Axios Codebook

December 16, 2022
😎 TGIF, everyone. Welcome back to Codebook.
- 🎉 We have just one more issue after today's in 2022. Have any accomplishments from the year you'd like to share with Codebook readers next week? Reply to this email!
- 📬 Have other thoughts, feedback or scoops to share? [email protected]
Today's newsletter is 1,408 words, a 5.5-minute read.
1 big thing: NSA and Cyber Command weigh divorce
Illustration: Aïda Amer/Axios
Capitol Hill debate about maintaining the National Security Agency and U.S. Cyber Command's shared leadership structure is about to become an annual occurrence — adding momentum to a steady push to break up the agencies' long-questioned relationship.
Driving the news: The recently Senate-passed annual defense policy bill — the National Defense Authorization Act — would require the defense secretary to give Congress an annual briefing, from next year through 2028, about the NSA and Cyber Command's relationship.
Why it matters: Annual briefings often set the stage for lawmakers to make major legislative moves down the line.
- The new reviews would also set a foundation for Congress and the Pentagon to study the relationship more regularly, further preparing the agencies for a possible split.
The big picture: The two Defense Department agencies are run by the same person, but in recent years, Washington has become more interested in possibly giving each agency its own leader.
- Since 2016, the two agencies have been disentangling their most critical operations, as required by Congress, in preparation for a possible split.
- The "dual-hat" structure nearly faced its end during the Obama administration and twice during the Trump administration.
- A group commissioned by the Biden administration recently wrapped up a review of the dynamic — but didn't reach a conclusive decision, per The Record.
State of play: When Cyber Command was stood up in 2010, it pulled heavily from the NSA for staff, since the intelligence agency was one of the first to explore offensive cyber missions.
- But the two offices think about cyber differently: The NSA focuses on intelligence gathering and surveillance, while Cyber Command pursues offensive and defensive military cyber operations.
Between the lines: Proponents of the dual-hat structure argue that Cyber Command and the NSA still rely heavily on the same intelligence skill sets and talent to conduct their operations. Having one leader at the top to balance how collected intelligence informs missions is essential, supporters argue.
- But opponents of the shared leadership structure worry that the two agencies use intelligence in completely different — and often compromising — ways. The NSA likes to remain in the shadows on the networks it accesses, while Cyber Command leans toward disruptive missions.
Yes, but: Cyber Command still lacks the resources it needs to operate on its own, former officials tell Axios.
- "The ability to effectively accomplish both missions continues to benefit from a single commander/director," said retired Lt. Gen. Charles Moore, who recently stepped down as deputy commander of Cyber Command, in a statement to Axios.
The intrigue: At the center of Washington's ongoing debate is the question of what the future of Cyber Command, and cyber warfare in general, should look like, one of the command's founding members, Josh Lospinoso, tells Axios.
- Lospinoso argues that Cyber Command could stand up on its own faster if it focused missions on disrupting "relatively poorly defended cyber physical systems," rather than replicating or leaning heavily on the NSA's IT knowledge.
The bottom line: No one expects the Biden administration to overhaul the leadership structure anytime soon — if at all. But the annual reviews would give lawmakers and the Pentagon more insight into how sustainable the dual-hat arrangement actually is.
- "It's a little bit like a marriage," says Jonathan Reiber, a former DoD official during the Obama administration. "You look at it from the outside, and it looks one way and it sounds one way, but unless you live in it, you actually don't know whether or not to split up or not."
2. Meta targets accounts tied to spyware
Illustration: Aïda Amer/Axios
Facebook's parent, Meta, removed hundreds of accounts in the last year across Facebook and Instagram tied to known spyware and surveillance-for-hire vendors, according to a report released Thursday.
The big picture: Major tech companies have become one of the first lines of defense against the global proliferation of spyware and surveillance-for-hire vendors, given the companies' unique visibility into how the vendors abuse their platforms and devices.
- These vendors typically build and sell hard-to-detect spyware to governments and other nefarious actors that's installed on phones through their security flaws.
