Axios Codebook

June 27, 2019
Welcome to Codebook, a newsletter about cybersecurity, a topic mentioned twice in passing at last night's Democratic debates, and never by name.
Today's Smart Brevity: 1,103 words, ~4 minute read.
Story ideas? Feel free to reply to this email.
1 big thing: Iran's history of hacking and being hacked
Illustration: Aïda Amer/Axios
Given last week's flurry of U.S. cyberattacks against Tehran, Iran's history of retaliating with cyberattacks might raise a few eyebrows. But more concerning might be Iran's history of learning new strategies from other nations' cyberattacks.
The big picture: In 2009, Iran became the first known target of cyber warfare. Its history with cyber conflict is long, and could be used to inform how the current moment might play out.
Background: Iran shows an uncommon ability to learn from other nations' techniques and targeting, said Silas Cutler, reverse engineering lead at Chronicle. That's evidenced in how it adapted to Stuxnet, 2009 malware likely launched by the U.S. and Israel to disable the Iranian nuclear program.
- After Stuxnet, notes Cutler, Iran invested heavily in cyber activities.
- That resulted in the Shamoon malware, ultimately used to damage the Saudi-owned oil company Aramco in a 2012 attack widely believed to have been carried out by Iran.
- "I'm less worried about a retaliatory attack and more worried about them learning from our attacks and making them their own," said Cutler.
In fact, Stuxnet caused a fundamental change in how hackers operate in Iran.
- Hacker culture in Iran dates back to the turn of the millennium. Ashiyane, an Iranian security forum still used today, was founded in 2002.
- But the purposes of hacker forums in Iran changed after Stuxnet, said Cutler, moving from being a general subculture to a more patriotic one.
- To this day, the Iranian government uses hacker forums for recruitment whenever they need an emergency workforce.
Where it stands: More recently, said Adam Meyers of Crowdstrike, Iran has learned from Russia's operations against Ukraine in its current operations against Saudi Arabia and the UAE.
The intrigue: Unlike North Korea, which has mainly used disruptive cyberattacks to settle petty scores and generate revenue, Iran's disruptive cyberattacks have been more tactical, said Ben Read, senior manager for cyber-espionage analysis at FireEye.
- Iran responded by launching massive denial-of-service attacks against the U.S. financial sector in 2012, after the U.S. launched sanctions against Iran and only two years after Stuxnet was exposed.
- Those are remarkably similar to the current state of affairs, notes Read. The U.S. announced new sanctions against Iran this week following the cyber attacks last week.
- Iran can be petty, too. (It may have used Shamoon to attack Sheldon Adleson's Sands casino in response to comments he made.)
What's next: Iran largely stopped targeting the West after the Iran deal, but activity has re-emerged against the U.S. as tensions have escalated. That activity appears to be more for information gathering than to cause harm.
- The U.S. should be aware of Iran's techniques should they chose to retaliate, said Read, as just knowing what to look for can be enough to head off Iran's brand of attacks.
- "They can do bad stuff, but they aren't wizards," he said.
2. China on spying claims: I'm rubber, you're glue
After a report accused Chinese hackers known as APT 10 or Cloudhopper of breaching 10 global cell phone providers, the Chinese embassy responded by calling out U.S. cyber operations.
The big picture: The firm Cybereason, which first noticed the campaign it says it is highly confident is Chinese espionage, said China's aim was to compile call data on dissidents, military officials, spies and law enforcement agents across international borders.
China denies the allegations. But they did so in an unusual way, taking aim at specific U.S. espionage programs.
What they're saying: "I'm sure those who have long been following cybersecurity issues must still remember the PRISM program and have heard of the Equation Group," said Foreign Ministry spokesperson Geng Shuang at a Tuesday press conference, referencing a U.S. bulk surveillance program outlined in the Snowden documents and a vaunted espionage group believed to be part of the NSA. "They may also have known that certain country has been wantonly waging 'cyber war' against other countries."
To be clear: All countries spy, many, if not most countries use hacking as part of their spying, and spying with the intent of informing government decisions is generally considered more of a jaywalking infraction than felony on the global stage.
- Targeting dissidents is less acceptable to the Western liberal order.
- If China has any specific allegations of the U.S. hacking its systems, they can contact me at this email address.
3. Equifax's code downloaded more after breach
In 2017, Hackers entered Equifax using a vulnerability in the open source Apache Struts library. And, despite that being one of the largest and best publicized breaches in history, downloads of the vulnerable, unpatched Struts library increased.
Why it matters: The data, compiled in Sonatype's new State of the Software Supply Chain report, is emblematic of a bigger problem in open source software: People often chose out of date code long after security problems are discovered.
By the numbers: When the vulnerability in Struts was announced in March of 2017, the vulnerable code was downloaded 1.78 million times that month despite a patched version being available.
- The monthly rate was relatively constant through the announcement of the breach in September of that year.
- In October, downloads crossed 2 million a month for the first time.
- Between July and November of 2018, the last months Sonatype publish data for, that version of struts was downloaded more than 2 million times each month.
