Axios Codebook

March 21, 2019
Welcome to Codebook, the loose cannon cybersecurity newsletter that plays by its own rules.
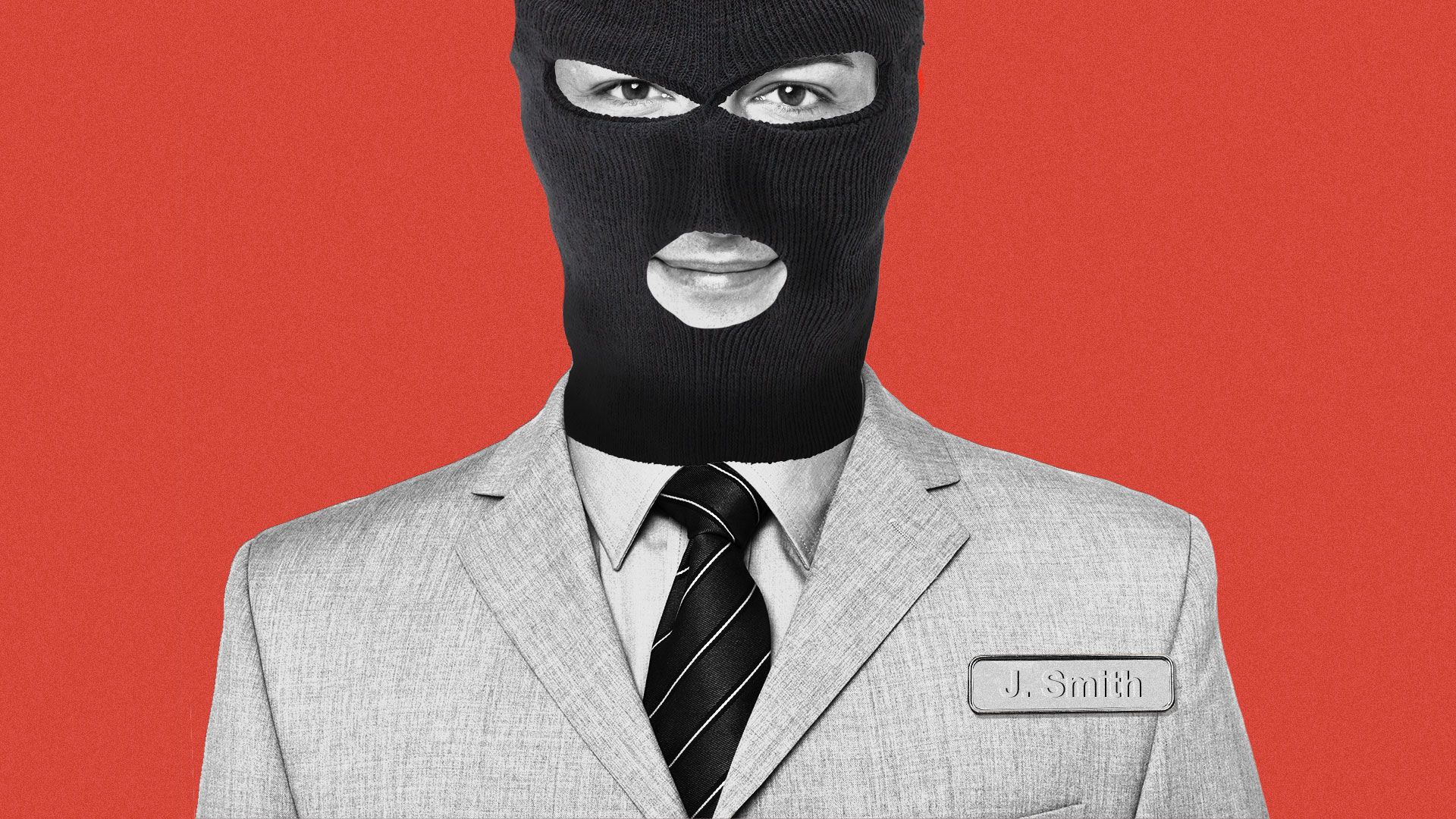
1 big thing: How to spot Russian spies — and other rogue employees
Illustration: Aïda Amer/Axios
Until his run ended in 2001, Robert Hanssen spent 20 years as a Russian mole burrowed deep in the FBI. That made him one of history's most successful inside threats — a class of threat that plagues both government agencies and private companies.
The FBI agent who went undercover to bring Hanssen down, Eric O'Neill, recounts the operation in "Gray Day," which hits bookstores next week. He spoke to Codebook about what Hanssen's tale can teach the rest of us about trusted insiders.
The big picture: It's not just hackers who steal files or funds; sometimes it's inside threats — employees exploiting legitimate access to a network to rob their employers. "They are people who already have the keys to the kingdom," said O'Neill.
- A 2016 survey found that 27% of attacks were either known or believed to be spearheaded by insiders.
The intrigue: While Hanssen was paid by Russia, according to O'Neill he was also motivated by resentment about being passed over for the fieldwork he sought and instead sent to man counterintelligence databases in an office.
- Disgruntled employees are a key source of insider threats. Just ask Tesla, where an employee passed over for promotion sent trade secrets to competitors last year.
- "Sometimes the people who don't get treated well or don't get promotions or are tired of being seen as the IT geeks, they can really cause the most damage," said O'Neill. "So it really behooves you to take care of those people."
- As in Hanssen's case, the biggest threats are the people with the most access, not necessarily the people with the highest status.
Trust, but verify: The FBI knew that someone in the government was leaking secrets to the Russians. But during their investigations, the agency refused to look internally for the mole.
