Axios Codebook

October 31, 2023
👻 Happy Halloween! Welcome back to Codebook.
- 📸 🐈⬛ 🐕 Reply to this newsletter with your best pet costume pics, please and thank you!
- 📬 Have thoughts, feedback or scoops to share? [email protected].
Today's newsletter is 1,595 words, a 6-minute read.
1 big thing: What relying on AI red teaming leaves out
Illustration: Annelise Capossela/Axios
Policymakers are increasingly turning to ethical hackers to find flaws in artificial intelligence tools, but some security experts fear they're leaning too hard on these red-team hackers to address all AI safety and security problems.
Why it matters: Red teaming — where ethical hackers try breaking into a company or organization — is a major touchstone in the AI executive order President Joe Biden signed yesterday.
- Among other things, the order calls on the National Institute of Standards and Technology to develop rules for red-team testing and calls on certain AI developers to submit all red-team safety results for government review before releasing a new model.
- The executive order is likely to become a policy roadmap for regulators and lawmakers looking for ways to properly safety test new AI tools.
The big picture: Employing red teams at companies is a tried-and-trusted security method.
- Many companies have internal teams that try to hack their employer to find and remediate any security vulnerabilities.
- But in the context of AI, red teaming has taken on an expanded definition that includes any program that lets users test tools to see what prompts could inspire bad outputs.
Catch up quick: Policymakers and industry leaders have been rallying around red teaming as the go-to practice for securing and finding flaws in AI systems.
- The White House and several tech companies backed a DEF CON red-teaming challenge in August where thousands of hackers tried to get AI chatbots to spit out things like credit card information and instructions on how to stalk someone.
- The Frontier Model Forum — a relatively new industry group backed by Microsoft, OpenAI, Google and Anthropic — also released a paper this month laying out its own standard approach to AI red teaming.
- Last week, OpenAI established a preparedness team that will use internal red teaming and capability assessments to mitigate so-called catastrophic risks.
What they're saying: "The emergence of AI red teaming, as a policy solution, has also had the effect of side-lining other necessary AI accountability mechanisms," Brian J. Chen, director of policy at Data & Society, told Axios.
- "Those other mechanisms — things like algorithmic impact assessment, participatory governance — are critical to addressing the more complex, sociotechnical harms of AI," he added.
Between the lines: Red teams are helpful when a problem is clearly defined, such as telling teams to hunt for known vulnerabilities and users to trick AI chatbots into writing phishing emails.
- But policymakers and tech companies have yet to determine what these models should be allowed to share and how they can be fairly used, which complicates the effectiveness of red teams, Data & Society senior researcher Ranjit Singh told Axios.
- Red teams also aren't equipped to tackle the larger questions around algorithmic bias in AI tools or fair uses for AI models, he added.
- Instead, companies and policymakers need to shift their attention to the algorithms and data sources at the heart of the models, rather than the outputs, David Brumley, a professor at Carnegie Mellon University and CEO of security testing company ForAllSecure, told Axios.
The intrigue: More funding is needed to expand AI security efforts beyond just internal and public red-teaming assessments, Singh added.
- "We are spending too much time building these technologies and a lot less money on ensuring that they're accountable and safe," he said.
- This scarcity has translated into "competing challenges" to figure out how best to assess security and safety, Singh said, and red teaming has the upper hand given how well established and easy it is for companies to focus on.
Yes, but: Biden's executive order does touch on broader safety and security problems — although questions about how it will implement those provisions remain.
2. Governments will pledge to not pay ransoms
Illustration: Sarah Grillo/Axios
A U.S.-led group of 48 countries is finalizing a pledge this week that their governments won't pay ransomware hackers if they're faced with an attack.
Driving the news: Anne Neuberger, deputy national security adviser for cyber and emerging tech, told reporters Monday that the pledge will come as part of this week's annual meeting of the Counter Ransomware Initiative (CRI).
- The European Union and Interpol will also sign the joint policy statement against paying ransoms, Neuberger said.
- The CRI member countries will launch a new project to leverage AI to analyze the blockchain to identify illicit funds tied to ransomware gangs, unveil the group's anticipated information-sharing program between members, and pledge to help any initiative member if they're hit with ransomware, she added.
Why it matters: Whether to pay ransomware hackers has been a major sticking point in the fight to disrupt and reduce the number of ransomware attacks around the world.
- This is one of the strongest signals from governments against paying hackers during an attack.
Catch up quick: The CRI was formed in 2021 as a tool to help establish norms on fighting and defending against ransomware.
