Axios Codebook

August 23, 2018
Welcome to Codebook, the cybersecurity newsletter that welcomes our squirrel overlords.
Tips? please reply to this email.
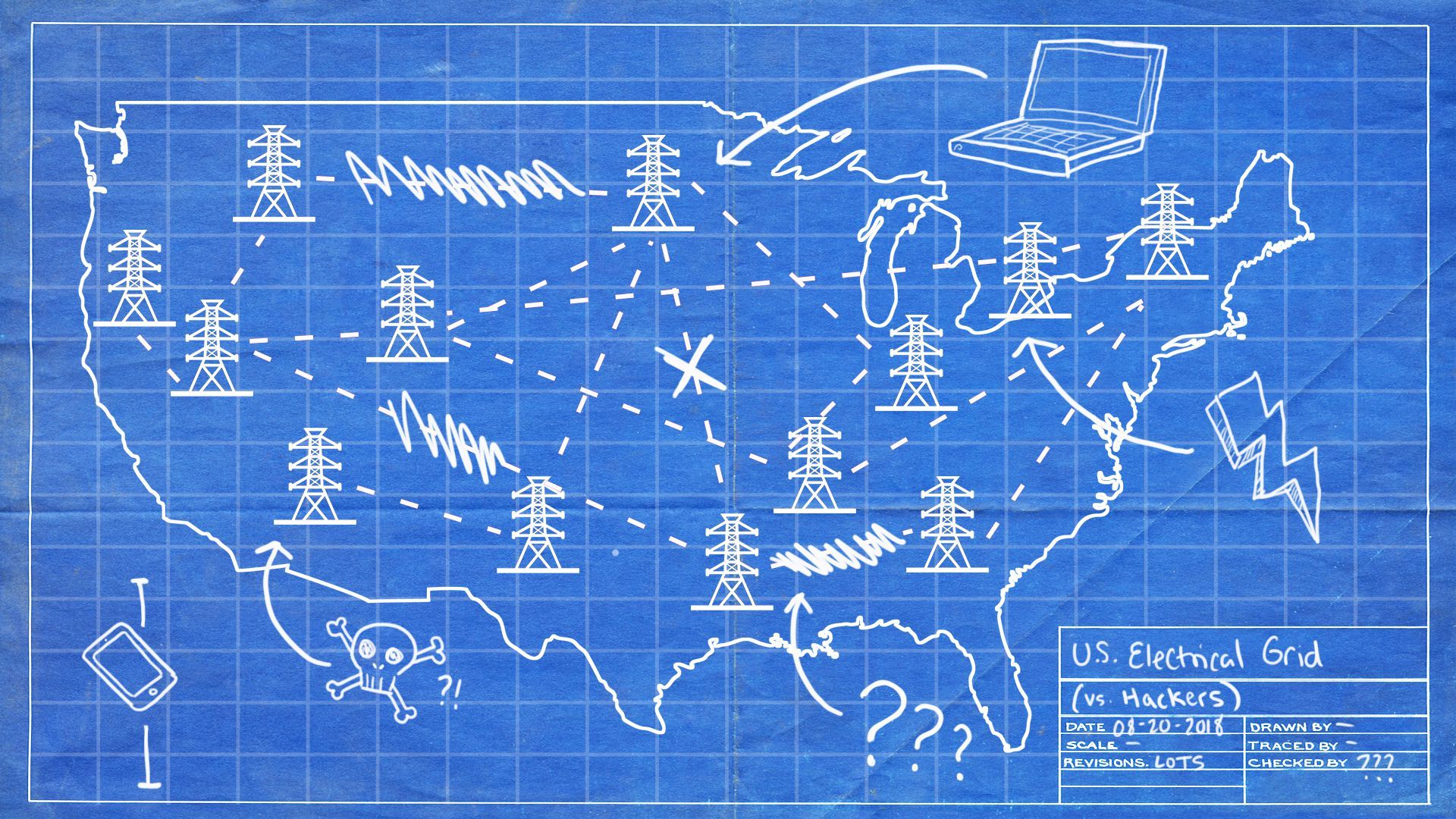
1 big thing: There is no grid to crash
Illustration: Sarah Grillo/Axios
In news stories, TV shows and at least one bestselling non-fiction book, you'll see warnings that hackers are coming to take out the U.S. electric grid, plunging the nation into democracy-ending darkness. An attack on that scale was even raised by leading intelligence officials in an Axios deep dive on global security threats.
The people tasked with protecting U.S. electrical infrastructure say the scenario where hackers take down the entire grid — the one that's also the plot of the "Die Hard" movie where Bruce Willis blows up a helicopter by launching a car at it — is not a realistic threat. And focusing on the wrong problem means we’re not focusing on the right ones.
So, why can't you hack the grid? Here's one big reason: "The thing called the grid does not exist," said a Department of Homeland Security official involved in securing the U.S. power structure.
Think of the grid like the internet.
- You can’t hack the entire internet. There’s so much stuff running independently that all you can hack is individual pieces of the internet.
- Similarly, the North American electric grid is actually five interconnected grids that can borrow electricity from each other.
