Axios Codebook

November 27, 2018
Welcome to Codebook, Axios' cybersecurity newsletter. A special thank you to everyone who tried to convince me that I actually do like Thanksgiving foods. You're all still wrong.
If you've got tips or story ideas, I'd love to see. Just reply to this email.
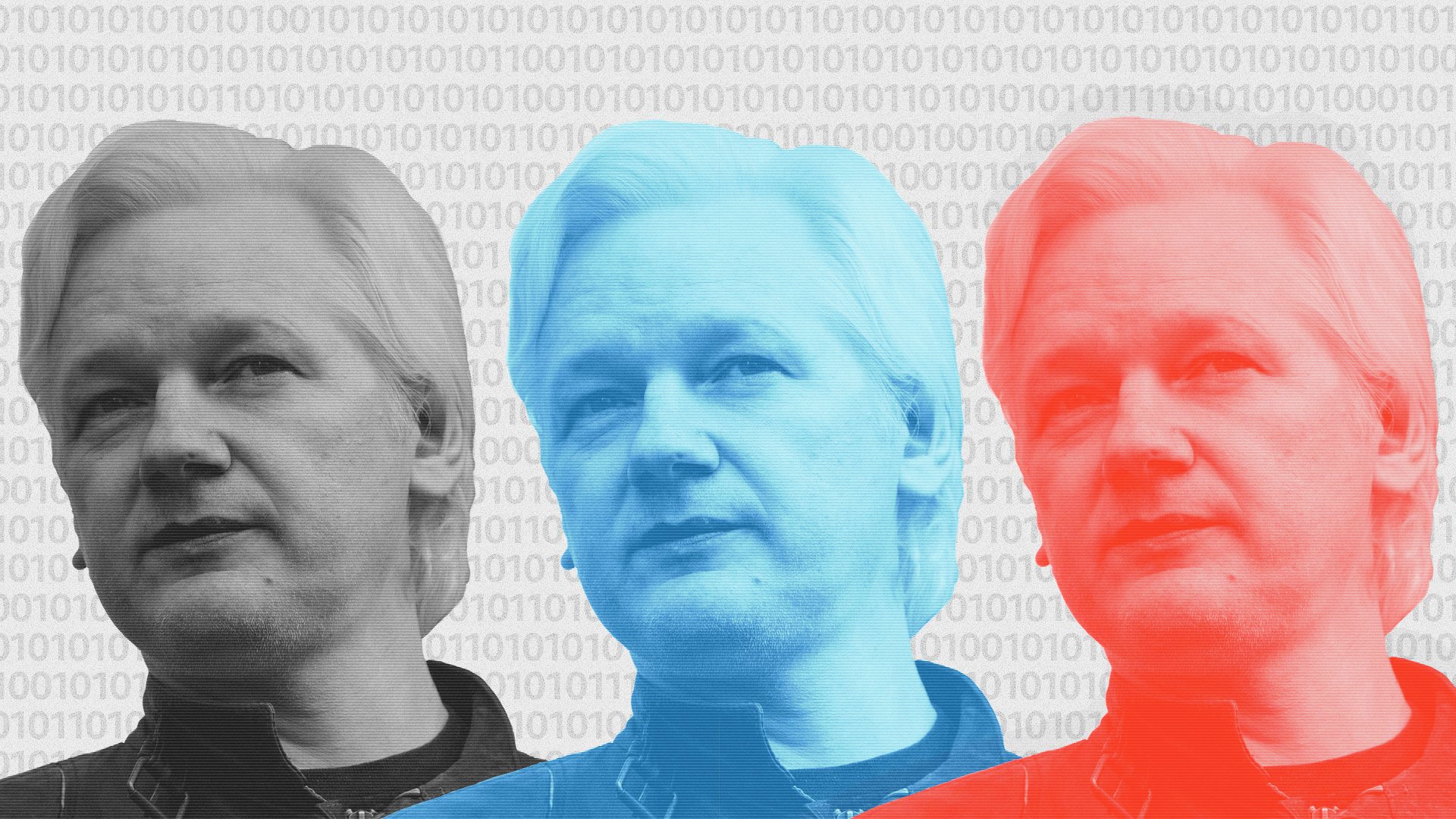
1 big thing: Why press fears on Assange charges are premature
llustration: Aïda Amer/Axios
A lot of journalists fear that putting Wikileaks honcho Julian Assange on trial — a prospect that looked more likely last week thanks to an inadvertent legal revelation — could be very bad for the free press.
My mom is worried, too: In my reporting in 2016, I received and published a bunch of leaked documents from Russia. If Assange is in trouble for doing that, I might be as well.
But, but, but: There's a good chance charges against Assange will have little to do with press freedom. Here's why saying otherwise might be jumping the gun:
- An errant line in a recent legal filing appears to have confirmed that sealed charges against Assange do exist, although the Department of Justice is still fighting releasing any details.
- Those unknown charges rattled journalists, who worry about setting a dangerous precedent.
