Axios Codebook

June 21, 2018
Welcome to Codebook, the only cybersecurity newsletter written by my mom (see below).
Tips? Please reply to this email.
1 big thing: The mystery of the municipal billing breaches
Illustration: Lazaro Gamio/Axios
Over the past year, at least 10 cities using online billing software called Click2Gov alerted citizens of credit card breaches. But the software being breached was not Click2Gov's program; it was the web platform cities installed to allow Click2Gov to run.
Why it matters: The ordeal has led to confusion about who's actually responsible for keeping these servers secure — cities, who thought they were installing a set-it-and-forget-it billing solution, or a software provider that didn't create the software that kept being undermined.
The discovery: Earlier this month, Inga Goddijn of Risk Based Security noticed something strange. Risk Based Security compiles and analyzes breach notification letters nationwide. And one software title kept coming up in letters being sent by cities: Click2Gov, from Superion Software.
- Those cities, largely small and midsized ones, ranged from Oceanside, Calif. and Goodyear, Ariz. to Fond Du Lac, Wis. and Ormond Beach, Fla.
- The most recent breach (Oxnard, Calif.) was just under a month ago.
- The breaches were not the only problem. Several cities Codebook spoke to reported hackers had also installed cryptocurrency mining programs on their systems.
The intrigue: Codebook spoke to computer security staff in several of the cities, who largely asked to remain anonymous. When Superion investigated breaches, they found hackers entered not through the Click2Gov software, but through Oracle's WebLogic application server — third-party software installed to run Click2Gov.
- The Weblogic vulnerability has a patch.
- Though breaches begain in the summer of 2017, cities breached by the end of the year say they had not been notified by Superion. And a few feel a little burned: "If it wasn't for Click2Gov, we wouldn't have installed WebLogic. If they had just told us about the vulnerability, we wouldn't have blamed them."
- That city claims to be changing its billing vendor in the near future.
Since the problem is not Superion's software, the cloud version of Click2Gov has not been subject to the same rash of breaches.
Typically, it's a vendor's responsibility to make sure its own software works. A separate software package might be the responsibility of the client who installed it or the vendor who made that product.
Superion, for its part, says it has taken a more proactive stance, making sure its clients know to patch WebLogic — it now claims to have helped 99% of customers currently have patched their systems.
The big picture: If you paid a utility bill using Click2Gov, there's a chance a different piece of software left your data vulnerable to a breach. And if you run a server make sure you keep all the software updated.
2. Russia may have scanned all 50 states in 2016, but don't panic
Press outlets were quick to pick up on a point made by Obama cybersecurity czar Michael Daniel at a Senate hearing yesterday — that Russia likely scanned election-related systems in all 50 states in 2016. That's jarring to hear, but it's less of a bombshell than it may seem.
Stay calm: Scanning is different from hacking, the way that Googling directions to a bank is different from robbing it. Scanning is simply collecting publicly available, unprotected data that could be used in attacks. The Department of Homeland Security has been frustrated by people who characterize one as the other.
- We knew definitively that at least 21 states had been scanned this way. The majority of those states were not attacked.
- Daniel was saying it seemed likely that, if Russia scanned 21 states, it probably completed the set.
- Codebook will further up Daniel's ante: D.C. was probably targeted, too.
We already knew Alaska was scanned, which — with due respect to our readers up north — should probably be a clue that Moscow wasn't limiting its scanning to states with the top strategic value. Alaska has voted Republican for more than 50 years. Trump was likely not in much jeopardy.
3. White House seeks a homegrown privacy initiative
Illustration: Lazaro Gamio / Axios
Axios broke news Wednesday that Gail Slater, special assistant to President Trump for tech, telecom and cyber policy at the White House National Economic Council, has met with industry groups to discuss creating a broad broad privacy framework for the U.S., as a counter to the E.U.'s GDPR privacy regulation.