- Last year, the group also pledged to not harbor ransomware criminals within their borders and started work on the information-sharing program unveiled this week.
Threat level: This year's initiative meeting comes amid an uptick in ransomware attacks.
- The number of ransomware attacks in 2023 has already outpaced the total for 2022, according to a report from cyber insurer Resilience released this month.
- However, fewer companies appear to be paying ransoms, with Resilience saying only 15% of its ransomware victim clients paid in the first half of 2023, compared to roughly 21% last year.
The big picture: It's often difficult to enact an outright ban on companies or other organizations paying hackers a ransom when they're hit with ransomware.
- In some cases, paying hackers to decrypt their files and not leak stolen data can be cheaper than having to rebuild their networks or switch over to data backups.
- However, paying a ransom further motivates and enables criminal groups.
Yes, but: Most ransomware criminals are operating in countries like Russia, China, Iran and North Korea that aren't members of the CRI.
- Some of these countries are also believed to be supporting ransomware gangs in some capacity.
Editor's note: This story has been corrected to note that Reliance's reported rate for ransomware victims paying in 2022 was roughly 21%, not nearly 40%.
3. SEC accuses SolarWinds of misleading investors
SolarWinds' headquarters in Austin, Texas, in April 2021. Photo: Suzanne Cordeiro/AFP via Getty Images
The Securities and Exchange Commission filed fraud charges Monday against software company SolarWinds and its top security executive in a case related to a wide-reaching cyberattack in late 2020.
Why it matters: It's rare for the SEC to charge a company over statements about its cybersecurity practices — even a company that has faced a cyberattack.
- The SEC is also charging Timothy Brown, SolarWinds' top security executive, with fraud — a decision that is sure to spark liability concerns among the security community.
Details: The SEC says in its complaint that SolarWinds and Brown presented misleading and false statements about the company's cybersecurity risks and practices from October 2018 to "at least" Jan. 12, 2021.
- The SEC alleges these statements were made in IPO registration forms, a security statement posted to the company's website, and a public 8-K filing made after the 2020 incident.
- In its security statement, the SEC claims, SolarWinds overstated the security of its password policies and software development process, as well as its policies for determining who has access to what internal data.
- SolarWinds made similar misleading statements throughout its SEC filings during that time, the SEC alleges.
Catch up quick: SolarWinds received public attention in late 2020 when a cybersecurity company then known as FireEye discovered that Russian state-backed hackers had broken into SolarWinds' IT systems and deployed malicious code into its software product updates.
- The incident — which went undiscovered for months and has been called the "most sophisticated attack ever" — affected roughly 100 companies and nine federal agencies.
What they're saying: "Today's enforcement action not only charges SolarWinds and Brown for misleading the investing public and failing to protect the company's 'crown jewel' assets, but also underscores our message to issuers: Implement strong controls calibrated to your risk environments and level with investors about known concerns," Gurbir Grewal, director of the SEC's enforcement division, said in a statement.
The other side: A spokesperson for SolarWinds and Brown's attorney both disputed the claims in the SEC's complaint.
Go deeper: SEC claims SolarWinds misled investors about cyber practices before 2020 breach.
4. Catch up quick
@ D.C.