And they could be an issue for any journalists who have handled leaks — including me. In my reporting in 2016, I received reams of documents from Russia. If Assange is in trouble for doing that, I logically might be as well.
- This is sometimes called the "New York Times problem." It's hard to punish WikiLeaks without punishing every news outlet that reported on the documents it released.
The intrigue: The DOJ almost certainly has facts not available to the public. And there's no good reason to assume that charges against Assange would just be about publishing documents.
Leaked documents show WikiLeaks may have taken several actions that moved it far afield from the realm of journalism. The organization:
- Hacked a website of an anti-Trump PAC and shared the ill-gotten password with the Trump campaign.
- Directed hackers to attack a specific target. While the request was brought to those hackers by someone other than Assange, they believed the messenger was an intermediary sent by Assange.
- Provided hackers with external support in the form of a search algorithm to sift through hacked documents.
Each of those instances could be viewed as either an outright violation of the Computer Fraud and Abuse Act or conspiracy to do so.
- Hacking the anti-Trump PAC website may actually be two crimes: trespassing into a computer and trafficking in the password.
Reporters don't get to break the law to create or investigate a story. "If you speed on the way to a story, you're still speeding," said Paul Rosenzweig, who teaches cybersecurity law at George Washington University School of Law. "You don't get a pass to rob a bank if you're going to write about robbing a bank."
The FBI has never contacted me about my role in the 2016 leaks. I assume that's at least in part because receiving leaked documents is not by itself a problem.
The bottom line: We don't know that the leaked documents paint an accurate picture of WikiLeaks' involvement in crimes. They do, however, at least suggest it may be worth waiting to see what the DOJ has before declaring a press emergency.
2. Australian opposition offers encryption compromise
A horse named Encryption after winning the Danehill Stakes at Flemington Racecourse on Sept. 15 in Flemington, Australia. Photo: Ross Holburt/Racing Photos via Getty Images
Mark Dreyfus, the Labor Party's shadow attorney general, offered a compromise to pass Australia's controversial encryption bill.
Why it matters: The Labor Party had been the last remaining hurdle in passing a bill giving the government the ability to circumvent unbreakable encryption.
Australia's approach had already been more restrained than what U.S. law enforcement had asked for, but it was still viewed as problematic by its critics.
Details: Dreyfus' compromise would allow only counterterrorism agencies to compel decryption.
The big picture: To many, Australia's bill would be the first domino to fall toward global regulation of encryption, including in the U.S. Critics say that kind of law is dangerous and is likely to introduce new ways for hackers to take over systems.
3. The FBI used fake FedEx site to foil fraudsters
The FBI used a fake FedEx website to obtain the internet address of cybercriminals, Motherboard reports.
Details: Motherboard unearthed the tactic from a 2017 warrant application.
- Scam artists impersonated the CEO from crane manufacturing firm Gorbel and sent false invoices to the accounting department, walking away with $82,000.
- The company noticed the fraudulent transaction and called in the FBI, who attempted to get the con artists to access a fake FBI website, designed to log the internet address being used by the criminals.
- The ploy didn't work. While the website was designed to produce error messages to coax criminals to connect to the site directly, rather than through a proxy server, the criminals didn't bite.
The FBI ultimately used a more traditional hacking technique to track the criminals.
Why it matters: The FBI has long used hacking methods to track cybercriminals, most famously targeting child pornographers. But it's not really clear what the ethics are of impersonating a U.S. company's brand.
4. Popular coding library hid cryptocurrency thief
The popular coding library event-stream hid code intended to break into the cryptocurrency wallet Copay. According to Copay, versions 5.0.2 through 5.1.0 incorporated that code.
What they're saying: "Users should assume that private keys on affected wallets may have been compromised, so they should move funds to new wallets," wrote Copay.
The malicious code was first flagged by Ayrton Sparling, a self-described California State University Fullerton computer science major, on GitHub.
A+ work.
5. Odds and ends
Paul Manafort arrives for a hearing at US District Court on June 15 in Washington. Photo: Mandel Ngan/AFP/Getty Images
- Baroness Trumpington, the former Bletchley Park transcriptionist who led the charge to posthumously pardon codebreaker Alan Turing for his conviction on homosexuality charges, has passed away. (BBC)
- The UK fined Uber a little under $500,000 for covering up a 2016 data breach. (The Guardian)
- Mexico used Pegasus spyware, made by an Israeli military contractor, to spy on journalists following the murder of another journalist. (New York Times)
- Consumer rights groups are targeting Google for GDPR violations. (Reuters)
- Six Flags is challenging Illinois' biometric privacy law, the toughest law in the nation. (The Verge)
- An alleged LinkedIn hacker will undergo psychiatric evaluation before trial. (CyberScoop)
- Amnesty International called for protests over Google's proposed censored Chinese search engine. (The Intercept)
- Report: Paul Manafort held secret talks with Julian Assange months before hacked Democratic emails were published. (Guardian)
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.