismay of protestors.
Why it matters: The copyright law has been a focus of intense criticism online.
Article 11 of the law, the so-called "link tax," would require sites like Facebook and Google to pay a fee when they summarize news stories and link to them.
- Supporters believe this will stop Big Tech from picking the pockets of news organizations who are going broke supplying the content that Silicon Valley exploits for its own profit.
- Opponents believe this may ultimately cause smaller sites, blogs and even the same news outlets the law is meant to protect to have to pay for the right to use links.
Article 13 of the law requires sites that distribute user-uploaded content to better screen for copyright violations.
- The problem, say critics, is that to accomplish this on a large scale, sites like YouTube would have to rely on automated scanning algorithms, which would inevitably cause more legitimate content to be swept up in the dragnet.
3. Audit offers recommendations to prevent next Equifax breach
Chairman of the House Oversight and Reform Committee Elijah Cummings (D-Md.) and Sen. Elizabeth Warren (D-Mass.) on Tuesday released an audit of shortcomings in how the government regulates data security at credit bureaus.
Why it matters: Nearly two years after the hackers stole personal information about the majority of Americans in the Equifax breach, lawmakers have made few systemic changes to prevent similar events from happening in the future.
Details: Cummings and Warren requested the audit from the Government Accountability Office in September 2017, and they're releasing the report in advance of a hearing about policy options to prevent future breaches held by the Oversight Committee’s subcommittee on economic and consumer policy Tuesday. The report recommends:
- The FTC should be able to enforce civil penalties under one of the main laws concerning credit bureaus.
- The Consumer Financial Protection Bureau (CFPB) should start regularly taking cybersecurity risks into account in examining credit bureaus.
- And the CFPB should take better stock of how many bureaus fall under its authority, as employees worry that the agency may not be aware of all the bureaus that meet its minimum thresholds.
4. Hacker group exploits ASUS' software update system
Photo: Dennis Lane/Getting Images
On Monday, Kaspersky Lab announced the discovery of Operation Shadowhammer, a group that implanted a backdoor in the systems of hundreds of thousands of ASUS-brand computers using the firm's software update system.
Why it matters: Shadowhammer infected all of those computers to target a preprogrammed list of 600 computers. This is concerning for a few reasons:
- The group behind the attack was sophisticated enough to exploit the software update system of a major tech firm, including accurately faking its software certificates.
- The group was willing to infect the supply chain of the many to get at the few.
- After infecting machines, malware checked if they were the target group by looking for MAC addresses, unique identifiers in the networking hardware. That means they had advanced knowledge of who they were looking for.
This is not a reason to stop updating software, which, in nearly all cases, improves rather than decreases security. It's very rare that attackers can copy certificates this way.
ASUS released a statement Tuesday morning about the incident, saying a "small number" of machines were infected by malicious code (countering Kaspersky's estimate of half a million).
5. Researchers lock up LockerGoga
Researchers at Alert Logic believe they have discovered a way to halt LockerGoga ransomware in its tracks.
Why it matters: LockerGoga has been used in a crippling string of ransomware attacks at industrial firms, causing industrial plants to temporarily shut down.
Details: Alert Logic claims that a specific type of malformed files used to link to files on other systems can crash the malware before it starts encrypting files. The trick involves a .lnk file placed in the "Recent Items" folder.
To be clear: This may just be a temporary fix. Whoever is deploying the malware could fix their wares to not be derailed by the bug.
6. Odds and ends
- Facebook takes down pages with ties to Iran and Russia (Axios)
- The new Swiss online voting system has yet more security problems. (University of Melbourne)
- Security intelligence firm Terbium Labs nabbed a $2 million investment from the Omidyar Network. (Terbium Labs)
- NSO Group, a militarized spyware contractor whose wares routinely are being used against activists and journalists, is launching an advertising offensive. (Motherboard)
- An Irish/American dual citizen accused of running dark web hosting for child pornography sites is facing charges in the U.S.
- DHS is requesting more money for CISA cybersecurity staff. (FedScoop)
- Your "strange headline belying a serious story" of the day: "‘Mutant Rabbit’ Lost By University of Michigan Laboratory, FOIA Docs Show." (Motherboard)
Codebook will return on Thursday.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.