4. In case you missed last week
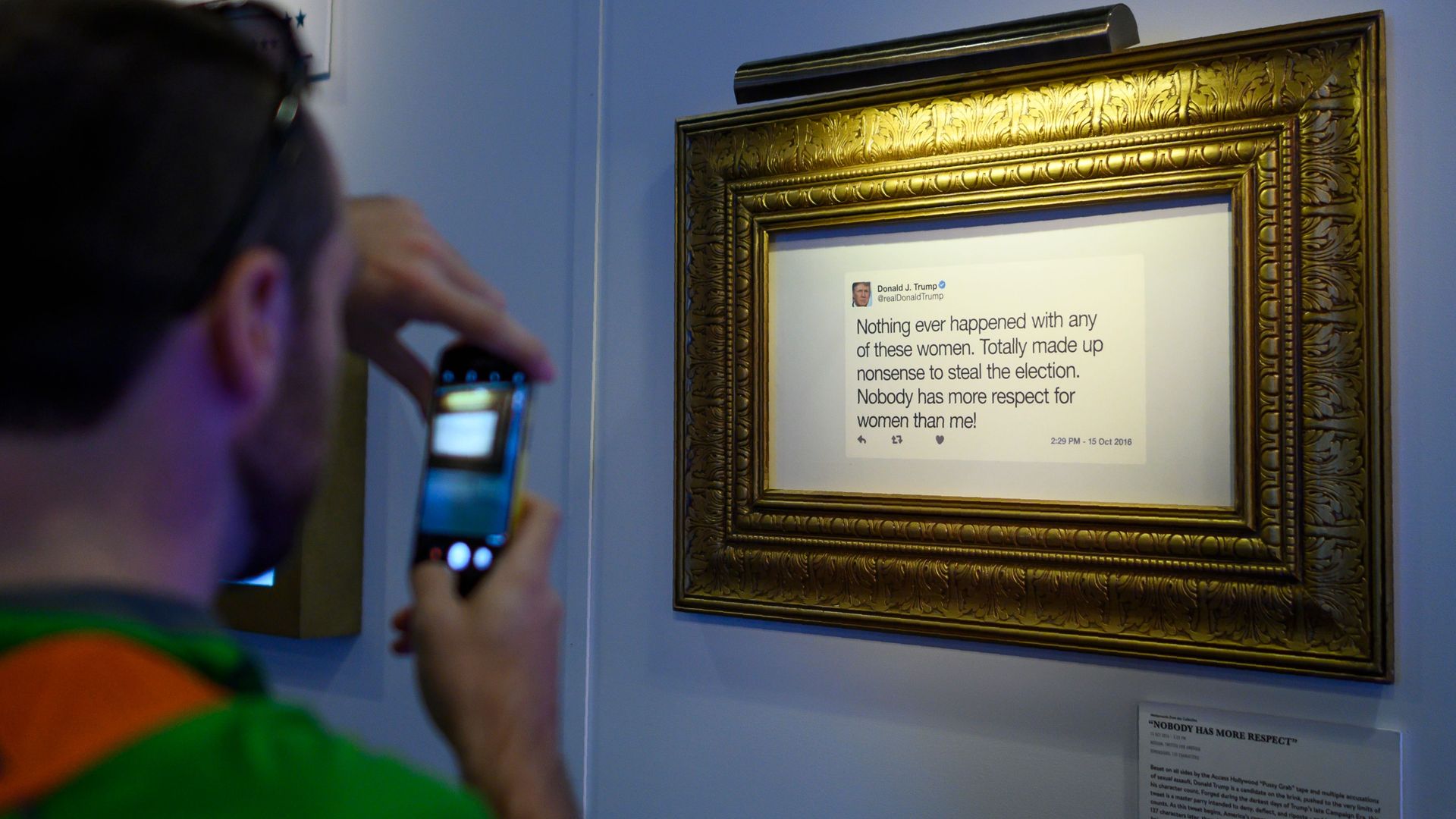
A gallery showing of President Trump's tweets sponsored by The Daily Show. Photo: Andrew Caballero-Renyolds/AFP via Getty Images
China will require an end to U.S. war on Huawei in trade talks: President Trump has, in the past, implied that all Huawei options can be negotiated, much to the chagrin of national security experts who feel trade and security should be kept in separate buckets. (Wall Street Journal)
- Intel, Micron and others have reportedly found ways to avoid labeling their products as American made, allowing them to continue selling to Huawei despite the pending export ban.
- Meanwhile, FedEx has sued to be let off the hook for exporting barred equipment to Huawei.
Trump to throw a "social media summit": Trump will hold a "social media summit" on July 11, accusing major platforms of "trying to rig the election" on the Fox Business Channel. (Wall Street Journal)
- While the right often complains about a litany of ways social media firms are censoring them, there isn't evidence of any specific political ideology being targeted by a major platform.
Ransomware attacks net $1.1 million in Florida cities: Over the course of about a week, Riviera Beach and Lake City, Florida each paid ransomware swindlers hundreds of thousands of dollars to recover encrypted files. (WUSF)
- Ransomware attacks on cities aren't anything new. Last year, Atlanta spent millions of dollars recovering from a similar attack and we don't know the two Floridian events in such a short time frame were more than a coincidence.
Facebook's failed to quash a data breach lawsuit. (Cyberscoop)
5. Odds and ends
- The Riltok banking trojan, once confined to Russia, is now targeting Europe. (Kaspersky)
- Google adds some new security bells and whistles to G-Suite. (Google)
- A deep dive on a gift card fraud group that attacked the Indian IT outsourcing firm Wipro. (RiskIQ)
- Global Cyber Alliance compiled some free tools that could bolster election security. (GCA)
- McAfee is suing former employees working at Tanium for theft of trade secrets. (Dark Reading)
- The former Senate aide who doxxed Republicans was sentenced to 4 years in prison. (Associated Press)
- Lots of people are trying to swindle cryptocurrency. (ZDNet, Wired, Bitdefender, BankInfoSecurity)
Codebook will return next week.
Sign up for Axios Codebook

Decode key cybersecurity news and insights. With Sam Sabin.