Axios Codebook

January 15, 2019
Welcome to Codebook, the only cybersecurity newsletter officially informed that the president's Twitter account can't grant reporters a federal holiday.
Tips? Ideas? Feel free to respond to this email.
1 big thing: The slippery slope of supply chain fear
Illustration: Rebecca Zisser/Axios
Now that the U.S. and other countries are barring the use of Chinese-built 5G equipment — thanks to allegations that China's government sabotages those products for espionage purposes — we're beginning to see more suspicious treatment of other infrastructure built in China, too.
The big picture: Following the U.S. ban on Chinese-made telecom equipment from Huawei and ZTE, we'll have to decide whether that means other parts of other supply chains are also guilty by association.
- Fears that Beijing could convert Chinese-built trains into surveillance machines are leading some in government to question the vulnerability of Chinese mass transit equipment. That recently led D.C.'s Metro transit system to add cybersecurity safeguard specs to a contract for new rail cars.
- One solar electricity investor wondered to Codebook whether Huawei's line of solar equipment should face national bans, too. "If we’re talking about national security," he said, "why would electricity be any different than telecommunication?"
Regulators often deal with these kinds of supply chain issues product by product only after a problem is discovered. That leaves much of the burden on the customers, who are often left hoping that the product they bought won't eventually run afoul of the government.
Take solar equipment as an example:
- China's main focus in hacking is stealing information, including national secrets and intellectual property.
- Solar products are not a good venue for stealing the kind of information China is known to steal.
- They, could, however, be a hypothetical way for Chinese hackers to cause physical harm, including blackouts. That risk is wildly unlikely, say most China experts, and would amount to an uncharacteristic act of war.
With mass transit, there are not a lot of other options beside Chinese components. And as in many other industries, Chinese components are typically cheaper.
The big question: How do you maintain global supply chains without getting involved in the geopolitics of smart devices?
The risk management proposition for companies should be "holistic" and case by case, said Edna Conway, chief security officer of the global value chain at Cisco and a member of the Department of Homeland Security's supply chain task force.
- That means weighing many factors against cost, including the functionality of equipment, tactics to limit exposure to potential damage, availability of replacements, and opportunity to fully test the equipment.
The bottom line: Policies driven by economic nationalism are likely to be overly broad and potentially destructive. "The global value chain is a benefit to all. We can and should continue to avail ourselves of it," said Conway.
2. For sale: Access to tamper with U.S. news sites
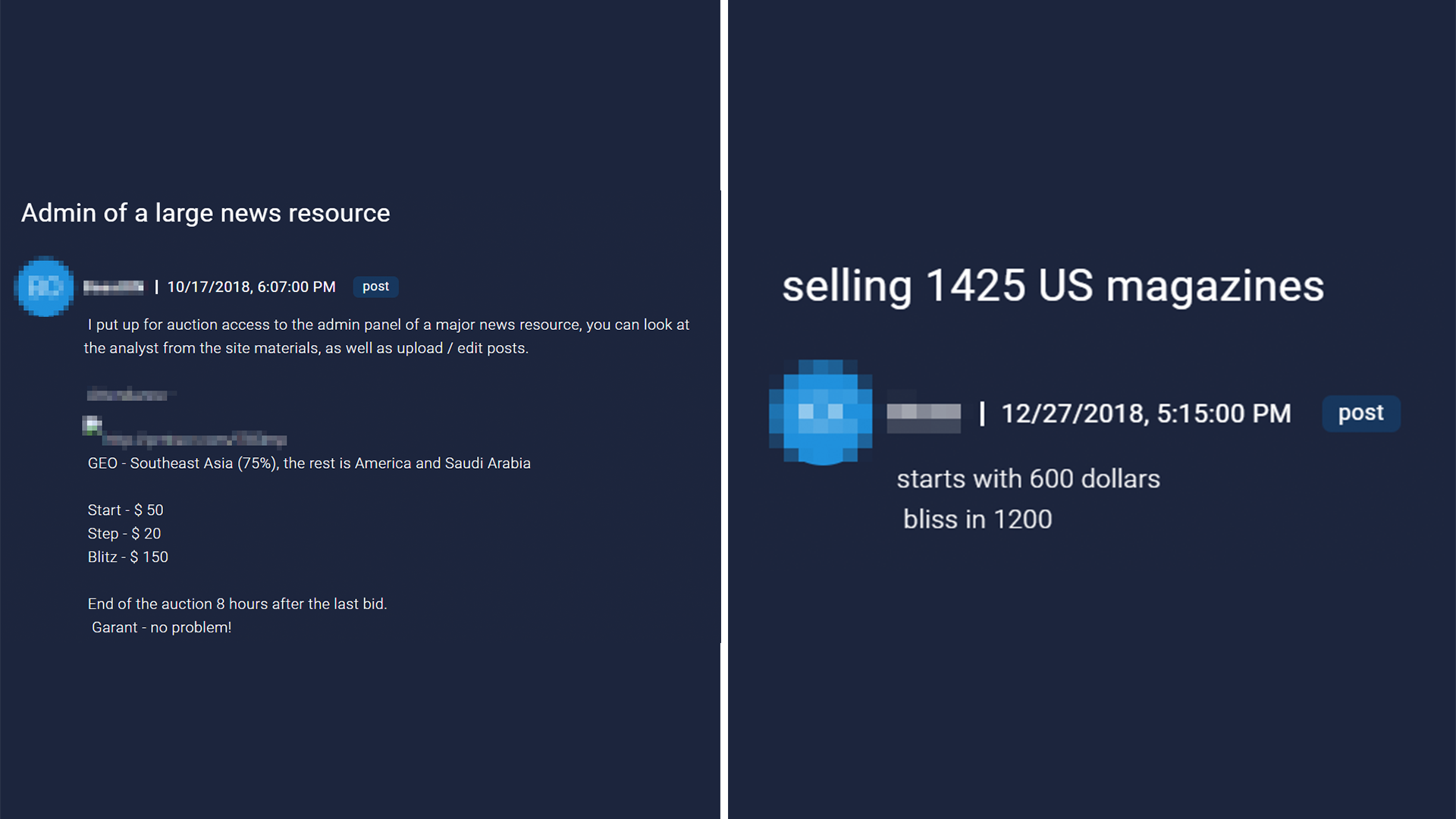
Listings on the hacker forum. Photos: Sixgill
Separate hackers on a Russian-language hacker forum have offered to sell access to the content management systems of bundles of news sites since October, notes Israeli threat intelligence firm Sixgill, which would give buyers the ability to edit or upload their own news stories. One offered access to 1,425 U.S. sites.
