Axios Codebook

October 04, 2018
Welcome to Codebook, where it's all nation states all the time (see below).
Tips? Reply directly to this email.
1 big thing: Foiling North Korea's bank-robbing hackers
Photo: Pyeongyang Press Corps/Pool/Getty Images
For several years, North Korea has been conducting a spree of bank robberies online. A new report from FireEye makes clear that a recent attempt to "name and shame" a North Korean government-affiliated hacker did nothing to curtail the digital heists, and sanctions have only made Pyongyang more eager to steal money. But experts think the U.S. still has other levers it can pull.
Why it matters: While the Trump administration is trying to play nice with Kim Jong-un ("We fell in love," said Trump at a rally Saturday night), the continuing heist campaign has attempted to steal more than $1 billion total.
Background: After years of crippling sanctions, the Kim regime began using part of its cyber program to generate the cash North Korea needed to run. According to FireEye, North Korea began robbing banks in 2014, shortly after being sanctioned for its third nuclear test.
- Since then, the pile of international sanctions has only grown, including some for cyberattacks. Those sanctions appear to have encouraged more North Korean thefts.
The FireEye report, released Wednesday, is an argument that North Korea's bank hackers are separate and distinct from the country's other hacking ventures.
- The bank robbers, which FireEye calls "APT38," operate by hacking a victim and requesting large transfers over the SWIFT interbank messaging system. "The attack ends in destructive, disk-whipping malware. They want to destroy systems not only to delete evidence, but to give them time to launder funds," said Nalani Fraser, threat intelligence manager at FireEye.
- APT38 is one of a number of financial crime operations in North Korea. Other hackers, for example, rob cryptocurrency exchanges.
Name and shame: In September, the Trump administration publicly named, sanctioned and announced plans to charge North Korean Park Jin Hyok for, among other things, helping develop the WannaCry malware.
- The tactic, often called "naming and shaming," did not decrease APT38 attacks.
The diplomatic play: Trump could make financial attacks a deal breaker in nuclear negotiations with North Korea, suggested Andrew Grotto, former senior director for cybersecurity policy to Presidents Obama and Trump and a current fellow at Stanford's Center for International Security and Cooperation.
- "The Trump administration pulled out of the Iran deal in part because it didn’t address other issues, like hacking," he said. "If they’re consistent, they would try to address bank robbery."
The legal moves: Grotto notes financial crimes require an external, international network of collaborators — from money launderers to people who identify soft targets to attack. If we can't arrest hackers in North Korea, we could arrest confederates elsewhere.
- Since North Korea lacks the internet infrastructure needed to launch cyberattacks, many of its attacks are launched from other countries. Michael Daniel, former White House cybersecurity coordinator and the current president and CEO of the Cyber Threat Alliance, believes the U.S. could press countries to cough up North Koreans.
Returning fire: And, said Daniel, the United States could use cyber means to disrupt the networks.
Or all of the above: "It would likely be a complex mix of tactics," said Daniel.
2. Breaking news: US authorities charged 7 Russian GRU hackers
US authorities charged seven Russian GRU agents for hacking a number of targets, including the World Anti-Doping Agency and other sports-related targets, and conducting an influence campaign based on those breaches.
Why it matters: Fancy Bear, hackers believed to have breached the Democratic National Committee in 2016 to tamper in the 2016 elections, is also believed to be the group that hacked the WADA. Putting two and two together, if these guys hacked WADA, maybe, just maybe, they are also involved with the group behind the 2016 election hacking.
The details: The international hacking campaign included attacks against laboratories in Switzerland and Brazil — document dumps under a website for “Fancy Bear's Hack Team.”
The big picture: Earlier in the day, Dutch authorities announced arresting and expelling four Russian agents caught attacking the lab running tests on the poisoning of former Russian spy Sergei Skripal and conducting attacks on British officials.
- The sealed U.S. charges released today accuse "some of the same Russian operatives caught in The Hague, along with their colleagues in Moscow, as part of a conspiracy to hack a variety of individuals and organizations, in the United States, Canada, and Europe, to obtain information or access that was then exploited for the benefit of the Russian government," said U.S. Assistant Attorney General for National Security John C. Demers.
The arrests might recontextualize a Wednesday night announcement by the UK's National Cyber Security Center that Russia was indeed behind a number of attacks most believed they were already behind, including the WADA and DNC.
