Axios Codebook

June 28, 2018
Welcome to Axios Codebook, the only cybersecurity newsletter that once had brunch in the same restaurant as John Tesh.
Quick sidenote to brag: Axios was named “Best Digital News Start-up” at the 2018 North American Media Awards. Feel free to respect Codebook more.
Tips? Just reply to this email.
1 big thing: A year after NotPetya, there's still a bear in the woods
Illustration: Sarah Grillo/Axios
National security advisor John Bolton met with Russian President Vladimir Putin Wednesday to work out the details of a summit between Putin and President Trump, now planned for July 16 in Helsinki. Bolton's meeting took place on a date that happened to be fraught with cyberwarfare significance.
Wednesday was the one year anniversary of NotPetya, a massively destructive cyberweapon the Trump administration attributed to Russia. The day before, Ukraine announced it saw the beginnings of a massive Russian cyberattack. But neither of those issues seemed to land in Wednesday's meeting.
Why it matters: Moscow's reliance on cyberwarfare — not just spying, but the destructive stuff — doesn't appear to be slowing. Experts wonder whether any Russia-U.S. summit can achieve much without grappling with that issue.
During the part of the meeting open to cameras, Bolton played down any strife between the U.S. and Russia. "U.S.-Russian relations are not in their best shape...I believe this is in large part the result of an intense domestic political battle inside the U.S," he said.
It's more than elections: Bolton is pinning the sour state of U.S.-Russia relations on the 2016 election and the controversies surrounding it. But even if you were to forget Russian involvement in the last election (and why would you do that?), Russia poses a broad spectrum of national and global security threats. In purely cybersecurity terms, the U.S. agenda can and should go farther.
- Russia's best known destructive attacks are in Ukraine. "But they are not only destructive in Ukraine," said John Hulquist, director of intelligence analysis at FireEye. He notes that the OlympicDestroyer malware sent to South Korea for the Olympics was likely Russian as well.
- The U.S. is at risk even when it isn't the one being attacked. NotPetya damaged systems worldwide, including in Russia, despite originating as an attack on Ukraine.
- "When Ukraine warns about cyber attacks, as they did on Tuesday, we should take notice, because NotPetya showed Russia is willing to inflict massive collateral damage in those attacks," said Andrea Limbago, chief social scientist at the cybersecurity firm Endgame.
NotPetya, remembered: There is a good chance we don't talk about NotPetya as much as we should. The firm Cybereason tallied damages NotPetya caused just for publicly traded companies and arrived at $1.2 billion. That number doesn't include individuals, private companies or governments. The actual scope of the damages is likely much higher.
For a sense of scale, the median hurricane does $1.8 billion total in damage.
- "Within the infosec community, we think of NotPetya as a game changer. But to the business community and government, it isn't viewed the same way," said Limbago.
Also a concern: crime. The Russian threat isn't just the Russian government. There's a thriving cybercrime ecosystem that rarely sees participants prosecuted or extradited. Moscow is "consistently harboring the most dangerous cybercriminals. It demands action until addressed," said John Carlin, former assistant attorney general for the Department of Justice’s (DOJ) National Security Division, and a current attorney at Morrison and Foerster.