Why it matters: GDPR is chock full of danger for unprepared U.S. firms — penalties for violating the new law can total 4% of global revenue. It looks like the White House is aiming to install its own guardrails for the use of personal data.
Our thought bubble: "This is very, very early on in the process, and conversations the White House is having are mostly conceptual. It doesn't appear that a comprehensive interagency process is fully kicked into gear yet," said Shannon Vavra, who broke the story.
"The timing on when that will happen (if at all) is unclear, since the White House is working to get industry buy-in before rolling out a policy — that, or face political backlash. But the bottom line is that the administration doesn't want GDPR to be the baseline for the U.S."
4. Google rolls out new account privacy interface
Google is rolling out a new Google Accounts interface simplifying user access to privacy settings, including what apps store data, and providing dedicated support. The features are available now on Android and will soon be brought to other platforms.
Why now: It takes longer than a few months to design and test interface changes, but it's hard to view any privacy rollout outside the lens of self-regulation since the Cambridge Analytica story broke at the end of March.
Why it matters: Whatever motivation is behind the changes, other companies tend to fall in line behind the biggest dog in the yard. If Google makes it easier for users to tweak privacy controls, it will probably get easier all around.
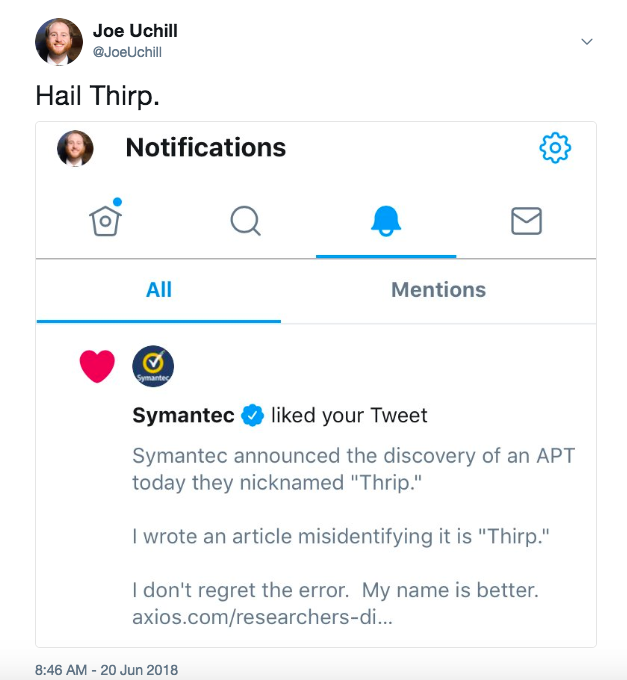
5. Wherein my mom explains the new Chinese espionage group
Thrip is a Chinese espionage group targeting satelite communications and geospatial intellegence groups in the US and Asia. Thrip was discovered by Symantec's AI systems. Thrip hides by using common networking tools rather than easier-to-spot malware. You can read about it here.
Thirp is a typo I spent a lot of Tuesday arguing would be a better name.
Joe's mom explains: "Why thrip is a good name for those of us who only understand garden metaphors:
"A thrip is a minute black winged insect that sucks plant sap and can be a serious pest of ornamental and food plants when present in large numbers.
"So: ornamental programs beware! it will suck the life out of them."
I talked to Symantec. Mom is right.
6. Odds and ends
- Lots of internet-connected things are vulnerable to a decade old attack called DNS rebinding. (The Register)
- The former employee Tesla accuses of stealing data and sabotaging systems says all he did was steal documents to blow the whistle on dangerous practices. (Washington Post)
- A controversial copyright bill is moving forward in the EU. (Motherboard)
- Lawmakers are asking Google to end a partnership with Huawei on national security grounds. (Axios)
- Flashpoint gives a mid-year update to its threat intelligence report. (Flashpoint)
Codebook will return on Tuesday. Thanks, mom!
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.