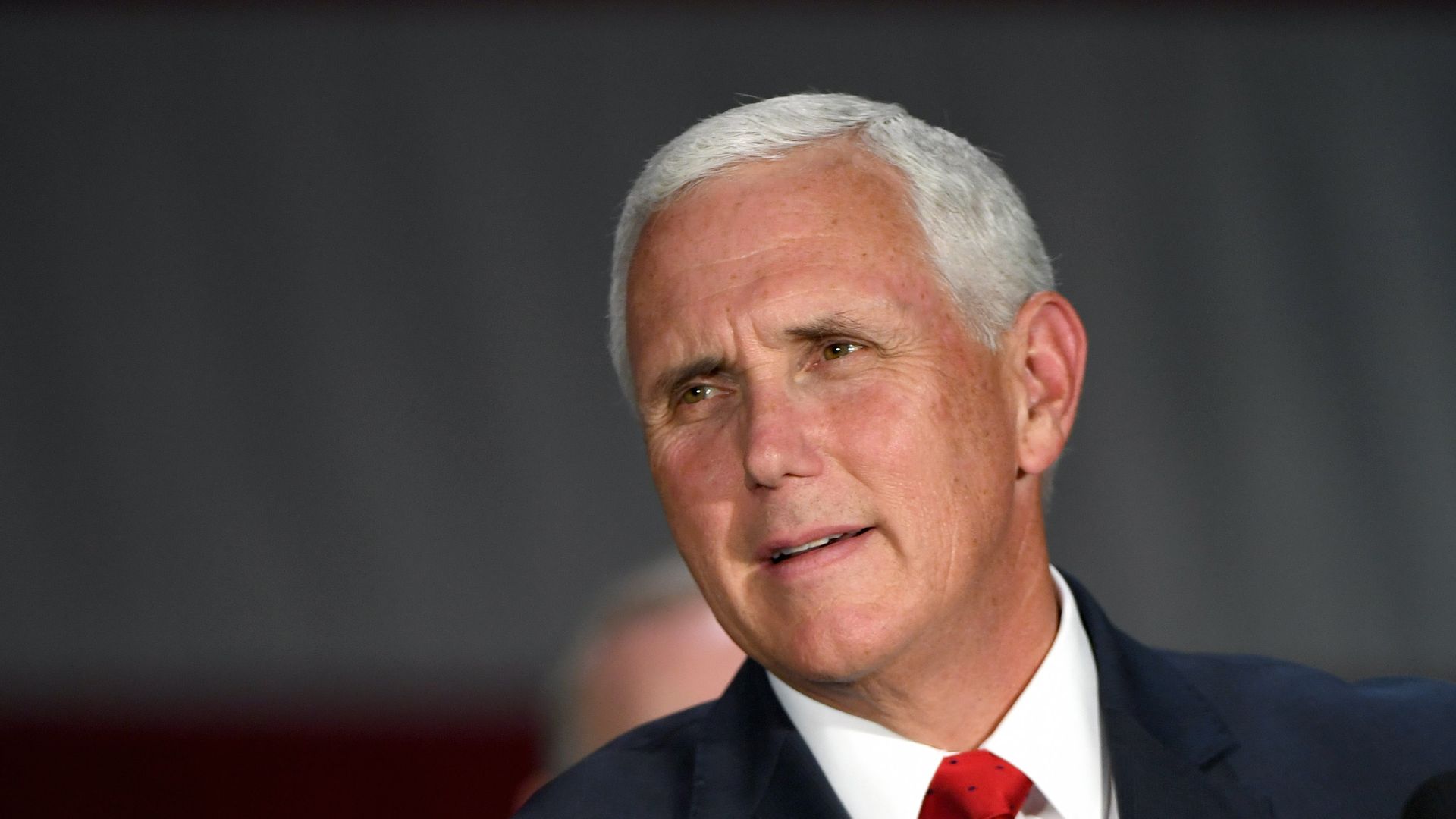
3. Pence reiterates case against China on election tampering
Vice President Mike Pence. Photo: Ethan Miller/Getty Images
In a speech Thursday at the Hudson Institute, Vice President Pence reiterated the administration’s accusation that China is interfering in the U.S. elections because it "wants a different American president."
The flashback: Last week Trump made similar claims at the UN and did little to back them up. Pence didn’t do much more.
The big picture: Pence said, “As a senior career member of our intelligence community recently told me, what the Russians are doing pales in comparison to what China is doing across this country.”
Nothing in today’s speech or last week’s claims backs that up.
Like last week, Pence mentioned that tariffs were targeted at industries in influential states and that China placed a clearly identified advertisement in the Des Moines Register arguing that a trade war is not in the U.S.' best interest. Neither of these appear to be about the election; both appear to be about trade policy.
Pence also mentioned that China:
- is now a major market for and funder of Hollywood movies
- funds think tanks
- is territorial about the South China Sea
- funded Venezuelan President Maduro
- makes a lot of loans to governments
None of this is similar to the kind of covert campaign that Russia conducted in 2016. China’s actions, as stated so far, are out in the open and (save for the South China Sea) within international norms. Russia hacked a political party, released secret data and ran a secret influence campaign.
The only example Pence cited that looks even remotely like a cyber action against the United States elections was a DDoS attack against the Hudson Institute website he said was in response to a speaker China didn't like.
The bottom line: Unless the administration has information it isn’t releasing, this is still not evidence of election interference.
4. Elsewhere in China news
- The Department of Homeland Security warned there was a new flurry of activity from the "cloudhopper" group, which the private sector linked to China. Cloudhopper has been active since 2017 and targets cloud and managed services to steal secrets.
- Bloomberg reports that, in 2015, China tampered with chips made by California's Supermicro that were used in server motherboards. Those sabotaged chips would have provided China access to whatever secrets passed through their servers. It's worth noting that Supermicro denies being aware of an FBI investigation into the chips mentioned in the story, that Apple and Amazon — which the story says independently discovered the sabotage — both deny having discovered it and that China denies the whole hullabaloo as well.
5. New Fancy Bear activity in South America, Europe
Fancy Bear is escalating espionage, particularly in Europe, according to a Symantec report released Thursday.
The big picture: Historically, most Fancy Bear hacking is to steal information. That's likely the goal here according to the report, which notes a more covert approach than the 2016 election hacking.
The targets identified by Symantec include several governments and military groups in Europe, one South American government, a "well-known" international organization and an Eastern European embassy.
6. Odds and ends
- The Senate voted to grant DHS a standalone cybersecurity agency. (FCW)
- A French police officer was caught selling police surveillance resources on the dark web. (ZDNet)
- The CEO of Phantom Secure plead guilty to selling encrypted communications devices to drug traffickers. (DOJ)
- Facebook sees no evidence that breached accounts were used to log in to other sites. (Facebook)
- Your headline of the day: "Mysterious Hole Shooting Out Flames in Arkansas Is Definitely ‘Not Satan,’ Officials Say." (Motherboard)
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.