Details: Researchers said they removed several account networks across Facebook and Instagram that spyware and surveillance-for-hire vendors relied on for product testing and data scraping.
- For instance, Meta removed 130 Facebook and Instagram accounts tied to spyware vendor Candiru and 250 accounts tied to vendor Quadream that they believed were being used to test their tools.
- Meta also removed about 230 accounts on Facebook and Instagram linked to spyware vendor CyberGlobes that were used to scrape user data.
Yes, but: Spyware makers also rely on other legitimate tools outside of Meta's and other companies' reach, the report notes.
- One example is Indian firm CyberRoot, which a Reuters investigation exposed as a hackers-for-hire service relying on marketing tool Branch to manage and track phishing links.
- "This demonstrates just how important a whole-of-society response is to tackling this growing malicious industry," the report says.
Catch up quick: Meta isn't alone in taking on spyware vendors.
- Google released a report last month exposing Spanish IT company Variston IT as a spyware maker.
- Both Apple and Meta-owned WhatsApp are in the middle of lawsuits against NSO Group.
3. An alternative to protect against quantum
Illustration: Aïda Amer/Axios
In the race to protect data from encryption-breaking quantum technology, two researchers are pushing a faster, more effective way to secure government secrets in a post-quantum future.
Driving the news: Pursuing a fragmented, yet still encrypted, data storage scheme might be the best bet companies have now to get ahead of the quantum threat in time, according to research published today by the Foundation for Defense of Democracies (FDD) first shared with Axios.
Why it matters: Depending on who you ask, quantum computers — which are expected to be able to crack today's encryption standards in less than a minute — could be operational anywhere in the next three to 28 years, but it will take about five to 15 years for organizations to transition to a new quantum-resilience standard.
- New government-approved encryption standards also aren't expected to be ready until 2024.
The big picture: It’s possible for agencies and other critical organizations to start pursuing a decentralized approach to encryption now, rather than having to wait for new quantum-proof encryption standards, the research says.
How it works: In the report, an FDD research team tested a data storage technique known as "augmented improbability of access," where data is individually encrypted and then stored in pieces across various places like the cloud, mobile devices and physical computers.