- "It was a psychological flaw, willful blindness making the FBI so sure it was a CIA person that we didn't see that the guy was someone in the room with knowledge of these cases," said O'Neill.
- That's a block many organizations have when looking for insider threats. It's hard to doubt your own employees, and hard for employees to accept being viewed as a threat.
- With Hanssen, that meant actively ignoring warning signs, including a tip that Hanssen's wife had found a suspect pile of cash in their home.
- "My favorite thing to ask people is 'When do you think was the first time Hanssen, a 25-year vet of the FBI, was polygraphed?'" said O'Neill, noting that the FBI required a lie detector test every 5 years.
- The answer is that he was never given a lie detector until after he was arrested.
What's needed: There are ways to thread the needle and guard against insider betrayal without destroying trust between management and staff.
- "You have to make everyone feel like they are part of the process rather than being watched," said O'Neill.
- That means telling people to be on the lookout for abnormal behavior. "If someone has a problem, it's not just their problem," he said.
- Auditing networks for the removal of files or other strange activity is a non-invasive way of spotting trouble.
- Segmenting networks — keeping data that doesn't need to be connected in separate compartments — and pruning unnecessary network access can limit exposure.
2. Sec. 230: Why Devin Nunes is fighting uphill
The Devin Nunes defamation suit — the one pitting him against Twitter, a conservative pundit and a fake cow — is not an easy case for the California representative to win on any count. But it will be particularly difficult to win against Twitter.
The big picture: Legal experts Codebook spoke to do not think Nunes will be able to show that any of the insults on Twitter were defamation; hyperbolic trash-talking is already exempt from defamation. But there's a second level of difficulty with suing Twitter: the federal code known as Section 230.
Details: "Section 230 in the Federal code essentially says an internet provider is not the publisher," said attorney Mark Jaffe, the Mark in TorMark Law.
- Section 230 protects the infrastructure that transmits a message from defamation suits.
- People who feel defamed can sue an "information content provider" who is responsible for the content.
- Jaffe differentiates the two like this: If the New York Times publishes an article, it's the content provider for the article. If someone posts a comment to the article, the Times is serving as an internet provider for the comment.
- "The Nunes case on its face is what section 230 is talking about," said Jaffe.
The intrigue: In the court documents, Nunes' lawyer tries to make the case that, since Twitter shows liberal bias (an argument favored by conservatives but unsupported by evidence) and moderates posts, it is an information content provider.
- "This is the kind of argument that repeatedly gets dumped," said Jaffe. "Just being aware of the accounts and not taking the accounts down does not make Twitter an information content provider. It's allowed to moderate accounts without being an information content provider, but not required to."
3. Despite arrests, researchers find new FIN7 tools
1 big fin. Photo: Marisol Bogaard/EyeEm/Getty Images
The financial criminal group FIN7, also called Carbanak, has upgraded its hacking toolkit, according to researchers at Flashpoint.
Why it matters: The group suffered 3 high-profile arrests since January 2018. While FIN7 never stopped thieving, the existence of new tools means the R&D arm of FIN7 — not just those pulling off attacks — has continued unencumbered.
To be sure: No one ever thought the arrests would end FIN7. The group always appeared to have more than 3 members and seemed capable of filling vacancies. There was, however, the outside chance the arrests could halt the group's software production cycle.
The new tools include a new attack interface, dubbed "Astra"; new malware spread by phishing that runs self-deleting SQL database commands, dubbed "SQLRat"; and a versatile backdoor, dubbed "DNSbot."
4. Meet LockerGoga, the ransomware that felled Norsk Hydro
Cisco Talos offers this deep dive into LockerGoga, ransomware most recently seen crippling Norwegian aluminum manufacturer Norsk Hydro, one of the largest aluminum makers in the world.
The big picture: With ransomware attacks, there's often a question if the intention is really to extort money. Some infections are meant as smokescreens to hide other attacks, while others are intended to cause damage under the guise of extortion. Talos finds that coding quirks in LockerGoga, intentional or not, may cause irreparable damage to systems.
Details: New versions of LockerGoga can permanently log users out of their systems, making it impossible to see the ransom note explaining how to decrypt their files.
- That makes the ransomware an irreversible attack on systems, which may or may not be the point. The Russian cyberattack NotPetya, for example, deleted systems under the guise of ransomware.
Also: In another odd quirk, the ransomware does not list a cryptocurrency address to pay the ransom. Instead, it offers an email address to coordinate payment.
- That would make LockerGoga difficult to scale, and it would be more applicable to targeted attacks than indiscriminate masses of victims. Email providers will typically shut down accounts used in attacks, so in a mass attack they'd be unlikely to capture many payments.
5. Odds and ends
- Former DHS Undersecretary for Intelligence and Analysis Francis X. Taylor believes nationalized 5g service, as proposed by Trump advisers, would be a security risk. (Homeland Security Today)
- Google patched a Photos vulnerability that let attackers track locations. (Impervia)
- Plaintiffs in a Google privacy lawsuit may have lacked standing, ruled the Supreme Court, and lower courts will now take another look. (Reuters)
- A Lithuanian email fraudster plead guilty to scheming Google and Facebook out of $100 million. (Reuters)
- PewDiePie's fans continue to do him no favors. (ZDNet)
- Wikipedia is protesting strict copyright law proposals in the EU. (The Verge)
- The EU is facing Russian phishing attacks ahead of elections. (CNBC)
Editor's note: This piece was corrected to show Hanssen's run ended early 2001 (not December 2000).
Codebook will return Tuesday. (UCF over VCU, Virginia loses to Wisconsin, Zags win it all.)
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.