Why it matters: "We get a sense of urgency from looking at this stuff," said Alex Karlinsky, a intelligence expert at Sixgill. "It may seem like a small thing, but in this era of political bots and trying to influence opinion, this is another way to do that."
Details: The posts appeared on a predominantly Russian-language hacker forum where hackers frequently auction access to websites of all types.
- The U.S. site package, listed in October, started bidding at $600 with a buy-it-now option of $1,200.
- A second listing in December offered access to a centralized administration panel for a variety of news sites. Those sites were largely Southeast Asian, with Saudi and U.S. sites mixed in. Bidding on that started at $50, with an option to outright purchase at $150.
The hackers in both cases were well-established enough on the forum that the listings appear credible, said Karlinsky.
There does not appear to be a specific spike in sales of access to news agencies, said Karlinsky. Rather, the two listings covering the same ground were a coincidence brought about by the rise in listings of pre-hacked sites overall.
3. More shutdown fallout: Federal web certificates expire
More than 80 certificates from federal websites have expired during the shutdown, notes Marc Rogers, director of cybersecurity for Okta.
Certificates? One major protection for web users is a trusted third party that ensures your web browser is connecting directly to a web site. They call that a certificate.
- If a site lacks a valid certificate, a hacker can set up a computer in between you and the server, relaying your commands to the server and the responses back to you — eavesdropping or changing whatever they like.
- Major browsers now block users from connecting to sites whose certificates has lapsed.
Why it matters: "Consumers will either not be able to access certain sites or view them via a trusted browser," said Rogers.
4. Report: Poland joins march against Huawei
After Poland arrested a Huawei executive for espionage last week, the Wall Street Journal reports that Poland will join the U.S. in lobbying NATO nations to avoid Chinese telecommunications tech many nations link to espionage.
Meanwhile: Ren Zhengfei, the typically reclusive founder of Huawei, emerged Tuesday to tell reporters the company does not spy on behalf of China.
- He added praise for Donald Trump ("A great president," quotes Bloomberg). He did not announce any plans to intervene in the other major Huawei arrest in recent weeks: Meng Wanzhou, Ren's daughter and Huawei's CFO, is facing extradition to the U.S. from Canada for violating sanctions to Iran.
5. Odds and ends
- Former FTC chief technologist Lorrie Faith Cranor will now head Carnegie Mellon's Cylab Security and Privacy Institute. (Carnegie Mellon)
- Hackers can take over cranes, presumably construct whatever giant structure they'd like. (Forbes)
- The city of Del Rio, Texas, had to resort to pen and paper after a ransomware attack (ZDNet)
- Well-loved, mid-sized conference DerbyCon will shut down after 2019. (DerbyCon)
- Russia's only satellite telescope has stopped responding to commands. (Motherboard)
- All implementations of the networking protocol SCP since 1983 are impacted by a newly discovered security flaw. (ZDnet)
- Actual Pinkertons are suing the Wild West video game Red Dead Redemption 2 over its use of the brand name. (The Verge)
Codebook will see you Thursday.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.