- Doing so would add more hurdles for hackers trying to collect any encrypted data they're trying to unlock since they'd need to break into multiple storage locations to piece together the whole file.
- Compare that to current encryption schemes, where typically hackers face only one central data repository.
Yes, but: Each organization would have to take time to figure out its unique storage needs, and implementation could still take "between two weeks and several months," per the paper.
- Waiting for post-quantum encryption standards might be better for organizations that don't have valuable or high-risk data to protect from foreign adversaries.
4. Catch up quick
@ D.C.
🏛 A top FTC official warned that companies under data privacy and security consent decrees, which include Twitter, have "no pause button." (Axios)
📲 The Senate passed a bill banning TikTok on all government devices, following a similar move among several state governments. (Axios)
💲 An FBI database filled with contact information for members of a wide-reaching information-sharing partnership was put up for sale on an English-language cybercrime forum this week. (KrebsOnSecurity)
@ Industry
🎁 Microsoft is struggling to get customers to purchase once-popular bundles of its software and cybersecurity tools. (The Information)
📞 Instagram rolled out new security support initiatives to help people recover hacked accounts. (ZDNet)
🔐 GitHub is requiring all users to implement two-factor authentication by the end of 2023. (BleepingComputer)
@ Hackers and hacks
💪🏼 Feds seized 48 websites and charged six people in an operation targeting a cyberattack-for-hire operation. (Bloomberg)
🏥 A subcontractor for the Centers for Medicare and Medicaid warned the personal data of 254,000 individuals may have been exposed in a recent ransomware attack. (Nextgov)
🪙 Crypto exchange Gemini said a phishing campaign targeted its customers this week after breaching a third-party vendor. (BleepingComputer)
5. 1 fun thing
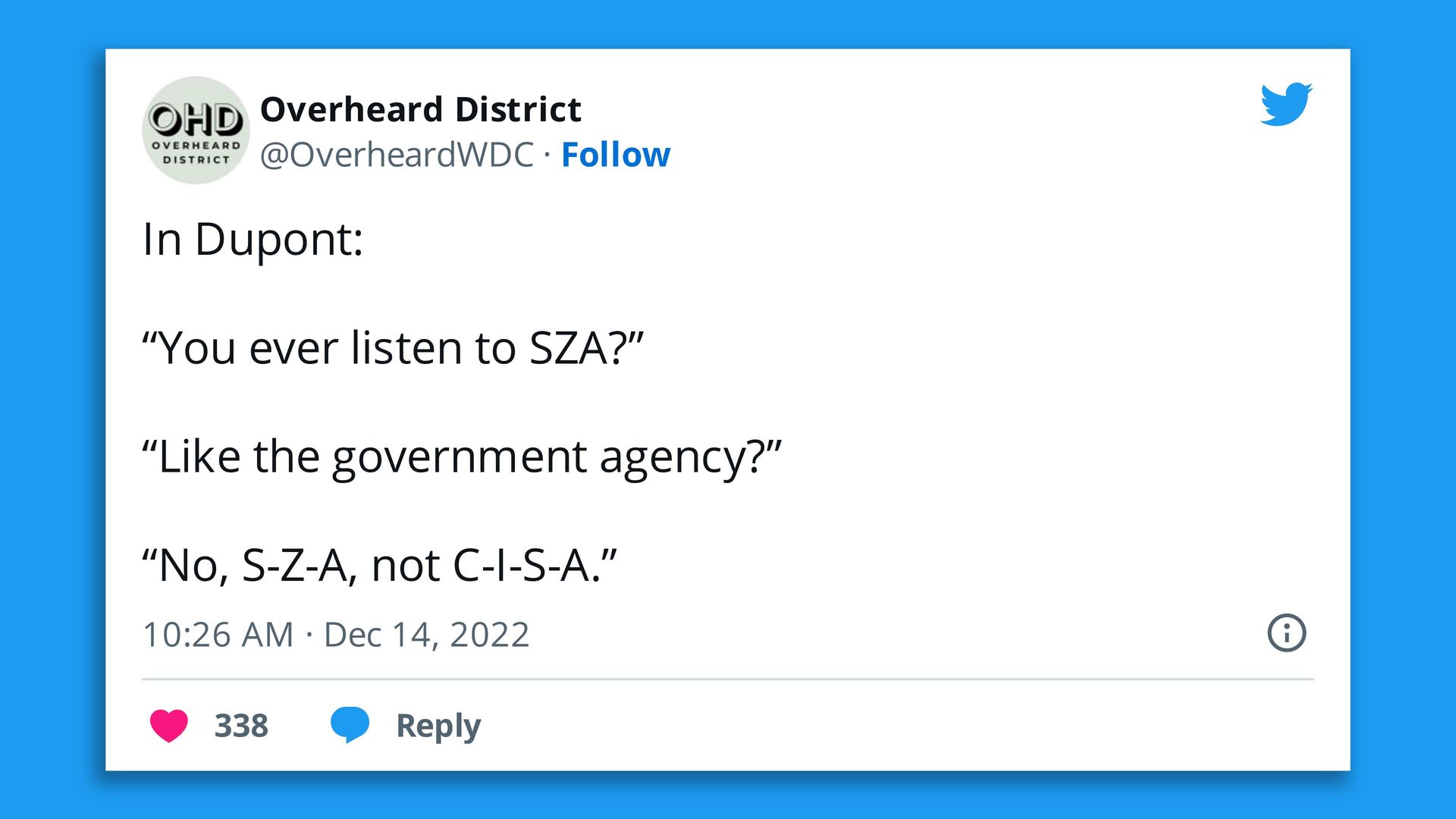
Screenshot: @OverheardWDC/Twitter
Godspeed to the person walking around D.C. this week who confused musician SZA with listening to the ... Cybersecurity and Infrastructure Security Agency??
- It's time for those of us in Washington to grapple with just how dorky we really are!
☃️ See y'all on Tuesday!
Thanks to Peter Allen Clark for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.