- "When someone talks about 'the grid,' it's usually a red flag they aren't going to know what they are talking about," says Sergio Caltagirone, director of threat intelligence at Dragos, a firm that specializes in industrial cybersecurity including the energy sector.
Redundancy and resilience: Every aspect of the electric system, from the machines in power plants to the grid as a whole, is designed with redundancy in mind. You can’t just break a thing or 10 and expect a prolonged blackout.
The real threat:
- National attacks are unlikely. Small attacks matter more than you'd think.
- "People can relate to their freezer stopping working. It's tough to relate to what would happen if oil refineries stopped working," said Mike Spear, global operations director for industrial cyber security at Honeywell.
Go deeper with the full story.
1.5 Grid crash: the squirrel factor
This is how little cybersecurity and electric grid experts are worried about the national blackout scenario: The inside joke in industrial security circles is that squirrels are the real terrorists.
Punch a squirrel: There are a ton of power outages worldwide caused by squirrels and other animals. Experts will often compare the success rate of terrorists or nation states attacking power plants and various obscure species causing mayhem.
- For instance: There have been at least 13 jellyfish-related blackouts worldwide. There are still only the two Ukrainian blackouts caused by cyberwar.
IBM's Cris Thomas gave a presentation on how squirrels are "winning the cyberwar" at Shmoocon in 2017 that's worth checking out.
2. Reported new DNC attack was only a test
Photo: Saul Loeb/AFP/Getty Images
The DNC walked back an assertion that it had detected a "sophisticated" hacking attempt early Thursday, announcing instead that it was simply a subcontractor's unauthorized security test.
Why it matters: While this is a slight black eye for the DNC, which looks a little foolish for riling up the press over what turned out to be an internal matter, it's a massive victory for Lookout, the third-party security firm that caught the "attempt" with its unique approach to discovering phishing sites.
What actually happened:
- The DNC uses the contractor NGP VAN to manage its digital voter operations — specifically, a product known as VoteBuilder.
- Lookout discovered what appeared to be a newly-registered phishing site meant to look like the NGP VAN site and alerted several stakeholders.
- After an FBI investigation, it turned out that, according to the DNC's chief security officer Bob Lord, a third party "not authorized by the DNC or its vendors" set up the site to test Democrats' resiliency to phishing attacks.
- Michael Kan, a reporter for PCMag, determined that the unauthorized third party was the Michigan Democratic Party — technically a separate entity from the national group.
- It's not uncommon for organizations to try to phish their own members as both an educational experience and security audit.
The tech behind the hullabaloo:
- "Most people in security want to know why a mobile security company discovered the phishing site," Aaron Cockerill, chief strategy officer at Lookout, told Axios. "There are dedicated products to protect organizations from phishing. Lookout is not one of them."
- Cockerill said Lookout, which protects mobile phones, got into the phishing protection buisness because phishing remains a key mobile threat. Lookout caught the site where others didn't because it uses a different apparatus than other phishing protection services.
- Most products run checks on a site after links are sent to clients. "We call that the 'sacrificial lamb' approach," said Cockerill. "The links won't be detected as phishing sites until someone first sees them, which may be too late for that person."
- Lookout, on the other hand, uses AI to detect if any newly registered sites are phishing sites. In the NGP VAN case, Cockerill said, it identified the site half an hour after it launched.
3. DHS wants states to have "verifiable and auditable" voting by 2020
At a press conference Wednesday, Homeland Security Secretary Kristjen Nielsen called on all states to have "verifiable and auditable" voting systems by the next presidential election.
Why it matters: Her comments follow a July speech by Vice President Pence asking states to upgrade their voting systems from less secure, outdated electric systems that leave no mechanism to verify election results.
But, but, but: Pence didn't ask congress for more funding in his speech, and Nielsen told reporters she anticipated much of the funding for the upgrades to take place within states. Many state secretaries of state don't see that as a viable plan to pay for the costly equipment.
4. North Korea using trading apps to steal cryptocurrency
Researchers at Kaspersky Labs announced Thursday that they've discovered malicious cryptocurrency apps for Mac and Windows that the security firm tied to Lazarus, a well known North Korean government-sponsored hacking group.
Why it matters: A key goal of Lazarus, the group most known to Americans from the Sony Pictures attack, is to generate funds for the Kim regime to compensate for losses from sanctions. What makes the "AppleJeus" malware interesting, says Kaspersky, is that it's the first known attempt by Lazarus to attack MacOS.
The details: AppleJeus is a malicious updater application paired with a non-malicious trading app.
- Lazarus used the malware to breach an Asian cryptocurrency exchange.
5. Odds and ends
- Huawei is barred from providing 5g equipment to Australia, which already blocks the Chinese firm's industrial land line equipment. (Twitter)
- A case study in NotPetya: How Maersk responded. (Wired)
- The case for a cyber 911. (Cyberscoop)
- The hacker network that used stolen press releases to play the stock market. (The Verge)
- Police arrest a second suspect for SIM swapping in California. (Motherboard)
- There's a new, critical vulnerability in Adobe Struts. (ZDNet)
- Wickr launches secure chat that doesn't need domain fronting to hide its origin. (Wickr)
Codebook is taking a week off next week. You should too. We'll meet up again a week from Tuesday.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.