The bottom line: "Russia has not slowed down since NotPetya," said Hulquist.
When Trump meets with Putin, U.S. safety will be better served by treating Russian cyberthreats as a serious danger than by dismissing them as a partisan issue.
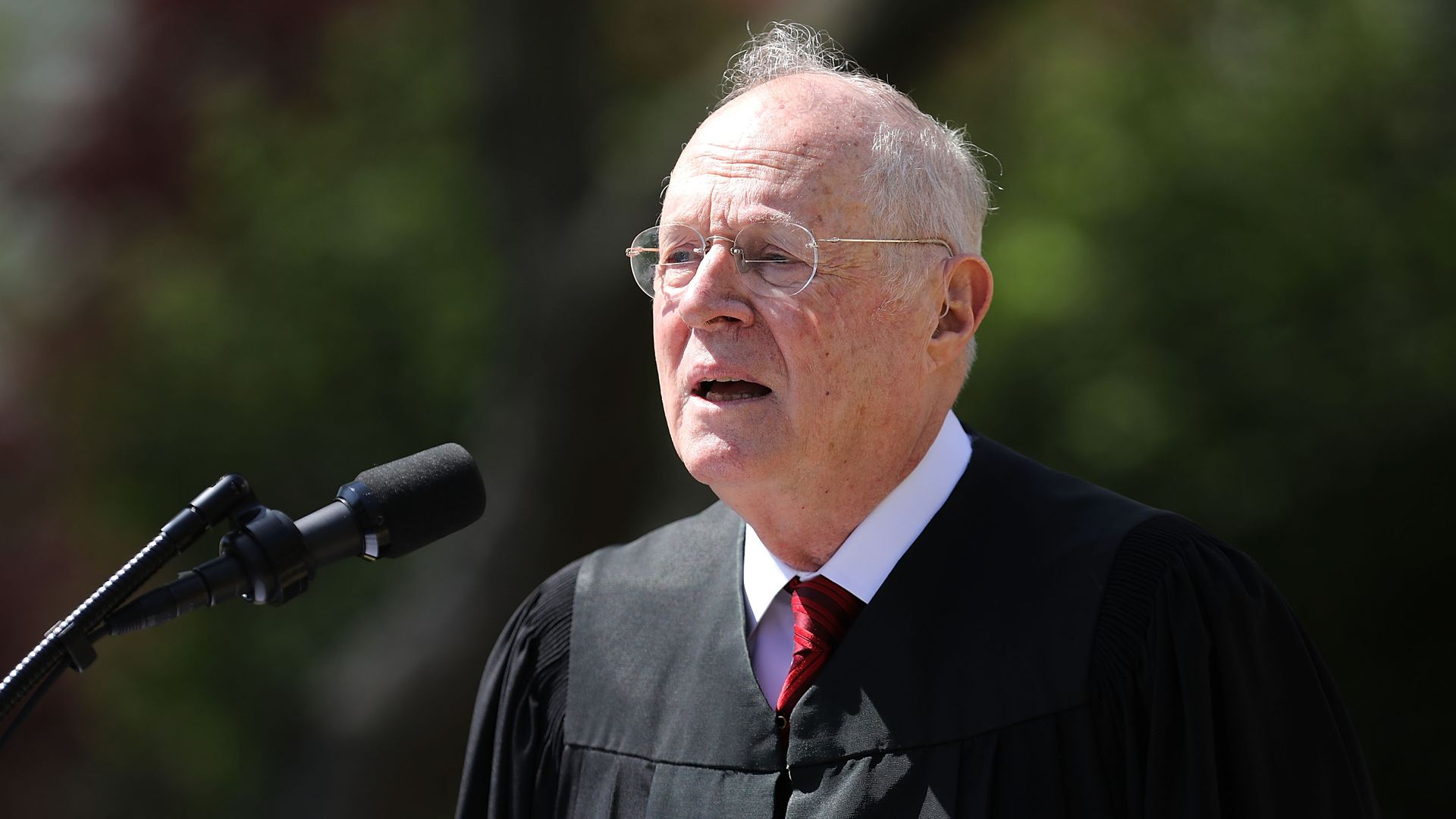
2. On communications privacy, Kennedy was never a key vote
Photo: Chip Somodevilla/Getty Images
Justice Anthony Kennedy, the U.S. Supreme Court's perennial swing vote, announced his retirement Wednesday. But according to Michelle Richardson, deputy director of the Center for Democracy and Technology's Freedom, Security, & Technology Project, Kennedy was never the swing vote in any of the "big 4" privacy cases he participated in.
The score board:
- Carpenter (2018): Voted for the losing side.
- Riley (2014): Unanimous.
- Jones (2012): Unanimous
- Kyllo (2001): Voted for the losing side.
Why not mattering actually matters: While a lot of things will change with a new court, the new justice might not make a huge dent in surveillance and communications privacy issues. "The nominee could be someone interested in giving law enforcement more authority and it wouldn’t matter," said Richardson.
And, if the nominee was the opposite, it wouldn't matter either.
3. Exactis had leaky data on nearly every American adult
Until notified by a security researcher, the Floridian marketing firm Exactis exposed the personal information of 340 million people online, unsecured. The leaky data was first reported by Wired.
But don't panic: Obviously, exposing that much information is not good. But the exact problem here — an unsecured database — would only yield data to someone who knew exactly where to look on the internet. While there are ways to search the internet for misconfigured databases, it's not exactly Google, and there's no evidence that any information was pilfered.
The details: The details, writes Wired, included contact information and "other highly personal characteristics for every name" ranging from "interests and habits to the number, age, and gender of the person's children." The data did not include Social Security or credit card numbers.
The discovery: Vinny Troia, the researcher, discovered the database earlier this month. He contacted the FBI and Exactis, and the firm has since secured its data.
4. Encrypted email sites downed by DDoS attacks
The encrypted email sites ProtonMail and Tutanota both fell victim to distributed denial of service attacks (DDoS) Thursday morning. Both have returned to full functionality. A DDoS attack floods a victim's server with so much traffic it crashes.
The details: It's unclear if the attacks were related. On Reddit, ProtonMail posted that "we have traced the attack back to a group that claims to have ties to Russia, and the attack is said to have been 500 Gbps, which would be among the largest DDoSes on record."
5. Odds and ends
- Huawei argues that the funding it provides for research at U.S. universities is not a national security threat. (Reuters)
- Ten EU nations signed an accord for their cybersecurity response teams to coordinate and share information. (SC Magazine).
- IEEE, the biggest research focused association for engineering and computer science, came out against encryption backdoors. (IEEE)
- Patch your Cisco ASA products now, warns Cisco. (ZDNet)
- A strange glitch sent a BBC reporter someone else's security camera footage. (Naked Security)
Codebook will return next week for a short week — Tuesday, but no Thursday.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.