📧 A Russian-speaking gang accessed the emails of roughly 632,000 employees at the Justice and Defense departments by exploiting a flaw in the MOVEit file-transfer tool this year, according to an obtained government report. (Bloomberg)
🌐 Internet and phone services are gradually returning in the Gaza Strip after an Israeli bombardment caused a blackout Friday. (Associated Press)
@ Industry
💰 Palo Alto Networks is acquiring Israel-based data management company Dig Security for a reported $400 million. (TechCrunch)
💸 HackerOne estimates it's paid out more than $300 million in bug bounties to ethical hackers since the platform's founding more than 10 years ago. (BleepingComputer)
📈 Demand for cybersecurity workers is still outpacing supply despite a growth in the total number of cyber workers, according to a new ISC2 study. (Nextgov/FCW)
@ Hackers and hacks
⚠️ Ransomware hackers have exploited at least 20,000 Citrix devices and stolen session tokens from organizations in an ongoing campaign, security researchers warn. (Ars Technica)
🔍 Dallas County confirmed it's investigating a possible cyberattack after a ransomware gang threatened to leak stolen data over the weekend. (The Record)
🪙 Crypto fraud researchers say they've uncovered evidence that hackers stole $4.4 million worth of cryptocurrencies last week using private keys and passphrases stolen during the 2022 LastPass breaches. (BleepingComputer)
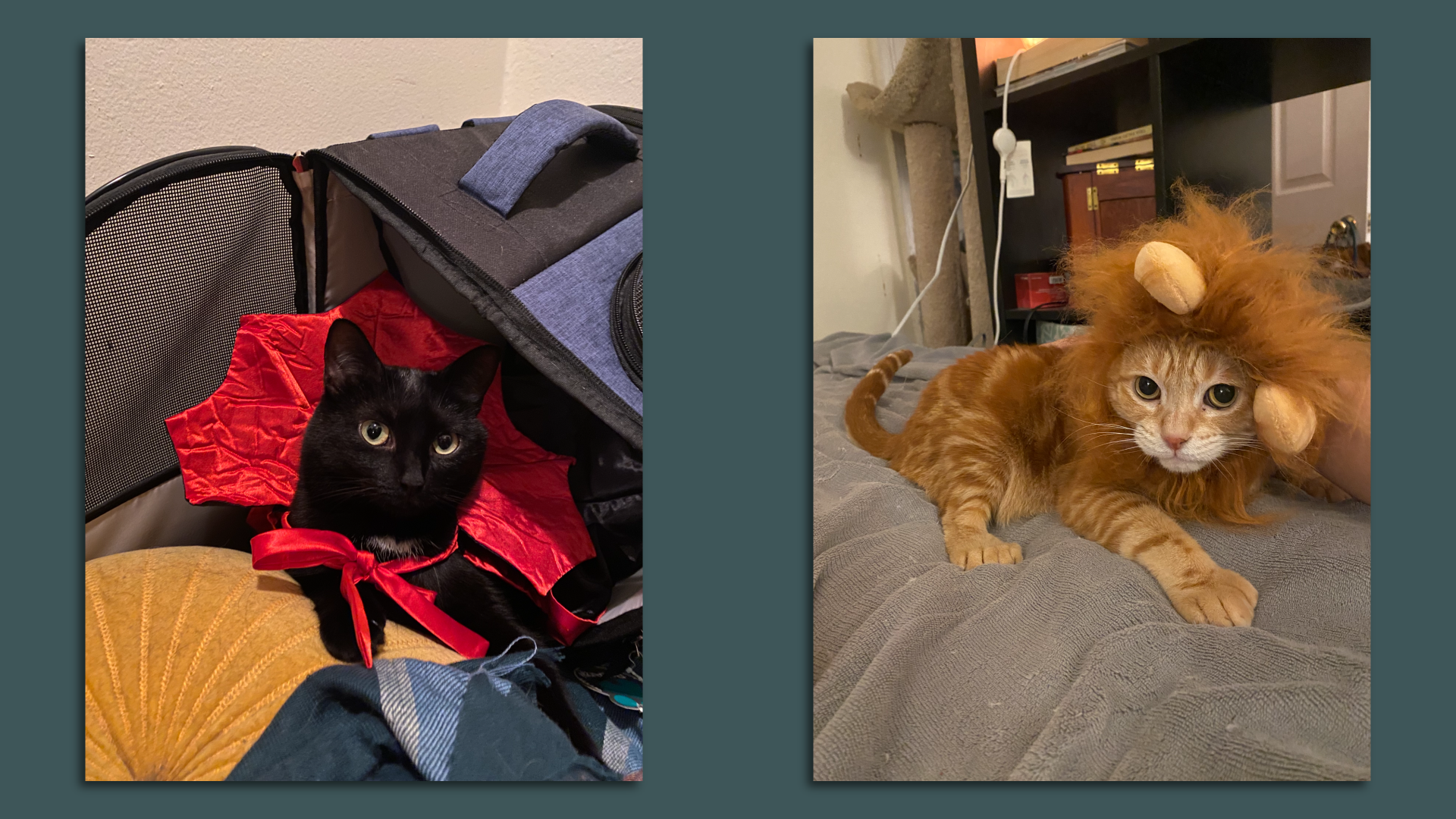
5. 1 fun thing
Lola (left) and Barry (right) contemplating how they're going to pay me back for this. Photos: Sam Sabin/Axios
I wouldn't ask for pet pics without giving you all something first!
- My Halloween cats — Lola the Vampire and Barry the Lion — hope you have a very spooky day! 🧛🏻♀️ 🦁 🖤
🎃 See y'all Friday!
Thanks to Scott Rosenberg and Megan Morrone for editing and Khalid Adad for copy editing this newsletter.
If you like Axios Codebook, spread the word.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.